Log Management and SIEM for Enterprise Cybersecurity
Log management and SIEM overview using both for enterprise cybersecurity sets the stage for a deep dive into securing modern businesses. This overview will explore the crucial role of centralized log collection and analysis in identifying and responding to threats, from the basics of log management and SIEM to practical implementation strategies.
We’ll cover the various sources of security logs, different collection methods, and the core functionalities of a SIEM system. Real-world use cases, including intrusion detection and compliance, will be highlighted. Understanding log analysis techniques, incident response procedures, and best practices for implementation will be essential to building a robust security posture. Finally, we’ll look ahead to future trends in this ever-evolving field.
Introduction to Log Management and SIEM
Log management is the cornerstone of enterprise cybersecurity, acting as a crucial first line of defense against malicious activities. It involves the systematic collection, storage, and analysis of logs generated by various systems and applications within an organization. Effective log management provides valuable insights into system behavior, enabling proactive identification and response to potential threats. This process is essential for understanding and addressing vulnerabilities, ensuring compliance, and improving overall security posture.Security Information and Event Management (SIEM) builds upon log management by providing a centralized platform for collecting, analyzing, and correlating security logs.
SIEM systems go beyond simply storing logs; they actively monitor them for suspicious patterns and events, often using advanced analytics and machine learning to identify potential threats in real-time. This sophisticated approach empowers security teams to quickly detect and respond to security incidents, significantly reducing the impact of breaches.
Centralized Log Collection and Analysis
Centralized log collection and analysis are critical for modern enterprises. Disparate systems generating logs across various departments and applications often create an overwhelming and fragmented view of security events. A centralized system consolidates these logs, providing a unified perspective on the entire security landscape. This consolidated view enables quicker detection of anomalies, malicious activities, and other critical security events, leading to more efficient incident response.
SIEM Architecture
The architecture of a SIEM system involves the collection and analysis of logs from various sources. A typical architecture includes the following components:
- Log Sources: This includes servers, applications, network devices, security appliances, and other systems that generate logs. Examples include web servers, databases, firewalls, intrusion detection systems, and endpoint security agents.
- Log Collectors: These agents collect logs from various sources and forward them to a central repository. They are often deployed on the individual systems to streamline data collection.
- Log Repository: This is the central storage location for collected logs. A robust repository ensures data integrity and accessibility for analysis. Databases or specialized log management systems are commonly used for this purpose.
- SIEM Platform: This is the core component that analyzes logs, identifies patterns, and generates alerts. It also provides a user interface for monitoring, reporting, and responding to security events.
- Alerting and Response System: The SIEM system notifies security personnel of potential threats through alerts, allowing them to investigate and respond quickly. Automated responses, such as blocking malicious IP addresses, can also be integrated.
A well-designed SIEM architecture ensures efficient log collection and analysis, enabling organizations to identify and address security risks proactively.
Illustrative Architecture Diagram
+-----------------+ +-----------------+ +-----------------+
| Web Server | --> | Log Collector | --> | Log Repository |
+-----------------+ +-----------------+ +-----------------+
| Application | --> | Log Collector | --> | Log Repository |
+-----------------+ +-----------------+ +-----------------+
| Database | --> | Log Collector | --> | Log Repository |
+-----------------+ +-----------------+ +-----------------+
| Firewall | --> | Log Collector | --> | Log Repository |
+-----------------+ +-----------------+ +-----------------+
|
V
+-----------------+
| SIEM Platform |
+-----------------+
| |
| | Alerts and Responses
| |
+-------+
|
V
+-----------------+
| Security Team |
+-----------------+
This diagram illustrates the flow of logs from various sources (web servers, applications, databases, firewalls) to a central log repository.
The SIEM platform analyzes the logs to identify potential security events and generate alerts, which are then acted upon by the security team.
Log Sources and Data Collection
A critical aspect of any robust enterprise security strategy hinges on the ability to collect and analyze security logs from various sources. Understanding the diverse origins of these logs, the formats in which they’re stored, and the methods for aggregating them is paramount. This allows for a comprehensive view of potential threats, enabling proactive incident response and effective security posture management.
Log Source Identification
Security logs originate from a wide range of sources within an organization, each providing valuable insights into system activity. Servers, applications, and network devices all generate logs detailing events like user logins, file access, network traffic, and system errors. For example, web servers log user requests and errors, while firewalls log network intrusions and attempted breaches. Properly identifying and categorizing these logs is the first step toward effective threat detection.
Log Formats and Transmission Protocols
Logs are formatted in various ways, impacting their analysis and usability. Common formats include CSV (Comma Separated Values), JSON (JavaScript Object Notation), and XML (Extensible Markup Language). These formats define how data elements are structured within a log entry. Transmission protocols, such as Syslog, are crucial for moving these logs to a central repository. Syslog, for instance, is a standardized protocol used for routing and managing logs across networks.
Log Collection and Aggregation Methods
Collecting logs from diverse sources requires a well-defined strategy. Centralized log management systems, often coupled with SIEM (Security Information and Event Management) solutions, aggregate logs from various sources, regardless of their format. This aggregation allows for correlation of events and analysis of potential threats. Log collection tools use various methods to collect data, such as agents that run on individual systems or network taps that capture network traffic.
Comparison of Log Collection Tools
| Tool | Features | Pros | Cons |
|---|---|---|---|
| Splunk | Powerful search and analysis capabilities, supports various data sources, provides dashboards and visualizations, allows for custom scripting. | Excellent for complex analysis, strong visualization tools, scalable to large environments. | Can be expensive, steep learning curve for complex configurations. |
| Elasticsearch, Logstash, Kibana (ELK Stack) | Open-source, highly scalable, supports various data formats, allows for real-time data processing and indexing, flexible architecture. | Cost-effective for smaller organizations, customizable, supports real-time analysis. | Requires more technical expertise to set up and manage compared to some commercial tools. |
| Graylog | Open-source, versatile log management and analysis platform, includes features for real-time log processing, alerting, and dashboards. | Good balance of features and cost-effectiveness, supports a wide range of data sources. | May require more configuration for complex use cases. |
| Fluentd | Open-source data collector and forwarder, highly configurable, supports various data formats and protocols. | Flexible and highly configurable, ideal for integrating with other systems, easy to integrate with other tools in the ecosystem. | Requires more expertise for complex implementations, may not offer the same level of out-of-the-box analysis features as other tools. |
Each tool in the table possesses strengths and weaknesses, and the optimal choice depends on the specific needs and resources of an organization.
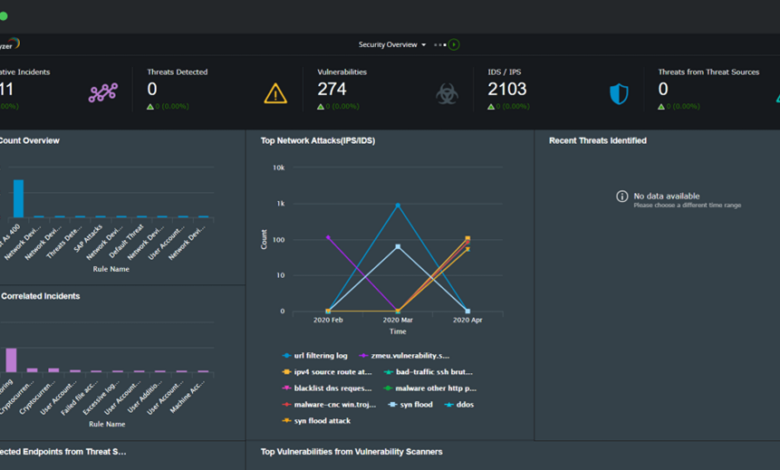
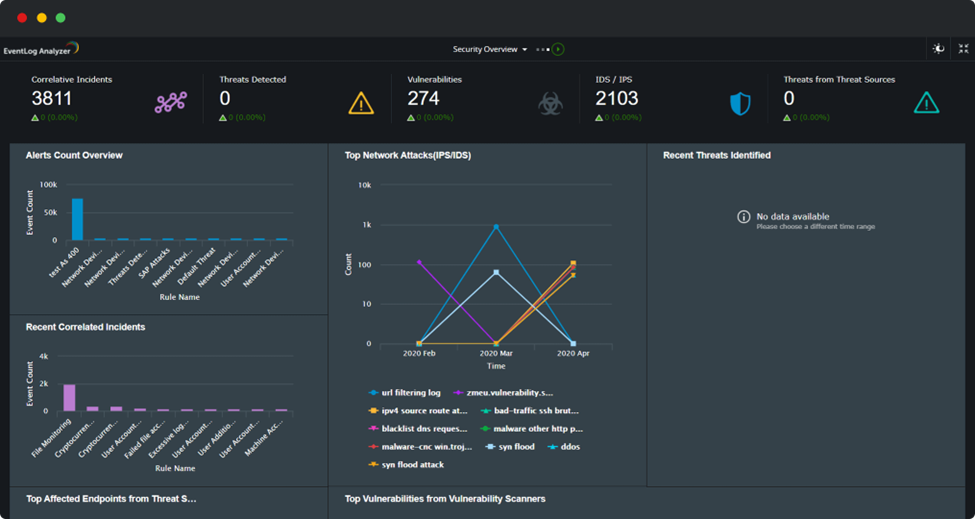
SIEM Functionality and Use Cases: Log Management And Siem Overview Using Both For Enterprise Cybersecurity
Security Information and Event Management (SIEM) systems are critical for modern enterprise cybersecurity. They act as a central nervous system, collecting and analyzing security logs from various sources to identify threats and vulnerabilities. This allows organizations to proactively address potential issues and maintain a robust security posture.SIEMs are not just reactive tools; they are integral to a proactive security strategy.
By aggregating and analyzing security data, SIEMs enable organizations to understand potential threats, identify patterns, and respond swiftly to incidents. This proactive approach minimizes the impact of security breaches and strengthens the overall security framework.
Core Functionalities of a SIEM
SIEM systems possess several core functionalities that enable effective threat detection and response. These include log aggregation, correlation, and analysis, each playing a vital role in building a comprehensive security picture. Log aggregation collects security logs from various sources, such as firewalls, intrusion detection systems, and applications. Correlation analyzes these aggregated logs to identify relationships and patterns between different events.
Analysis interprets these patterns to determine the potential significance of an event and to classify it as a threat or benign activity.
Threat Detection and Response
SIEMs significantly enhance an organization’s ability to detect and respond to security threats. By analyzing logs from various sources, SIEMs can identify suspicious activity, such as unauthorized access attempts, malware infections, and data breaches. Once a threat is detected, SIEMs can automatically trigger alerts, allowing security teams to respond quickly and effectively. This rapid response minimizes the potential damage and impact of security incidents.
Real-World Use Cases
SIEM systems are crucial for various enterprise cybersecurity use cases. For instance, intrusion detection is facilitated by identifying malicious activity patterns in network traffic logs, which is critical for early threat identification and prevention. Vulnerability management leverages SIEMs to monitor and analyze systems for known vulnerabilities, which is essential for proactively addressing security gaps. Finally, compliance requirements, such as PCI DSS or HIPAA, can be effectively managed by using SIEM to monitor activities and ensure adherence to regulations.
By correlating various events, SIEM systems can identify suspicious activities that could lead to non-compliance.
Potential Security Alerts and Events
- Suspicious login attempts from unusual IP addresses or user accounts.
- High volume of failed login attempts for a particular account or IP address.
- Unusual file access or modification patterns, especially for critical files or directories.
- Significant increases in network traffic or bandwidth usage from specific sources.
- Malicious code execution attempts detected by antivirus or intrusion detection systems.
- Anomalies in user behavior, such as unusually high numbers of access attempts to sensitive data or applications.
These alerts, identified and analyzed by a SIEM system, are essential for early detection of potential threats and enable proactive responses, which in turn protects critical systems and sensitive data.
Log Analysis Techniques and Procedures
Unraveling the secrets hidden within log files is crucial for effective cybersecurity. Log analysis isn’t just about reading; it’s about deciphering patterns, anomalies, and ultimately, identifying potential security threats. This process requires a structured approach that combines technical expertise with a deep understanding of the organization’s systems and processes.
Log management and SIEM are crucial for enterprise cybersecurity, providing a comprehensive view of events and potential threats. However, vulnerabilities like those found in Azure Cosmos DB, detailed in Azure Cosmos DB Vulnerability Details , highlight the need for robust security measures beyond basic log analysis. Ultimately, a strong log management and SIEM strategy is key to defending against a wide range of threats.
Common Log Analysis Techniques for Identifying Security Incidents, Log management and siem overview using both for enterprise cybersecurity
Various techniques exist to uncover malicious activities within log data. These techniques leverage different approaches, from simple pattern recognition to sophisticated statistical analysis. Understanding these methods empowers security analysts to proactively identify and respond to security incidents.
- Pattern Recognition: Regular expressions and other pattern-matching tools are fundamental to log analysis. Analysts identify suspicious sequences of events, such as unusual login attempts or repeated failed access attempts. For example, a sudden spike in failed login attempts from a specific IP address might indicate a brute-force attack.
- Statistical Analysis: Identifying deviations from expected behavior using statistical methods can highlight anomalies. By analyzing the frequency and distribution of events, analysts can pinpoint outliers and unusual patterns. For example, a sudden surge in the volume of network traffic from a particular source might signal a distributed denial-of-service (DDoS) attack.
- Correlation Analysis: Correlating seemingly unrelated events to uncover a larger incident is a critical technique. Analyzing logs from different sources (firewalls, intrusion detection systems, web servers, etc.) allows analysts to connect events like a series of failed login attempts with unusual network activity. This holistic view provides a clearer picture of the attack.
Methods for Analyzing Log Data to Identify Patterns and Anomalies
Effective log analysis involves exploring various methods to discover meaningful patterns and anomalies within the collected data. This exploration requires a combination of automated tools and manual analysis, often guided by pre-defined rules and thresholds.
Log management and SIEM (Security Information and Event Management) are crucial for any enterprise’s cybersecurity strategy. Understanding these systems helps identify threats and vulnerabilities, but modern threats demand more. For instance, deploying AI code safety tools, like those described in Deploying AI Code Safety Goggles Needed , is becoming increasingly important to proactively prevent vulnerabilities in code.
Ultimately, a comprehensive approach that combines strong log management and SIEM with cutting-edge AI tools is key to maintaining a robust cybersecurity posture.
- Rule-Based Analysis: Pre-defined rules and criteria are applied to the log data. These rules can be based on known attack signatures, suspicious user behaviors, or thresholds for specific events. For example, a rule could trigger an alert if a user attempts to access sensitive data outside of normal working hours.
- Anomaly Detection: This method identifies deviations from expected behavior in log data. Machine learning algorithms and statistical models can learn normal patterns and flag events that fall outside these patterns. For example, if a system typically logs a certain number of successful login attempts per hour, an anomaly detection system would flag a significantly higher or lower count.
- Behavioral Analysis: Understanding typical user and system behavior is key. By analyzing historical data, security analysts can identify normal patterns and flag deviations. For instance, if a user suddenly starts accessing files they haven’t accessed before, this might indicate suspicious activity.
Steps in a Log Analysis Workflow
A systematic workflow is essential for efficient and effective log analysis. This process involves various steps, from initial data ingestion to reporting and incident response.
- Data Ingestion: Collecting logs from various sources (servers, applications, network devices) into a centralized repository. This step ensures that all relevant information is gathered and stored for analysis.
- Filtering: Selecting the specific logs relevant to the analysis task. Filtering based on time, source, event type, or other criteria reduces the volume of data and focuses on the important information.
- Correlation: Connecting seemingly unrelated events to uncover a broader security incident. This step allows analysts to understand the full scope and context of the event.
- Reporting: Summarizing the findings and presenting them in a clear and actionable format. Reports should include details of the identified incidents, recommendations for remediation, and potential impact on the organization.
Log Analysis Process Flowchart
[A flowchart would visually represent the process, starting from data collection and ending with incident response. It would clearly illustrate each step, including filtering, correlation, analysis, and reporting.]
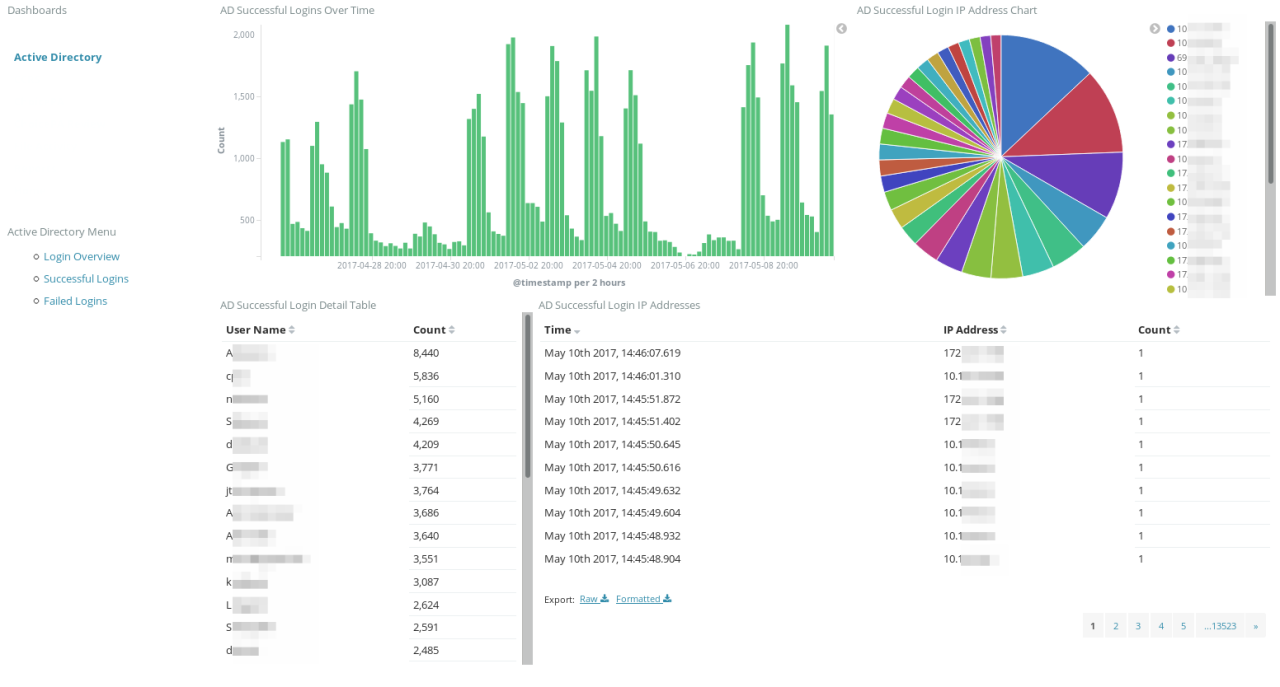
Security Incident Response with Log Management and SIEM
Log management and Security Information and Event Management (SIEM) systems are crucial components in a robust security incident response plan. They provide the detailed insights needed to quickly identify, contain, and resolve security incidents, minimizing damage and recovery time. By aggregating and analyzing logs from various sources, SIEM systems allow security teams to correlate events, detect anomalies, and respond proactively to threats.
This allows for a more effective and streamlined incident response process.The ability to quickly identify and contain security incidents is paramount in today’s threat landscape. SIEM and log management provide the essential tools for effective incident response, enabling security teams to react swiftly and efficiently. This detailed analysis allows for more accurate threat assessment, faster containment procedures, and ultimately, a more secure environment.
Investigating and Containing Security Incidents
SIEM systems act as a central hub for collecting and analyzing security logs. By correlating events across different systems, SIEMs can identify patterns and anomalies that might indicate malicious activity. This allows for faster detection of potential incidents, enabling swift action to contain the threat. For example, a sudden surge in failed login attempts from a specific IP address, coupled with unusual file access patterns on a particular server, might indicate a compromise.
A SIEM system can quickly identify these correlated events, triggering alerts and providing the necessary context for investigation.
Identifying Compromised Systems Using Log Analysis
Log analysis is a key element in isolating compromised systems. By examining logs from various systems, such as servers, firewalls, and endpoints, security analysts can identify unusual activities that might indicate a breach. For example, unusual network traffic patterns, unauthorized access attempts, or suspicious file modifications can all be identified using log analysis. The crucial step is understanding the normal baseline activity for each system.
Deviation from this baseline is often a strong indicator of compromise.
Creating Incident Reports Using SIEM Data
SIEM systems provide a wealth of data that is critical for creating comprehensive incident reports. These reports need to be clear, concise, and actionable, detailing the steps taken to investigate, contain, and resolve the incident. A well-structured incident report will typically include: the date and time of the incident, a description of the observed events, the systems affected, the steps taken to contain the incident, the root cause analysis, and the corrective actions implemented to prevent future incidents.
A structured template can ensure consistency and completeness in these reports.
Key Log Sources for Incident Response
- System Logs: System logs from servers, workstations, and other devices provide valuable information about system activity, including login attempts, file access, and application errors. This information is crucial for detecting unauthorized access and identifying suspicious behavior.
- Network Logs: Network logs from firewalls, routers, and intrusion detection/prevention systems record network traffic patterns. These logs are essential for identifying unusual network connections, suspicious traffic, and potential intrusions.
- Application Logs: Application logs capture activity related to specific software applications. Analyzing these logs can reveal anomalies in application usage, such as unauthorized access attempts or data exfiltration.
Implementing Log Management and SIEM in Enterprises
Log management and Security Information and Event Management (SIEM) systems are crucial for modern enterprise cybersecurity. Implementing these solutions effectively requires careful planning, thorough selection, and ongoing maintenance. This section details the key considerations for successfully integrating and utilizing these powerful tools within a corporate environment.
Considerations for Implementation
Implementing a log management and SIEM solution is not a simple task. Careful planning and consideration of various factors are essential for a successful deployment. These factors include aligning the chosen solution with the organization’s existing infrastructure, security policies, and data governance practices. Understanding the volume and types of logs generated by different systems within the enterprise is critical for selecting the right solution and ensuring its scalability.
Selection of Log Management and SIEM Tools
Choosing the right log management and SIEM tools is a critical step in the implementation process. Factors such as scalability, integration capabilities, reporting features, and vendor support should be carefully evaluated. Consider the specific security needs of the enterprise, including the types of threats the organization is most vulnerable to, and select tools capable of detecting and responding to those threats.
- Scalability: The solution should be capable of handling the increasing volume of logs generated over time. A solution that cannot adapt to future growth can become a significant bottleneck and hinder its effectiveness.
- Integration Capabilities: The ability to seamlessly integrate with existing systems is crucial. Integration reduces manual data entry and ensures consistency in data collection and analysis.
- Reporting Features: The reporting capabilities of the tool must align with the enterprise’s reporting needs and provide actionable insights for security analysts.
- Vendor Support: A reliable vendor with strong technical support is vital for resolving issues and ensuring the long-term viability of the solution.
- Cost-Effectiveness: The total cost of ownership (TCO) should be evaluated, including software licenses, hardware, maintenance, and training costs.
Maintaining and Upgrading a SIEM System
Maintaining and upgrading a SIEM system is an ongoing process. Regular updates are essential to keep the system current with the latest security threats and vulnerabilities. Proactive maintenance minimizes downtime and ensures the system continues to function optimally. Implementing robust monitoring and alerting mechanisms allows for quick identification of potential problems.
- Regular Updates: Security threats evolve constantly. Maintaining the latest security signatures and threat intelligence updates is critical for detecting new attacks.
- Monitoring and Alerting: Monitoring the SIEM system’s performance is vital to identify and address potential issues before they escalate. Alerting mechanisms should be well-defined and responsive to ensure quick action on identified threats.
- Data Backup and Recovery: Implementing a robust data backup and recovery strategy is essential for maintaining the integrity of critical data in case of system failures or data loss events.
- Staff Training and Knowledge Retention: Providing ongoing training and support for security analysts using the SIEM system is crucial for maximizing its effectiveness.
Checklist for Successful Implementation
A well-defined checklist can significantly increase the likelihood of a successful log management and SIEM implementation. This checklist should cover all aspects of the project, from initial planning to ongoing maintenance.
| Step | Action |
|---|---|
| 1 | Assessment: Identify log sources, data volume, and security needs. |
| 2 | Selection: Evaluate potential solutions based on criteria such as scalability, integration, and cost. |
| 3 | Implementation: Deploy the chosen solution and configure integrations with existing systems. |
| 4 | Testing: Validate the system’s functionality and performance with realistic data loads. |
| 5 | Training: Equip security personnel with the necessary skills to utilize the system effectively. |
| 6 | Monitoring: Establish continuous monitoring and alerting procedures to track system health and security events. |
| 7 | Maintenance: Regularly update the system, backup data, and address any issues. |
Security Best Practices and Considerations

Log management and SIEM systems are crucial for enterprise cybersecurity, but their effectiveness hinges on robust security practices. Implementing strong security measures for log data ensures its integrity, confidentiality, and availability, protecting valuable insights and preventing potential breaches. Effective security practices also help organizations meet compliance requirements and respond to security incidents efficiently.Proper security measures safeguard log data from unauthorized access and manipulation, while regular audits ensure the systems are functioning as intended and meeting established security standards.
This proactive approach is essential for maintaining trust and compliance in today’s digital landscape.
Log management and SIEM are crucial for enterprise cybersecurity. They provide a comprehensive view of activities, helping identify threats and vulnerabilities. For instance, recent developments like the Department of Justice Offers Safe Harbor for MA Transactions ( Department of Justice Offers Safe Harbor for MA Transactions ) highlight the importance of strong security measures. Ultimately, robust log management and SIEM systems are essential for navigating the ever-evolving cyber landscape.
Securing Log Data and Maintaining Integrity
Robust security practices are paramount to maintaining the integrity of log data. This involves a multi-layered approach that addresses storage, access, and processing.
- Data Encryption: Encrypting log data both in transit and at rest is a fundamental security practice. This ensures that even if unauthorized individuals gain access to the storage, the data remains unintelligible. Examples include using industry-standard encryption algorithms like AES and TLS for secure transmission. Implementing robust key management practices is equally important to prevent unauthorized decryption.
- Access Control: Implementing strict access control measures is vital to limit access to log data. Principle of least privilege should be adhered to. This means granting users only the necessary permissions to perform their tasks. Role-based access control (RBAC) systems provide a structured way to manage user permissions, limiting access to sensitive log data only to authorized personnel.
- Data Validation and Integrity Checks: Implementing mechanisms for validating and checking the integrity of log data is crucial. This includes verifying data source authenticity and ensuring the data hasn’t been tampered with during collection or storage. Hashing techniques, such as MD5 or SHA-256, can be used to verify the integrity of log files.
Compliance Requirements
Meeting industry-specific compliance regulations is essential for organizations handling sensitive data. Log management and SIEM systems play a critical role in ensuring compliance.
- Data Retention Policies: Organizations must establish and adhere to clear data retention policies for log data, ensuring compliance with regulations such as GDPR, HIPAA, and PCI DSS. These policies dictate how long log data should be stored and the procedures for securely deleting outdated information. Failure to comply with these policies can result in significant penalties.
- Audit Trails and Logging: Maintaining comprehensive audit trails is often a regulatory requirement. These records provide a detailed history of actions performed on the log management and SIEM systems, enabling organizations to track changes, identify potential issues, and demonstrate compliance.
- Data Security Standards: Adhering to established data security standards, like NIST Cybersecurity Framework, ensures that organizations are implementing best practices for log data management. These standards provide guidelines for securing log data, ensuring compliance, and protecting sensitive information.
Securing Log Data Storage
Robust security measures are essential to prevent unauthorized access to log data stored in various locations. This includes physical security of data centers, network security, and access controls.
- Physical Security Measures: For on-premises log data storage, implementing physical security measures, such as access control, surveillance, and environmental controls, is crucial. This protects the physical infrastructure housing the data.
- Network Security: Implementing strong network security protocols, such as firewalls and intrusion detection systems, is essential for preventing unauthorized access to log data stored on servers or cloud storage. Secure network configurations, including proper firewall rules, are necessary to protect against unauthorized access.
- Secure Storage Solutions: Selecting and implementing secure storage solutions for log data is crucial. Consider cloud-based solutions that provide built-in security features, such as encryption and access control. Ensure proper encryption protocols are employed for cloud-based data storage.
Regular Auditing of Log Management and SIEM Systems
Regular audits are vital for maintaining the effectiveness and integrity of log management and SIEM systems. They help identify potential vulnerabilities, ensure compliance, and optimize performance.
- System Configuration Audits: Regular audits of system configurations ensure the security settings are up-to-date and align with established security policies. These audits help to prevent misconfigurations that can expose sensitive data.
- Data Integrity Audits: Data integrity audits verify that the log data is accurate, complete, and hasn’t been tampered with. These audits help ensure the reliability of the data for analysis and incident response.
- Security Incident Response Audits: Audits of the security incident response process ensure that the organization is prepared to effectively handle security incidents detected through log analysis. This includes evaluating the effectiveness of incident response procedures.
Future Trends and Developments
The field of log management and Security Information and Event Management (SIEM) is constantly evolving, driven by advancements in technology and the ever-increasing complexity of cyber threats. This evolution necessitates continuous adaptation and innovation in our approaches to data collection, analysis, and response. Staying ahead of the curve requires understanding emerging trends and proactively integrating them into our security strategies.Cloud computing’s influence on log management and SIEM is profound, and this influence will only grow.
Centralized logging and analysis within cloud environments present unique opportunities and challenges. Effective log management must be adaptable to the dynamic nature of cloud-based infrastructure and its diverse architectures.
Emerging Trends and Technologies
The future of log management and SIEM is marked by several key trends. These include the increasing use of artificial intelligence (AI) and machine learning (ML) for automated threat detection and analysis, the rise of serverless architectures and the need for robust, scalable log collection strategies, and the integration of zero trust security principles into SIEM solutions. Furthermore, the growing demand for improved user experience and intuitive dashboards is also driving innovation in the field.
Impact of Cloud Computing
Cloud environments introduce new dimensions to log management and SIEM. The distributed nature of cloud deployments necessitates robust log aggregation and correlation strategies across various cloud services. Centralized management of logs from virtual machines, containers, and serverless functions is crucial. Security information and event management solutions need to adapt to these diverse environments, ensuring seamless integration and efficient data analysis.
Cloud-native SIEM solutions are gaining traction, designed specifically to handle the unique characteristics of cloud-based infrastructure.
Advancements in Log Analysis Techniques and Tools
Log analysis techniques are constantly evolving, with a strong emphasis on automation and intelligence. Advanced analytics, including anomaly detection, predictive modeling, and natural language processing (NLP), are increasingly integrated into log management and SIEM solutions. These tools empower security teams to identify subtle patterns and anomalies that might be missed by traditional methods. For example, NLP can be used to analyze security logs containing human language, like emails or chat messages, to uncover malicious activity.
Forecast for the Evolution of Log Management and SIEM in the Next Five Years
Within the next five years, we can anticipate significant advancements in log management and SIEM. Expect increased automation in threat detection and response, powered by AI and ML. Integration with other security tools and platforms, such as vulnerability management systems, will become more seamless. The rise of cloud-native solutions will continue, further simplifying deployment and management in cloud environments.
Finally, the focus on user experience and intuitive dashboards will continue, empowering security teams with more efficient and effective tools for threat analysis.
Last Word
In conclusion, log management and SIEM are critical components of a modern enterprise cybersecurity strategy. By centralizing log data and leveraging advanced analysis tools, organizations can significantly improve their ability to detect and respond to threats. This comprehensive overview has provided a foundational understanding, equipping you to navigate the complexities of log management and SIEM in a dynamic security landscape.
Essential FAQs
What are the key differences between log management and SIEM?
Log management focuses on collecting and storing logs, while SIEM adds the crucial element of analysis and correlation to identify patterns and threats. SIEM builds upon log management by providing tools to detect and respond to security events.
How can I choose the right log management and SIEM tools for my enterprise?
Consider factors like the volume and variety of logs generated, your budget, technical expertise, and the specific security threats your organization faces. Thorough research and vendor comparisons are essential to make the right choice.
What are some common security alerts and events that a SIEM can identify?
SIEMs can identify a wide range of events, including failed login attempts, unauthorized access, malware activity, suspicious network traffic, and data breaches. The specific alerts depend on the configuration and the tools used.
How does cloud computing impact log management and SIEM?
Cloud environments introduce new complexities for log management and SIEM. Centralized log collection and analysis are still crucial, but tools and strategies must adapt to the distributed nature of cloud-based resources.