IoT Worm Threatens City Smart Lights
An IoT worm could hack all smart lights in a city, potentially crippling vital infrastructure. This poses a significant threat to a city’s functionality, impacting everything from traffic control to emergency response. We’ll explore the vulnerabilities, potential impacts, mitigation strategies, and even the technological advancements being made to prevent future attacks.
This comprehensive look at the issue will cover various aspects, including the potential weaknesses of different smart light systems, the cascading effects on city services, and the importance of proactive security measures. We’ll examine real-world scenarios, discuss mitigation strategies, and delve into the future of IoT security. The discussion will also address the critical need for public awareness and education about these threats.
Vulnerability Assessment: Iot Worm Could Hack All Smart Lights In A City
The recent threat of an IoT worm targeting smart light systems underscores the critical need for robust security measures. The interconnected nature of these systems, often overlooked in design phases, presents significant vulnerabilities. Addressing these vulnerabilities is paramount to prevent widespread disruption and ensure the safety and reliability of urban infrastructure.Smart light systems, despite their convenience, are frequently susceptible to exploitation by malicious actors.
The inherent design flaws, combined with a lack of security awareness, create pathways for an attack. This vulnerability assessment dives deep into potential entry points and methods of defense.
Potential Vulnerabilities in Smart Light Systems
Smart light systems, particularly those employing IP-based communication protocols, face numerous vulnerabilities. Weak authentication mechanisms, outdated firmware, and insufficient network segmentation can create entry points for attackers. These vulnerabilities are often compounded by the lack of regular security updates and patches.
Types of Smart Light Systems and Their Weaknesses
Different types of smart light systems, each with their own communication protocols and security measures, vary in their vulnerability profile. Wireless systems, for example, are often more exposed to eavesdropping and unauthorized access compared to wired systems. The communication protocols themselves can be flawed, lacking encryption or proper authentication. For instance, the use of unencrypted protocols like HTTP or MQTT significantly increases the risk of interception and data breaches.
Impact of Lack of Security Updates
The absence of regular security updates and patches is a major contributing factor to the vulnerability of smart light systems. Malicious actors can exploit known vulnerabilities in outdated firmware to gain unauthorized access to the system. The lack of timely updates leaves the systems vulnerable to known exploits, increasing the potential for widespread compromise. For example, if a critical vulnerability in the firmware is not addressed, it could allow an attacker to remotely control the lights or even gain access to the entire network.
Propagation of an IoT Worm Through a Network
An IoT worm could exploit vulnerabilities in a network of interconnected smart lights by leveraging the system’s communication channels. The worm would propagate through the network, spreading from one light to another, compromising each device in its path. A successful worm propagation could cause widespread outages and disrupt essential services relying on the smart lights. This could impact public safety, emergency services, and even commercial operations.
Comparison of Security Features of Different Smart Light Manufacturers
| Manufacturer | Authentication | Encryption | Firmware Updates | Network Segmentation |
|---|---|---|---|---|
| Company A | Basic, vulnerable to brute-force attacks | Weak encryption, susceptible to decryption | Occasional, delayed releases | Limited segmentation |
| Company B | Stronger authentication, multi-factor | Robust encryption | Regular and timely updates | Advanced segmentation |
| Company C | Medium strength, prone to dictionary attacks | Moderate encryption | Semi-regular updates | Standard segmentation |
Note: This table is a hypothetical comparison and does not represent specific manufacturers. The security features of each manufacturer can vary and are subject to change.
Impact on City Infrastructure

Smart city initiatives, relying heavily on interconnected systems, create vulnerabilities when individual components fail. Compromised smart lights, a seemingly minor issue, can have cascading effects throughout a city’s infrastructure, impacting critical services and daily life. The potential for disruption is significant, especially in a densely populated area.
Cascading Effects of Smart Light Compromise
The interconnected nature of smart city infrastructure means a failure in one area can ripple through other systems. A widespread compromise of smart lights, for instance, could lead to a variety of cascading effects, disrupting the functionality of various critical services. This interconnectedness can amplify the impact of seemingly isolated incidents, creating substantial challenges for the city’s overall resilience.
Impact on Traffic Control, Iot worm could hack all smart lights in a city
Traffic control systems often rely on smart lights for coordinated signal timing. A large-scale compromise could lead to unpredictable and chaotic traffic patterns. Signals might malfunction, causing gridlock and potentially increasing the risk of accidents. This disruption is especially problematic during peak hours and emergencies, where efficient traffic flow is essential. The lack of consistent signal timing can cause significant delays and strain on emergency response efforts.
For example, a coordinated attack on a major metropolitan area could cripple its transportation system, impacting productivity and daily routines.
Impact on Emergency Response
Emergency response services, such as ambulances and fire trucks, rely on clear visibility and well-functioning traffic signals. A significant failure of smart lights could impair their ability to navigate the city effectively, potentially delaying their response times to emergencies. This delay could have severe consequences for public safety. Consider the scenario of a major accident where emergency vehicles are hindered by malfunctioning traffic lights, increasing the risk of casualties.
Disruptions in emergency response could potentially lead to loss of life and significant property damage.
Imagine an IoT worm infiltrating a city’s smart lighting system, capable of controlling every single bulb. This terrifying scenario highlights the urgent need for robust security measures. To prevent such hacks, deploying AI code safety tools like those discussed in Deploying AI Code Safety Goggles Needed is crucial. The vulnerability in smart city infrastructure is real, and we need proactive measures to safeguard against such attacks on critical systems.
Impact on Public Safety
Public safety is directly affected by the visibility and functionality of city lights. A widespread failure of smart lights would create significant areas of darkness, potentially increasing crime rates and creating unsafe conditions for pedestrians and cyclists. The loss of visibility could make it harder to identify and apprehend criminals and contribute to a sense of insecurity among citizens.
A lack of well-lit public spaces could also deter citizens from utilizing them after dark, potentially increasing crime and social unrest.
Impact on Daily Life
The disruption caused by widespread smart light failure could significantly affect daily life. The loss of visibility and reliable traffic signals could cause substantial transportation delays, impacting businesses, schools, and other essential services. Furthermore, reduced visibility could create unsafe conditions for pedestrians and cyclists. A major blackout in a city’s smart lighting system would lead to widespread disruption and anxiety, impacting individuals’ daily routines and the smooth operation of the city.
Potential Consequences by Affected Service
| Affected Service | Potential Consequences |
|---|---|
| Traffic Control | Gridlock, increased accident risk, significant delays, strain on emergency response |
| Emergency Response | Delayed response times, increased risk of casualties, hindered navigation |
| Public Safety | Increased crime rates, unsafe conditions, reduced visibility, deterred use of public spaces |
| Daily Life | Transportation delays, unsafe conditions, reduced visibility, disruption of routines |
Mitigation Strategies
The potential for an IoT worm to compromise a city’s smart lighting network necessitates a robust and multifaceted approach to mitigation. This involves a layered defense strategy, encompassing secure communication protocols, centralized management, and regular security assessments. Failure to implement comprehensive mitigation measures could result in widespread outages, significant financial losses, and even public safety risks.A proactive security posture is crucial to prevent exploitation.
The following sections detail various mitigation strategies, ranging from implementing strong authentication to employing intrusion detection systems. Understanding these approaches is essential for safeguarding critical infrastructure like smart lighting systems.
Robust Authentication Protocols
Effective authentication is the cornerstone of secure systems. Strong passwords, multi-factor authentication (MFA), and role-based access control (RBAC) are critical components. This ensures that only authorized personnel or systems can access and control the smart lighting network. For example, implementing MFA requires users to provide multiple verification methods, such as a password and a one-time code sent to a mobile device, making unauthorized access significantly more difficult.
Regular Security Audits
Regular security audits are indispensable for identifying vulnerabilities before malicious actors exploit them. These audits should cover all aspects of the smart lighting system, including hardware, software, and communication channels. Penetration testing, a simulated attack, is often a crucial part of this process, helping to reveal potential weaknesses in the system’s defenses.
Intrusion Detection Systems (IDS)
Intrusion detection systems (IDS) are crucial for real-time threat monitoring. IDSs continuously monitor network traffic for suspicious activity, alerting administrators to potential intrusions. Different types of IDS, including signature-based and anomaly-based systems, can be employed to create a comprehensive security layer. Signature-based IDS relies on known attack patterns, while anomaly-based IDS detects deviations from normal network behavior, providing an additional layer of protection.
Centralized Management System
A centralized management system (CMS) for smart lights allows for coordinated control and response to threats. With a CMS, administrators can remotely monitor all devices, update firmware, and enforce security policies uniformly. This centralized approach simplifies the process of managing a large number of devices, making it easier to contain an attack should it occur. Furthermore, it allows for quick isolation of compromised devices, minimizing the potential impact of a worm infection.
Data Encryption and Secure Communication Channels
Data encryption and secure communication channels are essential for safeguarding sensitive data transmitted within the smart lighting network. Using encryption protocols like TLS/SSL for all communications is paramount to prevent eavesdropping and data breaches. This ensures that even if an attacker gains access to the network, the data itself remains unintelligible. Implementing secure communication channels protects the integrity and confidentiality of data exchanged between devices and the management system.
Layered Security Approach
A layered security approach is vital to defend against a wide range of threats. This involves implementing multiple security controls at different points in the system. For example, combining strong authentication with a robust IDS, and integrating a CMS for centralized management, provides a layered defense. This multi-layered approach significantly reduces the attack surface, making it much harder for malicious actors to compromise the system.
A layered approach also enables swift response and isolation in the event of a breach.
Real-World Scenarios

A city’s smart lighting network, while offering energy efficiency and enhanced safety, presents a tempting target for malicious actors. A sophisticated IoT worm, exploiting vulnerabilities in these interconnected systems, could cause widespread disruption and potentially severe consequences. Understanding potential scenarios is crucial for developing effective mitigation strategies.
Potential Attack Vectors and Impact
Smart lighting systems are susceptible to various attack vectors. These range from simple denial-of-service attacks to more complex breaches compromising critical city infrastructure. A comprehensive understanding of these vectors is essential to anticipate and counter potential threats.
| Attack Vector | Potential Impact |
|---|---|
| Denial-of-Service (DoS) | Disruption of lighting services, potentially affecting public safety and visibility, particularly in critical areas like intersections or emergency response zones. |
| Data Exfiltration | Unauthorized access to sensor data, potentially revealing sensitive information about traffic patterns, pedestrian movement, or energy consumption. |
| Malicious Control | Manipulation of light patterns to cause confusion, disorientation, or even psychological distress. This could be used to hinder public safety or disrupt normal operations. |
| Data Injection | False data insertion into the system, potentially affecting the accuracy of traffic flow analysis, energy management, or even weather monitoring systems. |
| Ransomware | Encrypting the city’s smart lighting system and demanding payment for decryption, potentially causing significant financial and operational losses. |
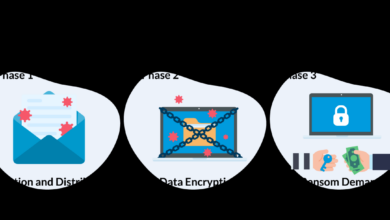
Sequence of Events: Infection to Compromise
A typical sequence of events begins with a compromised device within the network. This initial breach can then spread through vulnerable connections, exploiting known or unknown vulnerabilities in the software or firmware of other connected devices.
- Initial Infection: A compromised device, perhaps through a phishing attack or a previously unknown vulnerability, becomes infected with the IoT worm.
- Lateral Movement: The worm exploits network vulnerabilities to spread to other smart light fixtures, leveraging the interconnected nature of the system.
- System Compromise: The worm gains control over a critical number of devices, potentially impacting the entire city’s lighting infrastructure.
- Malicious Activity: The attacker, having gained control, can now execute various malicious actions, such as manipulating light patterns or initiating a denial-of-service attack.
City Response Strategies
Proactive measures are essential to mitigate the impact of such attacks. A multi-layered approach encompassing vulnerability assessment, incident response plans, and security awareness training is vital.
That terrifying thought of an IoT worm potentially hacking every smart light in a city is truly unsettling. While this sort of vulnerability is a real concern, it’s also worth considering how legal protections like the Department of Justice Offers Safe Harbor for MA Transactions Department of Justice Offers Safe Harbor for MA Transactions might influence future development and security protocols.
Ultimately, preventing such a widespread hack of smart city infrastructure remains a critical challenge.
- Regular Vulnerability Assessments: Continuously assessing the system for known and unknown vulnerabilities is critical to proactively identify and patch weaknesses.
- Incident Response Plan: Developing a detailed plan outlining steps to be taken in the event of an attack, including isolation procedures, containment strategies, and communication protocols.
- Security Awareness Training: Educating personnel on recognizing and reporting suspicious activity, ensuring that human error is minimized.
- Network Segmentation: Dividing the network into smaller, isolated segments can limit the impact of a breach.
- Robust Authentication: Implementing strong authentication mechanisms to protect against unauthorized access to the system.
Lessons from Similar Incidents
Various instances of security breaches in IoT systems offer valuable lessons. Analysis of these incidents provides insights into successful and unsuccessful strategies.
- Successful Security Measures: Examples of cities or organizations that have successfully secured their IoT systems through strong security protocols and frequent vulnerability assessments can serve as a benchmark for best practices.
- Unsuccessful Attempts: Examining cases where security measures failed to prevent an attack can provide insights into vulnerabilities that need to be addressed, such as weak passwords or inadequate security training.
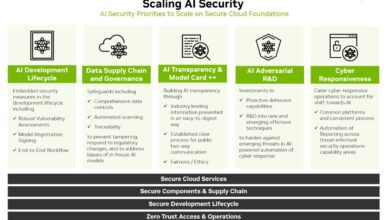
Technological Advancements

The Internet of Things (IoT) is rapidly evolving, bringing both unprecedented opportunities and significant security risks. As more devices connect to the network, the potential attack surface expands, necessitating a proactive and innovative approach to security. This section delves into promising advancements in IoT security technology, highlighting the crucial role of machine learning and emerging secure communication methods.
Potential Advancements in IoT Security Technology
A multitude of advancements are shaping the future of IoT security. These include the development of more robust encryption protocols, enhanced authentication mechanisms, and the implementation of decentralized architectures to mitigate the impact of a single point of failure. The goal is to create a more resilient and secure ecosystem where devices can communicate and interact without compromising sensitive data.
The Role of Machine Learning in Identifying and Responding to Malicious Activity
Machine learning algorithms are increasingly important in detecting and responding to malicious activity in IoT systems. By analyzing vast amounts of data from connected devices, these algorithms can identify unusual patterns and behaviors indicative of cyberattacks. This proactive approach allows for rapid identification and mitigation of threats, preventing widespread damage. For example, a machine learning model trained on normal device activity can flag deviations that signal an intrusion, potentially preventing a city-wide smart lighting outage.
Emerging Technologies for Secure Communication and Data Management
Emerging technologies like blockchain and homomorphic encryption are showing promise in bolstering IoT security. Blockchain’s inherent transparency and immutability can enhance the security and trust in data transactions. Homomorphic encryption allows for data processing without revealing its content, further protecting sensitive information. These advancements, coupled with enhanced security protocols, will play a pivotal role in creating a secure and trustworthy IoT environment.
Evolution of IoT Security Over the Past Decade
| Year | Key Advancements | Impact |
|---|---|---|
| 2013-2014 | Initial focus on device-level security, basic encryption protocols. | Limited protection against basic attacks, significant vulnerabilities remained. |
| 2015-2017 | Emergence of cloud-based security solutions, development of industry standards. | Improved visibility and centralized management, but cloud vulnerabilities were still a concern. |
| 2018-2020 | Increased focus on end-to-end security, emphasis on security by design. | Development of more resilient systems, better integration of security measures. |
| 2021-Present | Integration of machine learning and AI for threat detection, exploration of advanced encryption methods. | Proactive threat detection and response, significant potential for preventing large-scale attacks. |
Public Awareness and Education
The increasing reliance on interconnected devices in smart cities creates a fertile ground for malicious actors targeting vulnerable infrastructure. A crucial component of mitigating the risks of IoT worm attacks is educating the public about these threats and empowering them to protect themselves and their communities. Effective public awareness campaigns are not just about raising awareness, but about providing actionable knowledge and fostering a culture of cybersecurity within the city.Understanding the complexities of IoT security and its implications for the average citizen is paramount.
This understanding must transcend mere awareness to provide practical strategies for identifying and responding to potential threats. Citizens need to be equipped with the knowledge to protect their personal data and contribute to the overall security posture of the smart city.
Strategies to Raise Public Awareness
Public awareness campaigns should be multifaceted, using various channels to reach diverse demographics. Educational materials should be presented in clear, concise, and easily understandable language.
- Targeted Educational Programs: Schools and community centers should host workshops and seminars on IoT security. These programs should cover fundamental concepts like network security, data privacy, and recognizing phishing attempts. The workshops can be tailored for different age groups, ensuring content is age-appropriate and engaging.
- Public Service Announcements (PSAs): Short, impactful PSAs aired on local television, radio, and social media platforms can effectively disseminate critical information. The PSAs should highlight the potential consequences of negligence in IoT security and showcase simple steps to enhance security.
- Community Forums and Events: Organize community forums and events focused on smart city technology. These events should include interactive exhibits demonstrating the vulnerabilities of IoT devices and showcasing practical security measures. This approach promotes engagement and encourages open discussions.
Educational Campaigns to Empower Citizens
Educational campaigns should empower citizens with practical knowledge and actionable steps to identify and respond to potential threats. These campaigns should not only provide theoretical information but also provide real-world scenarios.
- Interactive Online Platforms: Develop user-friendly online platforms offering interactive tutorials, quizzes, and guides on IoT security best practices. These platforms should use clear visuals, videos, and real-life examples to explain complex concepts in a more engaging way.
- Mobile Applications: Develop mobile applications providing users with instant access to security tips, alerts about potential threats, and interactive exercises to reinforce their understanding.
- Simulations and Games: Create engaging simulations and games that put citizens in the role of a hacker or a victim of a cyberattack. This hands-on approach can be more effective in driving home the importance of vigilance and security awareness.
Importance of User Education on Security Best Practices
Understanding the potential impact of user negligence is crucial in a smart city environment. Security best practices extend beyond individual devices to encompass the interconnected ecosystem.
- Strong Passwords: Emphasize the importance of strong, unique passwords for all IoT devices. Highlight the use of password managers and multi-factor authentication.
- Regular Updates: Educate users about the necessity of keeping their IoT devices and software updated. Explain how updates patch security vulnerabilities.
- Device Management: Promote the use of device management solutions to control access to devices and monitor activity. Encourage users to set up appropriate access controls to minimize the attack surface.
Challenges in Educating the Public
Effective public awareness campaigns face significant challenges, particularly when dealing with complex technical issues.
- Technical Jargon: The use of technical jargon can hinder understanding and engagement. Educational materials need to avoid technical language and use simple, understandable language.
- Low Technological Literacy: Not all citizens possess a high level of technological literacy. Educational programs must adapt their approach to cater to a diverse range of technical proficiency levels.
- Maintaining Interest: Sustaining public interest in cybersecurity topics can be challenging. Creative and engaging methods are needed to maintain attention and encourage active participation.
Message to Inform the Public
“Protecting your smart city devices is everyone’s responsibility. Simple steps like using strong passwords, keeping software updated, and being cautious about suspicious emails and links can make a significant difference. Your vigilance is a key component in ensuring the safety and security of our interconnected world.”
That terrifying thought of an IoT worm potentially hacking all the smart lights in a city is chilling, isn’t it? It highlights the vulnerabilities in interconnected systems. Thankfully, security researchers are also finding weaknesses in cloud services like Microsoft Azure’s Cosmos DB. This vulnerability, detailed in Azure Cosmos DB Vulnerability Details , could potentially impact the systems controlling those same smart lights, raising the stakes of a potential city-wide outage.
The interconnected nature of these systems is both amazing and frightening.
End of Discussion
The potential for an IoT worm to compromise a city’s smart lights highlights the critical need for robust security measures. Addressing vulnerabilities, implementing proactive mitigation strategies, and fostering public awareness are essential steps to ensure the safety and reliability of these crucial systems. This discussion emphasizes the interconnectedness of technology and the need for a layered security approach.
The future of smart cities depends on our ability to secure these systems against such threats.
Essential FAQs
What are the most common communication protocols used in smart light systems?
Common protocols include Zigbee, Z-Wave, and Wi-Fi. These protocols vary in their security features, making some more vulnerable to attack than others.
How can a city respond to a smart light system attack?
A multi-faceted response is necessary, involving isolating infected systems, restoring functionality to critical systems, and conducting a thorough post-attack review to identify and fix vulnerabilities.
What role does data encryption play in preventing IoT worm attacks?
Encryption protects data transmitted between smart lights and control systems, making it much harder for attackers to intercept and manipulate the information.
What are some examples of successful security measures in similar IoT systems?
Successful examples include using strong passwords, regular software updates, and robust authentication methods. These preventative measures can significantly reduce the likelihood of an attack.