Mafia Cyberattacks Malwarebytes Alert
Malwarebytes detects new mafia launching cyber attacks including ransomware, a frightening development that reveals a new dimension in cybercrime. This sophisticated threat actor is using advanced techniques, likely employing ransomware to disrupt and potentially extort victims. The implications for various sectors are significant, demanding careful consideration of preventative measures.
This emerging trend highlights a concerning shift in cyberattacks. The mafia group is apparently leveraging advanced tools, potentially including new strains of ransomware, to target organizations. Malwarebytes’ detailed analysis and detection capabilities are crucial to understanding and mitigating the risk. The attack methods used will be explored in this post, along with the potential damage and preventive strategies.
Overview of the Threat
A new ransomware operation, seemingly affiliated with a criminal organization often referred to as the “Mafia,” is targeting various sectors. Initial reports indicate a sophisticated approach, leveraging advanced malware and potentially targeting critical infrastructure or sensitive data. The group’s modus operandi suggests a significant escalation in cybercrime tactics, posing a serious threat to businesses and individuals alike.This emerging cyberattack trend highlights a worrying escalation in the sophistication and organization of ransomware attacks.
The attackers are not simply opportunistic; they appear to be strategically targeting vulnerable systems and exploiting specific vulnerabilities. This shift towards a more organized, calculated approach demands a proactive and comprehensive response from both individual users and large enterprises.
Characteristics of the Emerging Malware
The malware used in these attacks exhibits several concerning characteristics. It appears to be highly modular, capable of adapting to various security measures and potentially evading detection. The attackers seem adept at utilizing advanced techniques like encryption, data exfiltration, and persistent infection to ensure maximum impact. The ransomware’s capabilities are evolving, indicating a continuous refinement of their attack vectors.
Methods Used by the Mafia Group
The Mafia group employs a multifaceted approach to launch their cyberattacks. Initial infiltration often involves exploiting known vulnerabilities in software or phishing campaigns. These attacks are often meticulously planned, targeting specific organizations or individuals. Once inside the system, the attackers deploy their malware, encrypting data and demanding payment for its release. Furthermore, they may also utilize advanced techniques like social engineering, creating believable narratives to gain access to systems.
Potential Impact on Various Sectors
The potential impact of this new ransomware on various sectors is significant. Financial institutions, healthcare providers, government agencies, and critical infrastructure are particularly vulnerable. Data breaches could lead to significant financial losses, operational disruptions, and reputational damage. Moreover, the targeted nature of the attacks suggests a specific focus on organizations with valuable or sensitive data, increasing the potential for extortion.
The consequences could range from temporary disruptions to long-term operational problems.
Examples of Similar Attacks by Organized Crime Groups
The emergence of this new ransomware operation echoes previous incidents of organized crime groups conducting cyberattacks. Groups like Lazarus and DarkSide have demonstrated the potential for significant damage caused by ransomware. These groups frequently target specific industries or organizations, leveraging their resources and expertise to maximize their impact. Their operations often involve extensive planning and execution, highlighting the evolving nature of cybercrime.
The attacks on Colonial Pipeline and JBS Foods demonstrate the real-world impact of ransomware targeting critical infrastructure and supply chains. These examples illustrate the need for robust security measures and proactive defense strategies.
Malwarebytes’ Detection Capabilities
Malwarebytes, a leading cybersecurity solution provider, employs a multifaceted approach to identify and neutralize sophisticated threats like the new mafia ransomware. Their detection system leverages a combination of signature-based and heuristic analysis, coupled with machine learning algorithms, to proactively safeguard users against emerging cyberattacks. This proactive approach is crucial in the ever-evolving landscape of malware, where traditional methods often fall short.The core of Malwarebytes’ detection engine rests on a sophisticated analysis of suspicious activities and file behaviors.
Malwarebytes is reporting a new wave of cyberattacks from a criminal group, including ransomware. This new threat is definitely concerning, but it’s important to remember that vulnerabilities in systems like Azure Cosmos DB can also be exploited by these groups. For detailed information on the Azure Cosmos DB Vulnerability, check out this resource: Azure Cosmos DB Vulnerability Details.
Knowing about these vulnerabilities helps in strengthening defenses against these sophisticated attacks.
This analysis is performed across multiple layers, allowing the system to identify threats even if they employ obfuscation techniques. The key is not just recognizing known malware, but also understanding how new threats behave and adapt. This approach is crucial for staying ahead of the curve in the ongoing arms race between malware developers and cybersecurity companies.
Specific Detection Techniques
Malwarebytes utilizes a comprehensive set of techniques to identify the new mafia malware. These techniques are designed to detect malicious activities at various stages, from initial infection to execution of harmful payloads. The approach is multi-layered, meaning that multiple layers of detection are triggered, providing redundancy and reducing the chance of false positives.
- Signature-Based Detection: Malwarebytes maintains a constantly updated database of known malicious code patterns, often referred to as signatures. When a file or process matches a known signature, it is immediately flagged as malicious. This approach is effective for known threats, but it is less effective against new, previously unseen threats.
- Heuristic Analysis: This technique analyzes the behavior of files and processes to identify suspicious patterns. For example, if a file attempts to modify system files or connect to known malicious domains, it triggers an alert. Heuristic analysis is vital in detecting novel malware, as it can identify malicious behavior without needing a prior signature.
- Machine Learning (ML): Malwarebytes’ advanced machine learning algorithms learn from massive datasets of malware and benign files. This enables the system to identify subtle anomalies and behaviors associated with malicious software. These algorithms are continuously updated and refined, making them increasingly effective at detecting sophisticated attacks. The key advantage of ML is its ability to adapt to emerging threats and to evolve its detection patterns based on new data.
- Sandboxing: Suspect files or processes are isolated in a virtual environment (sandbox). Their behavior is monitored for malicious activities. This isolates the threat, preventing it from affecting the host system while the analysis takes place.
Key Features of the Detection System
The detection system has several key features that contribute to its effectiveness in identifying the new mafia threat. These features are essential in the dynamic threat landscape.
- Real-time Monitoring: The system constantly monitors system activity, identifying suspicious behavior in real time. This is critical for stopping attacks before they cause significant damage. This proactive approach allows for immediate responses to emerging threats.
- Multi-layered Protection: The detection system employs multiple layers of security. This means that if one detection method fails to identify a threat, others can step in to prevent harm. This redundancy is vital in preventing bypasses.
- Continuous Learning: Malwarebytes constantly updates its database of known threats and adapts its detection algorithms based on new information. This ensures that the system remains effective against emerging malware and attacks. This continuous improvement cycle is vital for maintaining efficacy in the ever-changing threat landscape.
Comparison with Other Cybersecurity Solutions
Malwarebytes’ approach to detection differs from other cybersecurity solutions in its emphasis on machine learning and heuristic analysis. While many solutions rely heavily on signature-based detection, Malwarebytes proactively identifies threats based on their behavior. This proactive approach helps in detecting zero-day exploits and unknown threats. The proactive approach is a key differentiator in the evolving threat landscape.
Step-by-Step Detection Process
The detection process involves several steps, each contributing to a comprehensive analysis:
- File/Process Identification: The system identifies new files or processes that are flagged as suspicious.
- Heuristic Analysis: The system performs a heuristic analysis of the file’s behavior to determine if it exhibits any malicious patterns.
- ML Algorithm Evaluation: The machine learning algorithm evaluates the file’s characteristics against the vast dataset of known and unknown threats.
- Sandboxing and Monitoring: The file or process is isolated in a sandbox to observe its activity in a controlled environment.
- Threat Classification: The system classifies the threat based on its behavior and characteristics.
- Alert and Remediation: If the threat is identified as malicious, the system issues an alert and initiates remediation measures to remove the threat.
Impact and Implications
The emergence of a new mafia-linked cybercrime group launching ransomware attacks signifies a significant escalation in the threat landscape. These attacks are no longer just about financial gain; they represent a sophisticated and potentially devastating assault on organizations and individuals alike. Understanding the ramifications of such attacks is crucial for proactive defense and mitigation strategies.The implications extend far beyond the immediate financial losses, impacting the psychological well-being of victims, eroding public trust, and even challenging the efficacy of existing cybersecurity measures.
This discussion will delve into the potential targets, the magnitude of financial and operational disruption, the resulting psychological and reputational damage, and the broader societal impact on cybersecurity and law enforcement.
Potential Targets and Vulnerabilities
The targets of these sophisticated ransomware attacks are diverse and include a wide range of organizations and individuals. Critical infrastructure, financial institutions, healthcare providers, and government agencies are particularly vulnerable. These entities often possess sensitive data, intricate operational systems, and significant financial resources, making them attractive targets for malicious actors. Vulnerabilities can stem from outdated software, weak passwords, inadequate security protocols, or poorly trained personnel.
Exploiting these vulnerabilities allows attackers to gain unauthorized access and inflict significant damage.
Malwarebytes just flagged a new, sophisticated cybercrime ring, launching ransomware attacks. This highlights the ever-evolving threat landscape, and the critical need for robust security measures. Fortunately, the Department of Justice Offers Safe Harbor for MA Transactions Department of Justice Offers Safe Harbor for MA Transactions is a promising step in protecting businesses and individuals from such attacks.
This new development, coupled with the emerging trends in ransomware, necessitates proactive measures to safeguard digital assets.
Financial Losses and Operational Disruptions
Ransomware attacks can lead to substantial financial losses, both directly and indirectly. Direct losses include the ransom payments themselves, which can be substantial. Indirect losses encompass the costs of recovery efforts, such as data restoration, system remediation, and legal fees. Operational disruptions caused by ransomware can cripple organizations, leading to lost productivity, decreased revenue, and damage to reputation.
Examples like the Colonial Pipeline attack illustrate the catastrophic consequences of ransomware on critical infrastructure, leading to fuel shortages and economic disruption. The financial strain can also cascade through supply chains, impacting numerous businesses and consumers.
Psychological and Reputational Damage
Beyond the financial ramifications, ransomware attacks can inflict significant psychological and reputational damage on victims. The loss of sensitive data, disruption of operations, and the threat of further attacks can cause considerable stress, anxiety, and fear among employees, customers, and stakeholders. Reputational damage can be devastating, eroding public trust and confidence in the organization. The perceived inability to protect sensitive data can lead to loss of clients, partnerships, and market share.
Broader Implications for Cybersecurity and Law Enforcement
The rise of these sophisticated ransomware groups underscores the urgent need for improved cybersecurity practices and enhanced law enforcement capabilities. Collaboration between public and private sectors is essential to share threat intelligence, develop joint strategies, and enforce stricter penalties for cybercrimes. Strengthening cybersecurity regulations, promoting awareness and education, and investing in advanced cybersecurity tools are crucial steps to deter and mitigate these attacks.
The evolution of these threats requires constant adaptation and vigilance from both organizations and law enforcement agencies. The complexity of these attacks demands proactive measures to prevent them, detect them, and respond to them effectively. The success of these measures depends on a collaborative effort to address this increasingly sophisticated cybercrime problem.
Malwarebytes is reporting a new wave of cyberattacks, with organized crime groups launching ransomware campaigns. This highlights the urgent need to bolster our defenses, and deploying AI Code Safety Goggles Needed here is crucial. These sophisticated attacks underscore the importance of proactive security measures to mitigate the risk of falling victim to such criminal activity.
Potential Mitigation Strategies

The escalating threat of ransomware attacks, orchestrated by sophisticated criminal groups like the Mafia, necessitates a proactive and multi-layered approach to protection. Failing to implement robust security measures can lead to significant financial losses, reputational damage, and disruption of operations. This section Artikels crucial mitigation strategies to safeguard against these attacks and effectively respond to incidents.
Comprehensive Security Posture
A strong security posture is the foundation for preventing and responding to cyberattacks. This involves a combination of technical controls, employee training, and incident response planning. Organizations must adopt a zero-trust security model, assuming that every user and device could be compromised, and implement multi-factor authentication (MFA) for all accounts.
Proactive Measures to Reduce Infection Risk
Preventing infections is paramount. Proactive measures, such as regular software updates, robust anti-malware protection, and employee training, drastically reduce the likelihood of successful attacks. Regular vulnerability assessments and penetration testing can identify and address weaknesses in systems before attackers exploit them. These preventative steps are crucial in fortifying defenses against evolving threats.
- Regular Software Updates: Keeping operating systems, applications, and security software updated is essential. Outdated software often contains vulnerabilities that attackers can exploit. Automated patching systems can significantly streamline this process.
- Robust Anti-Malware Protection: Employing reputable and up-to-date anti-malware solutions is vital. These solutions should not only detect known threats but also be capable of identifying zero-day exploits. Continuous monitoring and proactive threat intelligence integration are crucial components.
- Employee Security Awareness Training: Phishing attacks remain a common vector for ransomware infections. Regular training sessions can educate employees about identifying suspicious emails, links, and attachments. These sessions should focus on recognizing social engineering tactics and the importance of reporting suspicious activity.
Ransomware Attack Recovery
Developing a comprehensive incident response plan is critical for recovering from a ransomware attack. This plan should Artikel steps for containing the attack, identifying affected systems, and restoring data. It’s important to have a tested backup and recovery strategy in place.
- Data Restoration: Regular backups are essential for recovering data after a ransomware attack. Offsite backups stored in a secure location are critical to avoid data loss in case of a physical attack or disaster. A well-defined backup and recovery process will significantly reduce the downtime and data loss associated with ransomware attacks.
- Incident Response Plan: A documented incident response plan should Artikel the roles and responsibilities of individuals and teams during an attack. The plan should include procedures for containing the spread of malware, notifying affected parties, and coordinating recovery efforts. The plan should be regularly reviewed and updated to reflect the latest threat landscape.
Best Practices for Securing Sensitive Data and Systems
Securing sensitive data and systems requires a combination of technical and administrative controls. Implementing strong access controls, encrypting data at rest and in transit, and implementing multi-factor authentication are critical steps.
- Access Controls: Implementing least privilege access controls limits the ability of attackers to move laterally within the network. This means users only have access to the resources they need to perform their job functions.
- Data Encryption: Encrypting sensitive data both at rest and in transit protects the data from unauthorized access, even if the system is compromised. Modern encryption standards and tools are readily available to enhance data security.
- Multi-Factor Authentication (MFA): Enforcing MFA adds an extra layer of security, making it significantly harder for attackers to gain access to accounts. MFA should be implemented for all critical accounts and systems.
Technical Analysis of the Malware
This new ransomware strain, emerging from the shadowy mafia cyber-attack groups, presents a complex challenge for cybersecurity professionals. Understanding its intricate code structure and the vulnerabilities it exploits is crucial to developing effective defenses and mitigating its impact. This analysis delves into the technical details of this threat, examining its code, distribution methods, and comparisons with existing ransomware variants.
Malware Code Structure and Functionality
The malware’s code is designed to leverage a sophisticated modular architecture, enabling its rapid adaptation to evolving security measures. Key components include an initial payload designed to establish persistence on the compromised system. This persistence module can install backdoors and establish communication channels with command-and-control (C&C) servers. The encryption module employs advanced cryptographic algorithms, targeting various file types and potentially utilizing techniques to bypass security measures like file integrity monitoring.
Further modules handle the exfiltration of sensitive data and the generation of ransom notes. The modular structure allows for the development of different attack vectors, tailored to specific vulnerabilities and targets. This flexibility makes it challenging to develop a single solution to counter its capabilities.
Vulnerabilities Exploited
The malware exploits a range of vulnerabilities, including known and zero-day exploits. A common vector involves exploiting outdated or poorly patched software, targeting systems with insufficient security configurations. It may also exploit vulnerabilities in widely used applications, gaining initial access to the system through common attack vectors. The attackers likely conduct reconnaissance to identify systems with known vulnerabilities and exploit those that are not properly secured.
This proactive approach allows them to maximize their chances of success.
Distribution Techniques
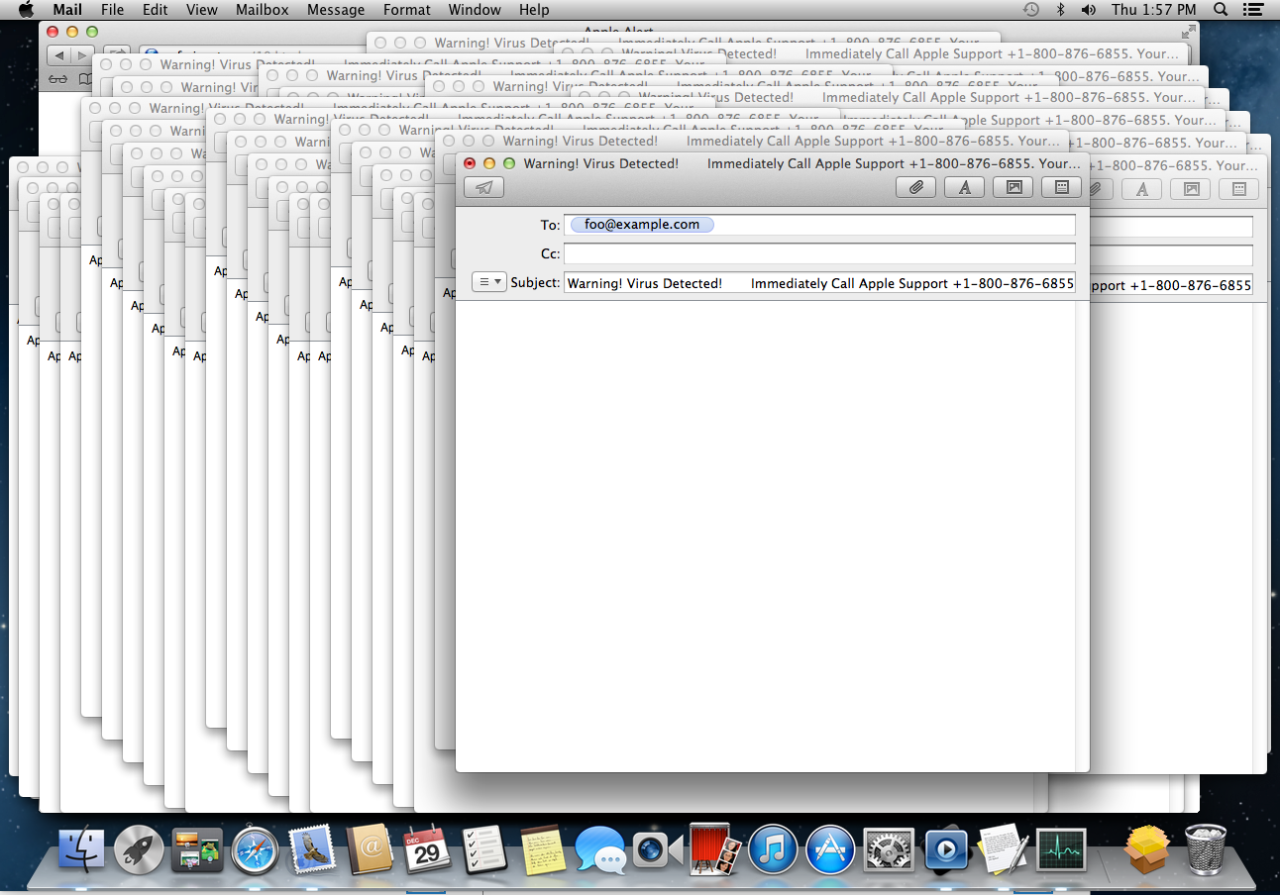
The malware’s distribution methods are diverse and sophisticated. It is likely spread via phishing emails, malicious attachments, compromised websites, and exploit kits. These methods rely on social engineering tactics, deceiving victims into downloading infected files or visiting compromised websites. The use of social engineering makes it more difficult for victims to identify the threat. Advanced techniques like spear-phishing campaigns, tailored to specific organizations or individuals, are also probable.
Comparison with Existing Ransomware Variants
Compared to other ransomware families, this new strain demonstrates advanced features and capabilities. It leverages more sophisticated encryption algorithms and sophisticated persistence mechanisms, offering greater resistance to traditional decryption methods. It also exhibits a more comprehensive approach to data exfiltration, aiming to maximize financial gain and create reputational damage for the targeted organizations. In comparison to other ransomware families, this new variant’s modular architecture enables the flexibility to adapt to new security measures.
While many ransomware variants rely on simple encryption techniques, this strain leverages advanced cryptographic algorithms, making it harder to recover files without paying the ransom. Furthermore, its ability to exfiltrate sensitive data adds an extra layer of threat.
Legal and Regulatory Considerations: Malwarebytes Detects New Mafia Launching Cyber Attacks Including Ransomware
The rise of sophisticated ransomware attacks, orchestrated by organized crime groups like the new mafia, necessitates a robust legal and regulatory framework. These attacks not only cripple organizations but also raise complex legal and ethical questions about liability, data protection, and international cooperation. Understanding these considerations is crucial for developing effective strategies to combat this emerging threat.The legal landscape surrounding cybercrime is constantly evolving, making it challenging for organizations to navigate the intricacies of jurisdiction, evidence gathering, and prosecution.
International collaboration is essential to address the transnational nature of these attacks, ensuring that perpetrators are held accountable regardless of their location.
Legal Implications of Ransomware Attacks
Ransomware attacks carry significant legal implications for both the victims and the perpetrators. Victims face potential liabilities for data breaches, particularly if they fail to adhere to data protection regulations. Perpetrators are subject to criminal prosecution in jurisdictions where the attacks originate or have a significant impact. Critically, proving intent and tracing the perpetrators’ activities can be challenging, especially in cases involving sophisticated encryption and obfuscation techniques.
Examples include the Colonial Pipeline attack and the JBS Foods ransomware incident, highlighting the severity of these attacks and the potential for significant financial and reputational damage.
Regulatory Requirements for Reporting and Responding to Cyber Incidents, Malwarebytes detects new mafia launching cyber attacks including ransomware
Regulatory bodies worldwide are implementing guidelines and regulations for reporting and responding to cyber incidents. These regulations often mandate specific procedures for notifying affected parties, conducting investigations, and implementing remedial measures. Failure to comply with these regulations can lead to substantial fines and legal repercussions. For example, GDPR in Europe mandates specific requirements for data breach notification, while the NIST Cybersecurity Framework provides a comprehensive guide for organizations to develop their incident response plans.
Potential Liabilities for Organizations Targeted by These Attacks
Organizations targeted by ransomware attacks can face a range of potential liabilities. These liabilities can include financial penalties, reputational damage, and legal battles over data breaches. Furthermore, if the organization is found to have inadequately secured its systems, leading to the attack, they could be held liable for damages. The WannaCry ransomware attack, for instance, highlighted the vulnerability of organizations with outdated systems and inadequate security protocols.
International Cooperation Needed to Combat These Threats
Effective international cooperation is critical to combatting ransomware threats. This involves sharing information about emerging threats, coordinating law enforcement efforts, and developing international standards for cybersecurity. International collaboration platforms like the Budapest Convention on Cybercrime offer a framework for harmonizing national laws and improving cooperation between countries. Moreover, establishing clear guidelines for handling ransom demands and preventing future attacks is a critical component of this international effort.
Joint task forces and information-sharing initiatives among nations can significantly enhance the ability to identify and dismantle these criminal organizations.
Visual Representation of the Threat
The rise of sophisticated cyberattacks, particularly ransomware campaigns orchestrated by criminal organizations, necessitates a clear understanding of the attack chain and the malware’s propagation within a network. Visual representations offer invaluable insights into the intricate steps involved, enabling proactive defense strategies. This section details various attack chain visualizations, illustrating the malware’s spread and the stages of a ransomware attack.
Attack Chain Visualization
The attack chain typically begins with reconnaissance, followed by exploitation of vulnerabilities, and culminates in data encryption and ransom demands. This attack model is a simplified depiction, but it accurately represents the core phases. A detailed flowchart, if created, would include more specific techniques. 
A typical attack chain begins with initial reconnaissance, aiming to identify potential targets. This often involves gathering information about the victim organization’s network infrastructure, security posture, and employee practices. The second phase focuses on exploiting identified vulnerabilities, often involving phishing emails, exploiting software flaws, or employing other social engineering techniques. Once access is gained, the attackers move to the next stage, which is often the deployment of malicious payloads. This could involve installing ransomware, stealing data, or creating backdoors for future access. Finally, the attackers encrypt data, restrict access, and demand a ransom payment.
Malware Propagation Diagram
This diagram illustrates the spread of malware within a network. The initial infection point, often through a compromised user account or a vulnerable system, serves as the source for infection. From there, the malware propagates through the network, potentially infecting other devices or systems connected to the compromised node. The rate of spread depends on factors like network architecture, security controls, and the malware’s capabilities.

A visual representation of the malware propagation would showcase the connections between infected devices and the path of the malware’s spread. This would depict the steps involved in moving from one machine to another, perhaps through file sharing, network drives, or email attachments. Understanding the network pathways is crucial for containment and remediation efforts.
Ransomware Attack Stages
The following table Artikels the stages of a ransomware attack, highlighting the key actions and potential consequences. Each stage plays a crucial role in the overall attack, allowing attackers to achieve their objectives. 
The stages of a ransomware attack, visualized as a flowchart, would depict the progression from initial intrusion to data encryption and ransom demand. Each stage involves specific actions by the attacker and responses by the victim, which are crucial in understanding the dynamics of such attacks.
Malware Characteristics and Detection Techniques
This table summarizes key characteristics of the malware and the detection techniques employed to identify and mitigate its impact.
| Malware Feature | Description | Detection Technique | Impact |
|---|---|---|---|
| Encryption Method | Utilizes a strong encryption algorithm (e.g., AES) to render data inaccessible. | File integrity monitoring, looking for unusual encryption patterns. Antivirus signatures and heuristics. | Data loss, business disruption, financial losses. |
| Payload Type | Ransomware payload. | File type analysis, suspicious process detection. Malware signature matching. | Data encryption and access restrictions. |
| Distribution Method | Spear phishing emails, compromised websites. | Email filtering, web security monitoring, network traffic analysis. Endpoint detection and response (EDR) systems. | Network compromise, user account compromise. |
Conclusion
In conclusion, the emergence of mafia-linked cyberattacks, including ransomware, underscores the evolving nature of cyber threats. Malwarebytes’ proactive detection is essential, and understanding the attack methods, potential targets, and mitigation strategies is critical. The impact on various sectors, from financial losses to reputational damage, emphasizes the need for robust cybersecurity measures. By understanding the details, we can better prepare and protect ourselves from these sophisticated threats.
Popular Questions
What are the common vulnerabilities targeted by these attacks?
The attacks likely target vulnerabilities in outdated software, weak passwords, and insufficient multi-factor authentication. They might also exploit social engineering tactics to gain unauthorized access.
How can organizations prevent these types of attacks?
Implementing robust security measures like strong passwords, regular software updates, employee training, and intrusion detection systems are key. Multi-factor authentication should also be used where possible.
What are the legal ramifications of these attacks?
The legal implications vary based on jurisdiction, but often involve potential lawsuits, fines, and even criminal charges, depending on the extent of the damage and breach of regulations.
What steps should be taken if a ransomware attack occurs?
Immediately disconnect the infected systems from the network, and contact cybersecurity experts to assess the situation and restore data. Never pay the ransom, as it often does not guarantee data recovery.