Majority Consumers Ignoring Mobile Security
Majority consumers are ignoring mobile security, creating a dangerous landscape for personal data. This lack of awareness exposes users to a multitude of threats, from malware to phishing scams, all lurking within seemingly harmless apps and websites.
This post delves into the reasons behind this alarming trend, examining consumer behavior, the perceived ease of use of mobile devices, and the role of clear communication from developers. We’ll also explore the consequences of neglecting security, including financial and reputational damage, and suggest potential solutions.
Understanding the Scope of the Issue
Mobile security is a critical yet often overlooked aspect of our digital lives. While awareness has increased in recent years, a significant portion of consumers remain vulnerable to a multitude of threats. Understanding the nature and scope of these risks is paramount to mitigating potential harm and safeguarding personal information.Mobile devices have become indispensable tools, offering convenient access to information, communication, and entertainment.
This accessibility, however, comes with inherent risks. Consumers are exposed to a complex web of threats, often unaware of the dangers lurking in seemingly innocuous apps, websites, and even seemingly safe public Wi-Fi networks.
Mobile Security Threats
Mobile security threats encompass a wide range of malicious activities designed to compromise user data and devices. These threats can manifest in various forms, ranging from subtle infiltration to outright theft of sensitive information.
It’s a bit of a bummer, but a lot of people are overlooking mobile security. This is especially concerning given recent reports of vulnerabilities, like the ones detailed in the Azure Cosmos DB Vulnerability Details. This alarming news highlights the critical need for better mobile security awareness, and emphasizes how easily vulnerable data can be compromised if users aren’t careful.
The majority of consumers are still ignoring the very real threats to their data and devices. Azure Cosmos DB Vulnerability Details is a great resource for understanding the specifics.
- Malware: Malicious software, such as viruses, spyware, and ransomware, poses a significant threat. These programs can infiltrate devices through various means, including infected downloads, malicious links, and compromised apps. They can steal personal information, disrupt device functionality, or even hold data hostage for ransom.
- Phishing: Deceptive tactics are frequently employed to trick users into revealing sensitive information. Phishing attacks often involve fraudulent emails, messages, or websites that mimic legitimate entities. Victims may unknowingly provide usernames, passwords, credit card details, or other confidential data.
- Scams: Sophisticated scams exploit human vulnerabilities and psychological manipulation. These scams can take various forms, from fraudulent investment opportunities to lottery scams, and often target unsuspecting users with promises of large rewards or urgent requests for personal information.
Exposure Vectors
Consumers are exposed to these threats through a variety of channels. Understanding the pathways through which these threats infiltrate our lives is crucial for effective defense.
- Apps: Many malicious programs are disguised as legitimate apps, waiting for unsuspecting users to download them. Users may be enticed by free offers or attractive features, unknowingly installing programs that compromise their device’s security and privacy.
- Websites: Compromised or malicious websites can deliver malware or phishing attacks. Users may unknowingly click on links or visit websites that contain hidden threats, leading to data breaches or device infections.
- Public Wi-Fi: Public Wi-Fi networks are often unsecured, making them prime targets for attackers. Hackers can intercept data transmitted over these networks, stealing sensitive information or installing malware on connected devices.
Common Misconceptions
Several misconceptions surround mobile security, contributing to the vulnerability of consumers.
- Security software is sufficient: While security software can provide a layer of protection, it’s not a foolproof solution. Users must exercise caution and awareness, as even robust security software cannot prevent all threats.
- Only sophisticated users are at risk: Anyone using mobile devices can be a target. Regardless of technical expertise, users are vulnerable to various threats, and awareness of these risks is crucial.
- Mobile security is not a priority: Many individuals prioritize convenience over security, potentially overlooking the risks associated with using their devices.
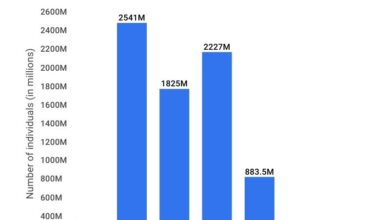
Frequency of Mobile Security Incidents
A comprehensive analysis of mobile security incidents is essential for understanding the scale of the problem. The frequency of various incidents varies, influenced by factors such as user behavior, security measures, and technological advancements.
| Incident Type | Frequency (Estimated) |
|---|---|
| App Downloads with Malware | High |
| Phishing Messages Received | Very High |
| Compromised Accounts | Moderate to High |
| Data Breaches | Moderate |
| Public Wi-Fi Attacks | Low to Moderate (depending on security measures) |
Identifying Consumer Behaviors
Mobile security is a critical yet often overlooked aspect of our digital lives. Understanding consumer behavior in this area is paramount to developing effective strategies for promoting safer practices. Consumers often prioritize convenience and ease of use over security, leading to a gap between best practices and actual implementation. This gap, in turn, fuels the vulnerabilities exploited by cybercriminals.The complexities of mobile security extend beyond a simple “on/off” switch.
Consumer behaviors are shaped by various factors, including age, income, technical proficiency, and even cultural norms. Understanding these nuances is crucial for tailoring security awareness campaigns and developing personalized solutions. We must also analyze how consumers interact with mobile security features, such as updates and two-factor authentication, to pinpoint areas where education and simplification are needed.
Security Practices Across Demographics
Different demographics exhibit varying levels of security awareness and adoption of security measures. Younger generations, for example, may be more comfortable with technology but may lack the experience to recognize sophisticated phishing attempts. Older generations, on the other hand, may require more straightforward and visually appealing explanations of security measures. Similarly, income levels can influence the perception of security risks, with those with lower incomes potentially being more susceptible to scams targeting financial accounts.
Common Patterns of Lack of Security Awareness
Several recurring patterns indicate a lack of security awareness among mobile users. A prevalent pattern is the tendency to ignore security updates, prioritizing immediate functionality over potential vulnerabilities. Another common pattern is the reluctance to use two-factor authentication (2FA), often perceived as an inconvenience rather than a crucial security measure. Furthermore, a significant portion of users fail to recognize the legitimacy of security warnings and alerts.
These behaviors, when combined, create a significant security vulnerability.
Consumer Interaction with Mobile Security Features
Consumers often interact with mobile security features in a superficial way. Many users simply download and install security apps without fully understanding their purpose or how to use them effectively. Similarly, the implementation of two-factor authentication (2FA) often proves challenging. Consumers may find the extra step inconvenient or forget to utilize the 2FA prompt. Moreover, users often ignore or dismiss security warnings and prompts, leading to potential breaches.
Factors Influencing Consumer Decisions
Several factors influence consumer decisions regarding mobile security. Convenience is a significant driver, with users often prioritizing ease of use over the adoption of robust security measures. Cost is another influential factor, where the perceived value of security may be outweighed by perceived costs, such as the time needed to implement security measures. Furthermore, trust in the provider of security software or services is a critical factor in consumer adoption.
Lack of trust in security features or warnings can lead to inaction.
Perceived Mobile Security Risks by Demographics
| Demographic | Perceived Risk of Malware | Perceived Risk of Phishing | Perceived Risk of Account Hijacking |
|---|---|---|---|
| Young Adults (18-25) | Moderate | High | Moderate |
| Middle-Aged Adults (35-55) | Low to Moderate | Moderate | Low |
| Seniors (65+) | Low | High | Low |
| High-Income Individuals | High | High | High |
| Low-Income Individuals | Moderate | High | Low |
This table illustrates a potential correlation between demographics and perceptions of mobile security risks. It highlights that while general concerns exist, the specific priorities and anxieties surrounding mobile security vary significantly. This variation underscores the importance of tailored security awareness campaigns.
Exploring the Reasons Behind Ignoring Security
Mobile security often feels like a chore, a necessary evil in the digital age. While awareness campaigns and technological advancements exist, a significant portion of users continue to overlook crucial security measures. This lack of vigilance isn’t necessarily malicious; rather, it’s a complex interplay of factors rooted in user perception, practicality, and the design of our digital ecosystem.
Understanding these underlying motivations is critical to developing more effective security strategies.The perceived ease and convenience of mobile devices often overshadow the need for rigorous security protocols. Users are accustomed to seamless interactions, and security measures can feel like an unnecessary hurdle in this process. This ingrained expectation of effortless use often trumps the understanding of potential vulnerabilities and risks.
The simplicity of logging in with a single touch or accessing information with a few taps fosters a sense of invulnerability. This, unfortunately, creates a blind spot in terms of security consciousness.
Perceived Ease of Use and Convenience
The user-friendly design of mobile devices, while a significant factor in their popularity, often contributes to a disregard for security. Intuitive interfaces and quick access to information create a perception of inherent safety. Consumers are often less inclined to engage with complex security measures if they perceive them as obstacles to their desired convenience. For instance, two-factor authentication, while a crucial security measure, can be seen as an unnecessary step for users accustomed to single-sign-on experiences.
Cost of Security Measures
Financial barriers can also discourage consumers from adopting robust security practices. Subscriptions for advanced security features, such as VPNs or comprehensive antivirus software, often present a cost that some users are unwilling to bear. This cost-benefit analysis frequently leans towards convenience, particularly for budget-conscious consumers. Free security solutions, while readily available, often come with limitations in terms of features and effectiveness, making the trade-off even more apparent.
Lack of Clear Security Communication
The way app developers and service providers communicate security measures directly impacts consumer behavior. Vague or overly technical explanations often leave users confused and disengaged. Clear, concise, and user-friendly explanations of security protocols are crucial to fostering a culture of security awareness. For example, if a banking app requires encryption for data transmission, users need to understand why this is necessary and how it benefits them.
It’s frustrating how many consumers are overlooking mobile security. With so much personal data stored on these devices, it’s crucial to adopt robust security measures. This is where solutions like deploying AI code safety goggles, as detailed in Deploying AI Code Safety Goggles Needed , become essential. The problem of complacent consumers needing more proactive measures in this space still remains.
Role of Perceived Trust in Brands and Services
Trust in a brand or service plays a significant role in shaping consumer security practices. Users who trust a company are more likely to adopt security measures recommended by that company. If a user perceives a service as reliable and trustworthy, they are more likely to believe the security measures are appropriate and necessary. Conversely, a history of data breaches or security vulnerabilities can erode trust, potentially discouraging security practices.
Trade-offs Between Convenience and Security
| Convenience | Security | Consumer Trade-off |
|---|---|---|
| Fast login | Strong password requirements | Prioritizing speed over complexity |
| Easy access to data | Data encryption | Prioritizing immediate access over data protection |
| Simple app interface | Multi-factor authentication | Prioritizing ease of use over robust security |
| Free service | Subscription-based security features | Prioritizing cost-effectiveness over comprehensive protection |
Analyzing the Impact of Ignoring Security
Ignoring mobile security can lead to a cascade of negative consequences, far beyond just a minor inconvenience. The repercussions can be significant, impacting finances, reputation, and even personal well-being. This section delves into the multifaceted damage that can result from neglecting mobile security measures.The digital world has become inextricably linked to our daily lives, and our mobile devices are at the heart of this connection.
Consequently, failing to secure these devices exposes us to risks that extend beyond the immediate. This analysis will examine the far-reaching consequences of this vulnerability, highlighting the importance of proactive security measures.
Financial Implications of Security Breaches
Neglecting mobile security exposes consumers to substantial financial risks. A compromised device can lead to unauthorized access to bank accounts, credit card information, and other sensitive financial data. This can result in significant financial losses through fraudulent transactions, identity theft, and the cost of recovering from the breach. For example, a user failing to enable two-factor authentication could see their online banking accounts emptied by a malicious actor.
The financial burden extends beyond direct losses, including the cost of restoring accounts, paying for identity theft protection services, and potentially legal fees.
Reputational Damage from Security Incidents
Security breaches can severely damage a consumer’s reputation, particularly in the digital age where online presence is crucial. A compromised account can lead to negative publicity, loss of trust from peers, and difficulties in future interactions. This is especially true for businesses, where a security incident can damage their brand image and deter potential customers. For instance, a retailer whose mobile payment system is compromised could lose customer trust and suffer a significant drop in sales.
Negative reviews and online comments can linger and negatively impact the reputation for a long time.
Legal Consequences for Consumers
Consumers may face legal consequences for neglecting mobile security. While direct legal action against an individual for a security breach may be rare, negligent behavior that contributes to a financial or reputational loss to others could potentially lead to legal action. This could involve legal recourse for financial damages, reputational harm, or potential criminal charges, especially if the security breach involves illegal activities like distributing malware.
For example, if a consumer knowingly uses a compromised device for illegal activities, they could face serious legal ramifications.
It’s a real shame that so many people are overlooking mobile security. While initiatives like the Department of Justice Offers Safe Harbor for MA Transactions Department of Justice Offers Safe Harbor for MA Transactions aim to bolster consumer confidence, the truth remains that most consumers still aren’t taking the necessary precautions. This alarming trend underscores the urgent need for more proactive educational campaigns.
Social and Psychological Effects of Security Breaches
Security breaches can have a significant social and psychological impact on consumers. A compromised account or device can lead to feelings of anxiety, stress, and even depression. The fear of identity theft, financial loss, and the potential for social stigma can significantly affect an individual’s mental health. Beyond individual trauma, there is also a social impact, as trust in digital systems can be eroded.
Impact Table of Mobile Security Incidents, Majority consumers are ignoring mobile security
| Level of Incident | Description | Financial Impact | Reputational Impact | Legal Consequences | Social/Psychological Impact |
|---|---|---|---|---|---|
| Low | Minor data breach, temporary account lock | Minimal financial loss, possible inconvenience | Slight reputational damage, minor disruption | Low probability of legal action | Mild anxiety, temporary frustration |
| Medium | Significant data breach, identity theft attempts | Moderate financial loss, account recovery costs | Moderate reputational damage, loss of trust | Possible legal action for financial damages | Significant anxiety, potential for stress-related issues |
| High | Major data breach, widespread fraud | Significant financial loss, identity theft | Severe reputational damage, brand crisis | High probability of legal action, criminal charges | Severe anxiety, emotional trauma, potential long-term psychological impact |
Potential Solutions and Mitigation Strategies
The alarmingly high rate of mobile security negligence among consumers necessitates a multifaceted approach. Simply acknowledging the problem isn’t enough; we must actively explore and implement practical solutions. This includes fostering a culture of security awareness, designing user-friendly security features, promoting transparency, and implementing effective tools. Furthermore, governments play a crucial role in establishing regulations and enforcing best practices.
Education and Awareness Campaigns
Raising public awareness about mobile security threats is paramount. Effective campaigns should target various demographics with tailored messages. This includes utilizing diverse communication channels, such as social media, educational materials, and partnerships with influencers. Clear and concise explanations of common security risks, like phishing and malware, are crucial. Illustrative examples of real-world attacks and their consequences can be powerful motivators for change.
Emphasis should also be placed on the importance of strong passwords, regular updates, and recognizing suspicious activity. For example, a campaign might highlight the financial and reputational damage that can result from a data breach. Educational materials should be accessible and easy to understand for all audiences, from children to seniors.
Design Principles for User-Friendly Security Features
User experience (UX) is critical for the successful adoption of security measures. Security features should be seamlessly integrated into the mobile experience, not an afterthought or an obstacle. This includes intuitive interfaces, clear instructions, and streamlined processes. Complex technical jargon should be avoided in favor of plain language. Security features should be unobtrusive but readily available when needed.
For instance, two-factor authentication (2FA) should be presented as a simple additional step, not a cumbersome barrier. Security prompts and warnings should be clearly presented and avoid overwhelming users with unnecessary information. Consider using visual cues and progress indicators to guide users through security procedures. A well-designed security feature empowers users without creating a frustrating experience.
Security Transparency and Communication
Consumers deserve clear and straightforward communication about their data security. Companies should openly disclose their data security practices and the steps they take to protect user information. Regular updates and security advisories should be provided in an accessible format. This includes providing detailed information about data breaches and the steps taken to mitigate them. Furthermore, companies should proactively communicate security best practices, such as password management and app permissions.
For instance, app stores could prominently display security ratings and user reviews related to data protection. This proactive approach builds trust and encourages responsible user behavior.
Effectiveness of Security Tools and Services
Numerous security tools and services are available for consumers, but not all are equally effective. Antivirus software, VPNs, and strong password managers all play important roles. Antivirus software effectively detects and removes malware, while VPNs enhance privacy and security by encrypting internet traffic. Strong password managers ensure the use of complex and unique passwords across multiple accounts.
The effectiveness of these tools depends on their ongoing updates and user compliance. A comprehensive approach that combines multiple security tools is often more effective than relying on a single solution. Reviews and comparisons of security tools can assist consumers in making informed choices.
Government Regulation and Enforcement
Government regulation plays a crucial role in ensuring minimum standards for mobile security. Clear regulations regarding data protection, breach notification, and the security of mobile applications are essential. Enforcement mechanisms should be in place to ensure compliance. For example, governments can mandate security audits for mobile apps before their release to the public. Penalties for non-compliance should deter malicious behavior and encourage responsible security practices.
Regulations should adapt to the evolving mobile landscape and emerging threats. International collaboration is important to address global security concerns.
Comparison of Security Solutions
| Security Solution | Pros | Cons | Effectiveness |
|---|---|---|---|
| Antivirus Software | Malware detection, removal | Can be resource-intensive, false positives | High, if updated regularly |
| VPN | Enhanced privacy, encryption | Potential speed reduction, reliability issues | High, for specific use cases |
| Password Manager | Strong password generation, storage | Reliance on a single service, potential security risks | High, if used securely |
| Two-Factor Authentication | Added layer of security | Complexity for users | High, if implemented correctly |
Illustrating the Problem with Examples
Ignoring mobile security can lead to a cascade of negative consequences, ranging from minor inconveniences to significant financial losses and reputational damage. Understanding real-world examples is crucial for highlighting the severity of the problem and motivating individuals to prioritize security. This section will delve into specific incidents, industry impacts, consumer experiences, fraudulent tactics, and user-friendly security features.
A Case Study of a Consumer Incident
A recent case involved a user whose mobile banking app was compromised. The attacker gained access to the user’s account and transferred a substantial amount of money. The user was unaware of the breach until they received a notification of a significant transaction from an unfamiliar location. This incident highlights the potential for financial loss when mobile security is neglected.
The attacker likely exploited a vulnerability in the user’s device or a weak password, demonstrating the importance of strong authentication and up-to-date security measures.
Impact on Various Industries
Mobile security breaches can impact various industries, disrupting operations and potentially causing significant financial losses. For example, a retailer experiencing a breach of their mobile payment system could face large-scale fraud and damage customer trust. Healthcare providers could see sensitive patient data compromised, leading to legal and reputational issues. The financial sector is particularly vulnerable, as mobile banking apps are frequently targeted for fraudulent activities.
Consumer Experiences with Mobile Security Issues
Many consumers have reported instances of phishing attempts on their mobile devices. One user described receiving a seemingly legitimate text message that requested their login credentials. Another user shared an experience where a malicious app disguised as a popular game stole their personal information. These experiences underscore the importance of being cautious of suspicious messages and downloads.
Users should scrutinize links and be wary of unsolicited requests for personal information.
Forms of Fraudulent Behavior
Fraudulent activities targeting mobile consumers take various forms. Phishing attacks are common, where attackers attempt to trick users into revealing sensitive information. Malware, often disguised as legitimate apps, can steal personal data and control devices. SIM swapping, where attackers gain access to a user’s phone number, is another common tactic. These examples highlight the diverse ways attackers exploit vulnerabilities.
It is crucial to remain vigilant and educated on these common tactics.
User-Friendly Mobile Security Features
Many mobile security features are designed to be intuitive and easy to use. Two-factor authentication, requiring a secondary verification method beyond a password, adds an extra layer of security. Strong password managers can help users create and store complex passwords, making it less likely that they will reuse weak passwords across multiple accounts. These features are vital for protecting user accounts.
Using them consistently can effectively deter potential attackers.
Real Consumer Feedback on Mobile Security Concerns
“I’m constantly worried about someone accessing my personal information through my phone. I wish there was a simpler way to manage all my security settings without having to be a tech expert.”
This quote highlights a common concern among consumers. The complexity of mobile security settings can be daunting for many, making it harder to maintain comprehensive security. Simplified interfaces and intuitive security features could help alleviate this concern and encourage broader adoption of security measures.
Last Word
The alarming reality of majority consumers ignoring mobile security underscores the urgent need for improved awareness and education. It’s crucial that individuals understand the risks and take proactive steps to protect themselves. Ultimately, a collaborative effort between consumers, developers, and governments is essential to cultivate a more secure mobile environment.
Detailed FAQs: Majority Consumers Are Ignoring Mobile Security
What are the most common types of mobile security threats?
Common threats include malware infections, phishing attempts that trick users into revealing sensitive information, and scams disguised as legitimate apps or messages.
How can I tell if an app is trustworthy?
Look for reviews, check the developer’s reputation, and be wary of apps asking for excessive permissions.
Why do consumers sometimes choose convenience over security?
The perceived ease of use and immediate gratification of mobile devices can outweigh concerns about security. Additionally, the cost of security measures, like subscriptions, can deter some users.
What are the potential financial consequences of a security breach?
Financial losses can range from stolen funds to identity theft, leading to significant credit damage and financial hardship.