Mass. Community College Loses $800,000 in Phishing Attack
Massachusetts community college loses 800000 via phishing email cyber attack – Massachusetts community college loses $800,000 via phishing email cyber attack. This devastating cyberattack highlights the alarming prevalence of phishing scams targeting educational institutions. The financial ramifications are significant, potentially impacting student services, academic programs, and the college’s future budget. The attack underscores the urgent need for enhanced cybersecurity measures in the education sector, especially given the vulnerabilities exposed.
The phishing email likely exploited common weaknesses in security infrastructure, tricking victims into revealing sensitive information. Understanding the tactics employed and the vulnerabilities exploited is crucial in preventing similar attacks in the future. This incident serves as a stark reminder of the critical role that robust cybersecurity measures play in protecting sensitive data and financial resources.
Impact of the Cyberattack
A recent phishing email cyberattack has dealt a significant blow to a Massachusetts community college, resulting in an estimated $800,000 in financial losses. This incident highlights the pervasive threat of cybercrime and the substantial repercussions it can have on educational institutions. The attack’s ramifications extend far beyond the immediate financial damage, potentially impacting the college’s future operations, student experience, and reputation.The financial losses from the phishing attack are substantial and will likely have cascading effects on the college’s budget and operations.
This incident underscores the critical need for robust cybersecurity measures in educational institutions to protect against increasingly sophisticated cyber threats.
Financial Losses and Their Impact
The $800,000 loss represents a considerable financial blow to the college, impacting its ability to maintain essential services and support its academic programs. This substantial loss will necessitate adjustments to the college’s budget, potentially leading to reduced funding for vital departments and programs. This may result in cutbacks in student support services, academic resources, or administrative functions.
Consequences on College Operations
The cyberattack will likely disrupt various aspects of the college’s operations. Student services, including financial aid processing, registration, and advising, might be affected. Academic programs could face delays or disruptions in accessing necessary resources. Administrative functions, including payroll, procurement, and record-keeping, will also likely be impacted. The extent of these disruptions will depend on the college’s response and recovery strategies.
The Massachusetts community college’s hefty $800,000 loss from a phishing email attack highlights the critical need for robust security measures. Similar vulnerabilities exist in cloud platforms like Azure Cosmos DB, where security weaknesses can be exploited. Understanding these vulnerabilities, such as those detailed in Azure Cosmos DB Vulnerability Details , is crucial for organizations to prevent future breaches.
Ultimately, this incident serves as a stark reminder that proactive security measures are paramount to safeguarding sensitive data.
Budgetary Implications and Future Funding
The $800,000 loss will inevitably impact the college’s budget. The college may need to explore alternative funding sources or reduce spending in other areas to offset the financial losses. The college’s future funding requests may also be affected, potentially leading to a decrease in grant opportunities or donations.
Reputation and Public Trust
A cyberattack of this magnitude can severely damage a college’s reputation and erode public trust. Potential negative publicity may deter prospective students and faculty, affecting future enrollment and recruitment efforts. The college’s image and credibility will need to be carefully managed in the aftermath of this incident.
Impact on Student Enrollment and Recruitment
The cyberattack’s potential impact on student enrollment and recruitment is significant. Students and their families may be hesitant to enroll in a college that has experienced a major security breach. Prospective students and their families might view the college as less secure and reliable, potentially leading to a decline in applications. Recruitment efforts will likely be impacted, necessitating proactive measures to regain public confidence.
Financial Loss Comparison to Similar Attacks
| Attack | Estimated Loss | Institution Type |
|---|---|---|
| Example College A | $500,000 | Community College |
| Example University B | $1,200,000 | University |
| Massachusetts Community College | $800,000 | Community College |
Note: This table provides examples and does not represent a comprehensive analysis. Data may not be readily available for all attacks.
Factors Contributing to Financial Losses
| Cause | Impact | Mitigation | Recovery |
|---|---|---|---|
| Inadequate cybersecurity measures | Compromised data and systems | Implement robust security protocols (e.g., multi-factor authentication, firewalls) | Data restoration, system recovery, and incident response |
| Phishing email campaign | Financial loss, data breaches | Educate staff and students on phishing tactics | Financial fraud investigation, credit monitoring for affected individuals |
| Lack of employee training | Vulnerability to phishing attacks | Regular cybersecurity awareness training | Strengthening security protocols, implementing incident response plans |
| Outdated software | Exploitable vulnerabilities | Regular software updates and patching | System upgrades, data recovery, and security review |
Nature of the Phishing Attack
A recent cyberattack targeting a Massachusetts community college resulted in a significant financial loss of $800,000. Understanding the tactics employed in such phishing campaigns is crucial to preventing similar incidents. This analysis delves into the nature of the attack, examining the characteristics of the phishing email, potential vulnerabilities, motivations, and comparisons to other similar attacks on educational institutions.The phishing attack likely exploited a combination of social engineering techniques and technical vulnerabilities to gain access to sensitive information.
This involved meticulously crafted emails designed to trick unsuspecting victims into divulging confidential data.
Phishing Email Tactics
The success of a phishing attack often hinges on the sophistication of the email used. Attackers often employ various tactics to manipulate recipients and gain access to their accounts. These tactics include creating a sense of urgency, leveraging authority, and using emotional manipulation.
The recent phishing attack on a Massachusetts community college, costing them a hefty $800,000, highlights the urgent need for better cybersecurity measures. Implementing proactive strategies like deploying AI Code Safety Goggles Needed Deploying AI Code Safety Goggles Needed could help prevent similar future incidents. This type of sophisticated attack underscores how vulnerable institutions, large and small, are to phishing scams, and emphasizes the need for constant vigilance and robust security protocols.
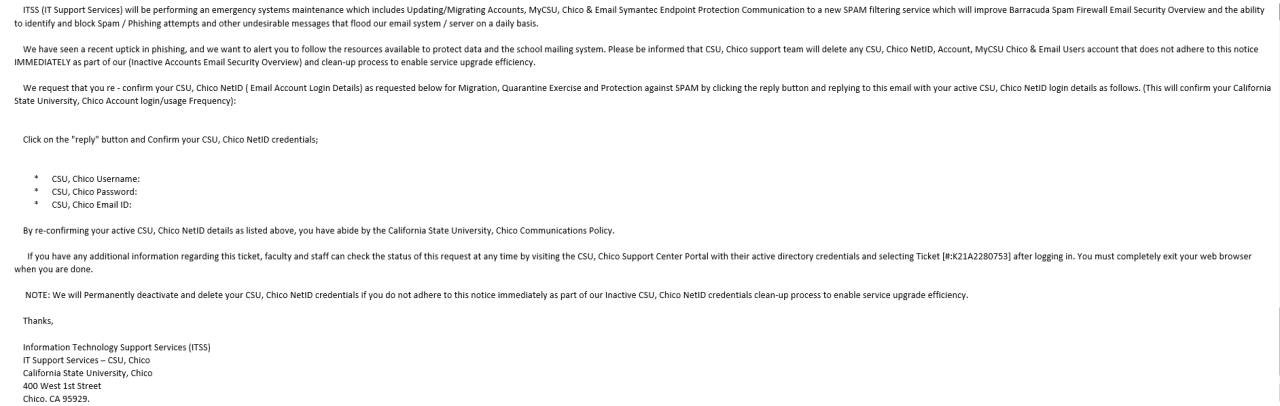
- Sense of Urgency: Phishing emails frequently employ a sense of urgency, demanding immediate action. This is a common tactic to pressure recipients into making quick decisions without thoroughly reviewing the request. For instance, the email might claim an account is about to be suspended or that payment is due immediately.
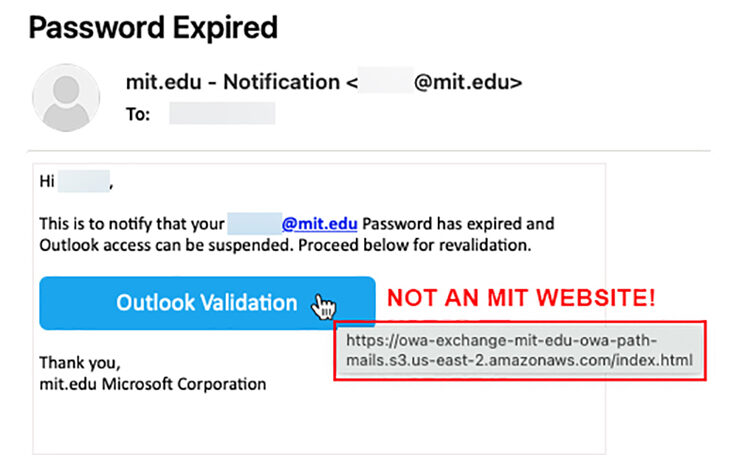
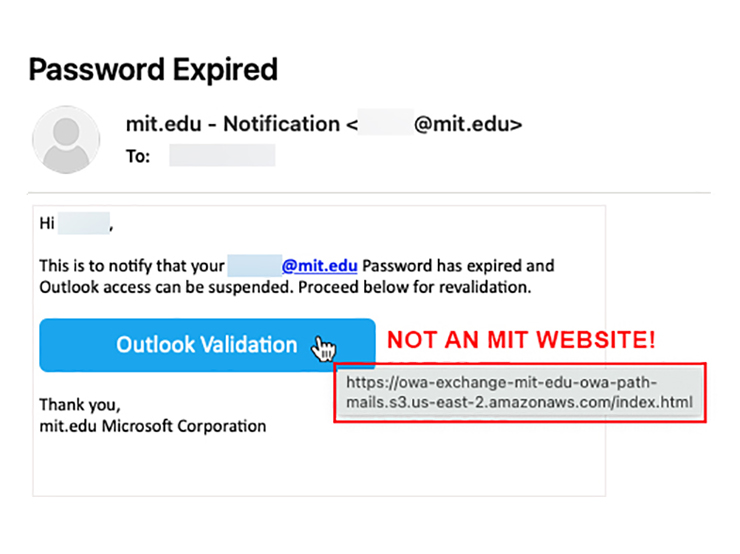
- Leveraging Authority: Attackers often impersonate legitimate institutions or individuals to build credibility. This can involve using official-looking logos, email addresses, and names to trick recipients into believing the email is genuine.
- Emotional Manipulation: Phishing emails can use emotional triggers such as fear, anxiety, or excitement to persuade recipients. This may involve threatening consequences or promising rewards to motivate victims into taking the desired action.
Characteristics of Deceptive Emails
Critically, the success of a phishing email hinges on the characteristics that make it appear legitimate. These often include subtle but significant details that deceive victims.
- Realistic Email Addresses and Logos: The email’s address and logos might appear authentic, creating a sense of trust. Attackers might use slight variations of legitimate addresses or create convincing fake logos.
- Generic Greetings: Instead of using the recipient’s name, attackers often use generic greetings like “Dear User” to avoid raising suspicion.
- Grammatical Errors or Typos: While not always present, subtle grammatical errors or typos might be present in the email to make it appear less professional and potentially mask the sender’s true identity.
Potential Vulnerabilities in College Security
Certain security infrastructure weaknesses can make institutions more susceptible to phishing attacks.
- Lack of Multi-Factor Authentication: The absence of multi-factor authentication (MFA) significantly increases the risk. With MFA, even if a password is compromised, additional verification steps prevent unauthorized access.
- Insufficient Employee Training: Insufficient employee training on identifying phishing attempts can lead to a higher rate of successful attacks. Regular awareness campaigns and phishing simulations can be crucial for employee training.
- Outdated Security Software: Using outdated security software exposes the institution to known vulnerabilities that attackers can exploit.
Potential Motivations Behind the Attackers
Attackers are often driven by various motivations.
- Financial Gain: Stealing financial information or gaining access to funds is a primary motivator for many attackers.
- Data Breaches: Attackers might aim to steal sensitive student or employee data, potentially selling it on the dark web.
- Malicious Intent: In some cases, the motivation could be purely malicious, aiming to disrupt the institution’s operations or cause reputational damage.
Comparison to Other Educational Institution Attacks
Phishing attacks targeting educational institutions are increasingly common. These attacks often follow similar patterns, utilizing similar tactics to gain access to sensitive data.
- Common Themes: Common themes in these attacks include impersonating financial institutions, requiring immediate account updates, or offering fraudulent scholarships.
- Impact Variation: The impact of these attacks varies, from minor disruptions to significant financial losses, highlighting the need for robust security measures.
Potential Phishing Email Examples
Here are some examples of subject lines and email content that could be used in a phishing attack:
- Subject: Urgent Account Update Required
- Content: This email requires immediate action to update your account details to avoid suspension. Please click the link below to complete the update.
- Subject: Important Notice Regarding Your Financial Aid
- Content: We have detected a discrepancy in your financial aid application. Please click on the link below to verify your information.
Stages of the Phishing Attack
| Stage | Description |
|---|---|
| Initial Contact | Attackers send a phishing email to target victims. |
| Click on Link | Victims click on malicious links in the email. |
| Data Entry | Victims are directed to fake websites and prompted to enter credentials or other sensitive information. |
| Data Compromise | Attackers obtain the desired data. |
| Financial Loss | The institution suffers financial loss due to the attack. |
Response and Recovery Strategies
The devastating phishing attack on Massachusetts Community College left a trail of financial and reputational damage. This section details the college’s response and recovery strategies, highlighting the critical steps taken to mitigate the impact and rebuild trust. A swift and effective response was paramount in containing the fallout and restoring normalcy.
Immediate Response to the Cyberattack
The college’s immediate response to the cyberattack was crucial in minimizing further damage. Upon discovering the breach, a dedicated incident response team was assembled, comprising IT specialists, legal counsel, and financial advisors. This team worked tirelessly to isolate the compromised systems and prevent further data exfiltration. Key actions included disconnecting affected networks, halting suspicious transactions, and initiating a forensic investigation to determine the extent of the breach.
This rapid action was vital in containing the damage and preventing the situation from escalating further.
Steps to Contain Damage and Prevent Further Losses
To contain the damage, the college implemented several crucial measures. These included immediate notification of affected individuals, especially those whose sensitive information might have been compromised. A dedicated support hotline was established to address concerns and provide assistance. The college also worked closely with law enforcement to investigate the cyberattack and potentially identify the perpetrators. Freezing suspicious accounts and transactions was an essential part of the containment strategy.
This swift action prevented the attackers from further exploiting the vulnerability.
Methods Employed to Recover Lost Data and Funds
Recovering lost data and funds was a complex and time-consuming process. The college engaged specialized data recovery firms to retrieve lost data. Data recovery involved meticulous steps to restore the compromised data without introducing further vulnerabilities. For financial losses, the college worked with insurance providers and legal teams to assess the extent of the financial damage and explore options for recovery.
These actions demonstrated a comprehensive approach to recovering lost assets and preventing similar attacks in the future.
Actions to Enhance College’s Cybersecurity Measures
The cyberattack served as a catalyst for strengthening the college’s cybersecurity posture. Comprehensive security audits were conducted to identify vulnerabilities in the existing infrastructure. The college implemented multi-factor authentication across all systems to prevent unauthorized access. Enhanced security awareness training was implemented for all staff, students, and faculty. This proactive approach to bolstering cybersecurity safeguards the college from future attacks and demonstrates a commitment to safeguarding its assets.
Ouch! A Massachusetts community college just lost a hefty $800,000 in a phishing email attack. This unfortunately highlights the ongoing threat of cybercrime, and while the Department of Justice Offers Safe Harbor for MA Transactions here might offer some potential recourse, the unfortunate reality is that this kind of financial damage is very real. It really underscores how important strong cybersecurity measures are for institutions of all sizes.
Key Phases of the Recovery Process
The recovery process involved several key phases, each with specific objectives and timelines.
| Phase | Description | Timeline |
|---|---|---|
| Initial Response | Isolate compromised systems, contain the breach, and notify affected parties. | First 24-48 hours |
| Damage Assessment | Evaluate the extent of data loss, financial impact, and potential legal liabilities. | First week |
| Data Recovery and Restoration | Retrieve lost data, restore systems, and implement backup procedures. | Weeks 2-4 |
| Financial Recovery | Assess financial losses, file claims with insurance providers, and explore legal options. | Ongoing |
| Security Enhancement | Implement improved security protocols, conduct vulnerability assessments, and enhance staff training. | Ongoing |
Communication Strategy with Stakeholders
Effective communication with students, faculty, staff, and the wider community was crucial throughout the recovery process. The college established a dedicated communication channel, utilizing email, social media, and town hall meetings to provide updates and address concerns transparently. This proactive approach fostered trust and maintained a sense of community during a challenging time. The college ensured that all stakeholders were informed of the situation, steps taken, and future plans.
Lessons Learned and Prevention
The devastating phishing attack that cost Massachusetts Community College over $800,000 serves as a stark reminder of the ever-evolving threat landscape in cybersecurity. Learning from this incident is crucial for other educational institutions to strengthen their defenses and prevent similar breaches. This analysis delves into key lessons learned, best practices, and proactive measures to fortify cybersecurity posture.
Key Lessons Learned
The attack highlighted several critical vulnerabilities. The primary lesson is the importance of robust security protocols and employee training to mitigate the risk of phishing attacks. A deep dive into the attack reveals that insufficient staff training on identifying phishing emails, coupled with a lack of multi-factor authentication, significantly contributed to the breach.
Best Practices for Strengthening Cybersecurity Defenses
Implementing a multi-layered approach to cybersecurity is paramount. This involves more than just email filters; it encompasses a comprehensive strategy that combines technology, training, and procedures. This multi-faceted approach must include:
- Implementing strong authentication protocols: Mandatory use of multi-factor authentication (MFA) across all accounts is essential. MFA adds an extra layer of security, making it significantly harder for attackers to gain unauthorized access, even if they have compromised a username and password.
- Enhancing email security: Implementing advanced email filtering solutions that can detect and block suspicious emails is critical. This includes employing technologies that analyze email content for malicious code or patterns, as well as those that examine sender reputations and email header information.
- Regular security awareness training: Regular training sessions are crucial for staff and students to recognize phishing attempts. This should include real-world examples of phishing emails, the techniques used by attackers, and the importance of reporting suspicious activity. This education should be ongoing and updated to address emerging threats.
- Establishing incident response plans: Developing and regularly testing a comprehensive incident response plan is vital. This plan should Artikel procedures for identifying, containing, and recovering from cyberattacks, ensuring a swift and organized response.
Proactive Measures to Prevent Similar Phishing Attacks
Proactive measures are key to preventing future incidents. These include:
- Employing advanced threat intelligence: Staying updated on the latest phishing tactics and techniques through reputable sources is critical. This enables institutions to proactively adapt their defenses to counter emerging threats.
- Regular security audits and vulnerability assessments: Proactive security audits and vulnerability assessments are crucial to identify and address potential weaknesses in the system before attackers exploit them. Regular testing of security measures, including firewalls, intrusion detection systems, and anti-virus software, ensures their continued effectiveness.
- Implementing security information and event management (SIEM) systems: Implementing SIEM systems allows for centralized monitoring of security events and potential threats, providing a real-time view of activity across the network and enabling swift identification of suspicious patterns.
Improving Staff Training on Identifying Phishing Attempts
Thorough training is essential to empower staff to recognize and report phishing attempts.
- Simulated phishing exercises: Conduct regular simulated phishing exercises to test the effectiveness of training and identify areas for improvement. These exercises should be realistic and engaging to replicate real-world scenarios.
- Providing practical examples: Use real-world examples of successful and unsuccessful phishing attempts to highlight the subtle clues that often indicate a fraudulent email. Provide clear guidelines on how to recognize suspicious email characteristics, such as poor grammar, misspellings, urgent tones, and unexpected attachments.
- Incorporating regular updates: Ensure the training materials are regularly updated to reflect the latest phishing techniques and trends.
Updating and Enhancing Existing Security Protocols
Security protocols must be adaptable and evolve with emerging threats.
- Regular protocol reviews: Conduct periodic reviews of existing security protocols to identify outdated or ineffective measures. Ensure that protocols are aligned with current best practices and emerging threats.
- Implementing multi-factor authentication (MFA): Enforce the use of MFA for all sensitive accounts and systems to enhance security. This adds an additional layer of security, making it more difficult for attackers to access accounts even if they have obtained passwords.
- Regular software updates: Ensure all software is updated with the latest security patches to address vulnerabilities. This proactive measure helps close potential entry points for attackers.
Importance of Regular Security Awareness Training, Massachusetts community college loses 800000 via phishing email cyber attack
Regular security awareness training for all staff and students is critical. This approach instills a security-conscious culture, making the institution a harder target for attacks.
- Creating a security-conscious culture: A security-conscious culture promotes vigilance and proactive reporting of suspicious activity.
- Enhancing overall security posture: Regular training fosters a culture of security awareness, empowering all members of the community to identify and report potential threats, thereby significantly enhancing the overall security posture of the institution.
Summary of Lessons Learned
| Aspect of Security | Lessons Learned |
|---|---|
| Email Security | Implement advanced filtering, improve training on identifying phishing emails. |
| Authentication | Enforce multi-factor authentication (MFA) for all accounts. |
| Staff Training | Conduct regular, realistic simulated phishing exercises, and provide up-to-date training materials. |
| Incident Response | Develop and regularly test a comprehensive incident response plan. |
| Proactive Measures | Employ advanced threat intelligence, conduct regular security audits, and implement SIEM systems. |
Cybersecurity Best Practices: Massachusetts Community College Loses 800000 Via Phishing Email Cyber Attack
Protecting against cyber threats requires a proactive and multifaceted approach. This involves implementing robust cybersecurity measures across all facets of operations, from user behavior to system infrastructure. A strong cybersecurity posture is crucial for maintaining data integrity, preventing financial losses, and safeguarding the reputation of an institution.
Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) is a critical security measure that adds an extra layer of protection beyond a simple username and password. It requires users to provide two or more verification factors to access accounts or systems. This significantly reduces the risk of unauthorized access, even if attackers obtain a user’s password. MFA strengthens security by requiring additional authentication methods like security tokens, biometric scans, or one-time codes.
Implementing MFA is a cost-effective and highly impactful step to enhance security posture.
Software and System Updates
Regularly updating software and systems is paramount to patching security vulnerabilities. Cybercriminals constantly develop new methods to exploit weaknesses in outdated software. These updates often include crucial security patches that address known vulnerabilities, making systems more resistant to attacks. Proactive updates ensure that the institution’s systems are equipped with the latest security defenses. Failing to update systems leaves them vulnerable to attacks, making it a significant lapse in cybersecurity best practices.
Strong Passwords and Password Management
Creating strong passwords and implementing password management practices are essential elements of a robust cybersecurity strategy. Complex passwords, incorporating a mix of uppercase and lowercase letters, numbers, and symbols, are more difficult for attackers to crack. Password managers can generate and store strong passwords, providing an easy way to maintain secure credentials for various accounts. By implementing strong password practices, the risk of account compromise significantly reduces.
Using a password manager automates this process and helps users avoid weak or reused passwords.
Email Security Measures
Strong email security measures are vital in preventing phishing attacks and other email-borne threats. Implementing email filtering solutions, including spam filters and anti-phishing tools, is critical. These tools can identify and block suspicious emails, reducing the risk of malicious content reaching users’ inboxes. Regularly training employees on identifying phishing attempts and reporting suspicious emails is also essential.
This employee education can significantly enhance the organization’s defenses against email-based attacks.
Incident Response Plan
Developing a comprehensive incident response plan is crucial for handling security breaches and other incidents. This plan should Artikel procedures for detecting, responding to, and recovering from cyberattacks. The plan should include contact information for key personnel, procedures for containing the breach, and steps for restoring systems. A well-defined incident response plan allows institutions to respond effectively and efficiently to any security incident, minimizing the impact and ensuring timely recovery.
Best Practices Summary
| Best Practice | Description |
|---|---|
| Multi-Factor Authentication (MFA) | Adds an extra layer of security by requiring multiple authentication factors. |
| Software and System Updates | Regularly updating software patches known vulnerabilities and improves security. |
| Strong Passwords and Password Management | Creating complex passwords and using password managers. |
| Email Security Measures | Implementing email filters, training, and reporting procedures. |
| Incident Response Plan | Developing a plan for detecting, responding to, and recovering from incidents. |
Data Backups and Disaster Recovery Planning
Regular data backups and disaster recovery planning are crucial for minimizing the impact of cyberattacks or other unforeseen events. Data backups allow for the restoration of lost or corrupted data, mitigating the potential financial and operational losses associated with a data breach. A robust disaster recovery plan Artikels the steps to take to restore critical systems and operations after a disaster.
This plan should include offsite storage locations for backups and procedures for quickly restoring systems. Data backups are essential for ensuring business continuity in the event of a cyber incident. A well-defined disaster recovery plan helps minimize downtime and ensures quick restoration of critical services.
Outcome Summary
In conclusion, the $800,000 loss suffered by the Massachusetts community college serves as a cautionary tale about the escalating threat of phishing attacks. The college’s response and recovery strategies, along with the lessons learned, offer valuable insights into mitigating similar risks. Ultimately, proactive cybersecurity measures and ongoing training are essential to safeguarding educational institutions from future cyberattacks. By implementing best practices, educational institutions can significantly reduce their vulnerability to phishing scams and protect their valuable resources.
Question Bank
Q: What are some common characteristics of phishing emails that targeted the college?
A: A thorough analysis of the phishing emails would be needed to identify specific characteristics, but often these include a sense of urgency, a request for personal information, and poor grammar or spelling. The specific characteristics of the emails used in this attack are not yet publicly known.
Q: How can institutions improve their security measures against phishing attempts?
A: Strengthening security measures requires a multi-pronged approach. This includes implementing multi-factor authentication, regularly updating software, training staff and students on identifying phishing attempts, and creating strong passwords.
Q: What are the potential long-term effects of this attack on student enrollment?
A: A loss of public trust could potentially impact student enrollment. However, the exact impact will depend on how the college handles the situation and communicates with students and the wider community.
Q: How does this compare to other cyberattacks on educational institutions?
A: Data on similar attacks and financial losses across various educational institutions could be analyzed to gain a comparative understanding. Publicly available data on such incidents would be needed to perform a comparison.




