
Medical Implants Super Vulnerable to Cyber Attacks
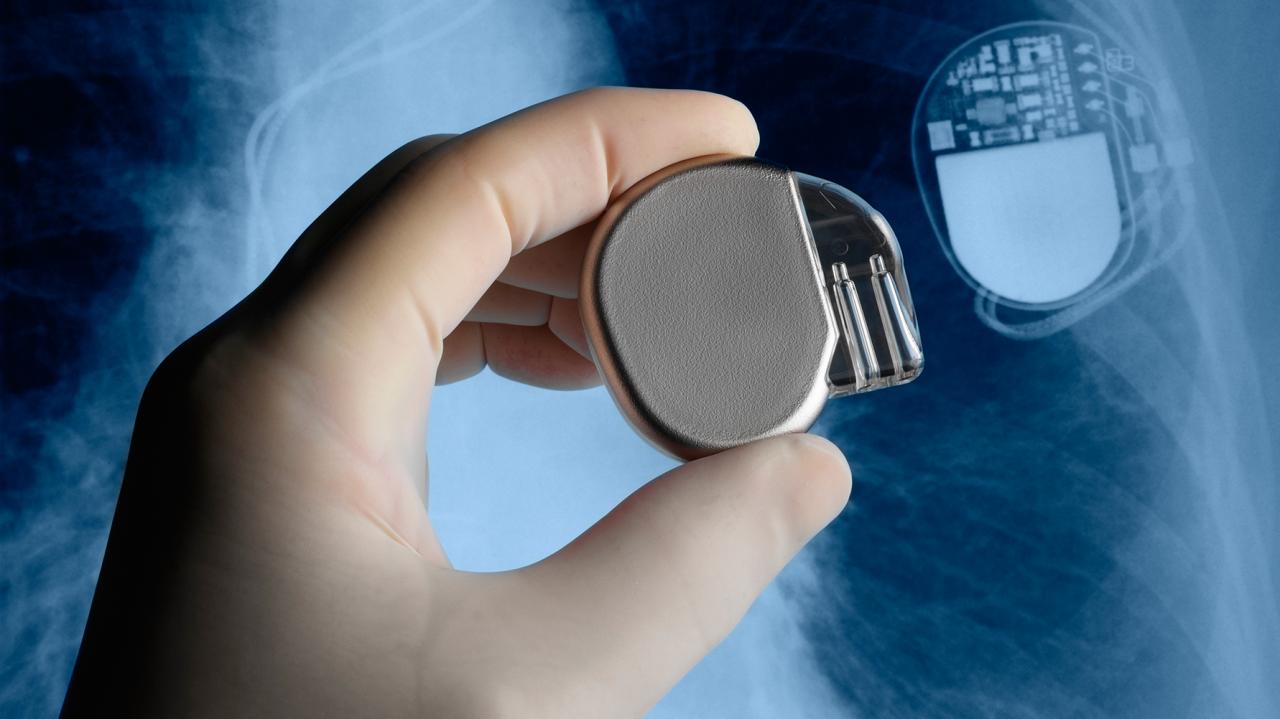
Medical implants are super vulnerable to cyber attacks. From pacemakers to insulin pumps, these life-saving devices are increasingly connected, making them prime targets for malicious actors. The potential consequences of a successful cyberattack range from incorrect dosage delivery to complete device malfunction, jeopardizing patient safety and well-being. This vulnerability highlights the urgent need for robust security measures and a comprehensive understanding of the threats.
This article delves into the vulnerabilities of various medical implants, examines existing security protocols, explores ethical considerations, and analyzes the regulatory landscape surrounding medical implant cybersecurity. We’ll also look at future trends and research directions in this critical area.
Vulnerability Assessment of Medical Implants

Medical implants, while crucial for patient well-being, present a unique set of cybersecurity challenges. These devices, often containing sensitive data and controlling vital bodily functions, are increasingly susceptible to cyberattacks. Understanding the vulnerabilities and potential consequences is paramount for ensuring patient safety and the reliability of these life-sustaining technologies.
Types of Vulnerable Medical Implants
Medical implants susceptible to cyberattacks encompass a broad range of devices. Pacemakers, insulin pumps, neurostimulators, and even some types of prosthetic limbs are vulnerable to malicious manipulation. These devices often rely on wireless communication, power lines, and embedded firmware, all of which could be exploited.
Attack Vectors
Several attack vectors can exploit vulnerabilities in medical implants. Wireless communication, often used for data transmission and remote adjustments, presents a significant attack surface. Malicious actors could potentially disrupt or manipulate the signals, leading to erroneous commands or data breaches. Power lines, crucial for powering the implants, could be tampered with, potentially causing malfunctions or even complete device failure.
Embedded firmware, the software residing within the device, could also be compromised. Sophisticated attacks might exploit vulnerabilities in the firmware to gain unauthorized control.
Potential Consequences of Successful Cyberattacks
The consequences of successful cyberattacks on medical implants are potentially severe. Incorrect dosage delivery from an insulin pump, for instance, could lead to life-threatening hypoglycemia or hyperglycemia. A malfunctioning pacemaker could cause serious cardiac arrhythmias, jeopardizing the patient’s life. Data breaches could compromise sensitive patient information, raising significant privacy concerns. The consequences of successful attacks are far-reaching and demand proactive security measures.
Comparative Vulnerability Assessment
| Implant Type | Wireless Vulnerability | Power Line Vulnerability | Firmware Vulnerability |
|---|---|---|---|
| Pacemaker | High (Wireless signals are easily intercepted) | Medium (Power fluctuations can affect operation) | High (Embedded firmware controls critical functions) |
| Insulin Pump | High (Wireless signals control dosage delivery) | Medium (Power fluctuations can cause inaccurate dosage) | High (Firmware controls crucial parameters like dosage) |
| Neurostimulator | High (Wireless signals regulate stimulation patterns) | Medium (Power fluctuations can disrupt stimulation) | High (Firmware dictates stimulation parameters and treatment) |
| Prosthetic Limb | Medium (Wireless communication for control and data) | Low (Typically powered by external sources) | Medium (Firmware for control systems, potentially accessible) |
Security Protocols and Countermeasures
Medical implants, while revolutionizing patient care, introduce unique cybersecurity vulnerabilities. Protecting these delicate systems from malicious actors is paramount. This requires robust security protocols, resilient designs, and continuous vigilance. A comprehensive approach encompassing encryption, access controls, and regular updates is essential to safeguarding these life-sustaining devices.
Existing Security Protocols, Medical implants are super vulnerable to cyber attacks
Medical implant designs often incorporate encryption methods to secure data transmission. These methods, such as Advanced Encryption Standard (AES), protect sensitive patient data and device commands during communication. Access controls, employing unique identifiers and authentication mechanisms, limit unauthorized access to the implant’s functionalities. These controls are crucial to prevent unauthorized manipulation of the implant’s programming.
Hardening Implant Designs
Several strategies can strengthen medical implant designs against cyber threats. Secure communication protocols, like TLS/SSL, establish encrypted channels between the implant and external devices, ensuring that all transmitted data remains confidential. Employing isolated systems within the implant minimizes the potential impact of a compromise in one area. This segregation reduces the risk of an attacker gaining control of the entire system.
Importance of Regular Updates
Regular software updates and security patches are critical for medical implants. These updates address vulnerabilities discovered after the initial release. Failure to implement these updates can expose the implant to exploitation by attackers. Maintaining a proactive approach to software maintenance is vital for ongoing security. Examples of this are seen in the constant updates to software in various medical devices to address new threats and vulnerabilities.
Comparison of Security Measures
| Security Measure | Effectiveness on Pacemakers | Effectiveness on Insulin Pumps | Effectiveness on Neurostimulators |
|---|---|---|---|
| Encryption | High – Protects data transmission, crucial for maintaining accurate heart rhythm. | High – Protects data transmission, critical for precise insulin delivery. | High – Protects data transmission, critical for safe and accurate nerve stimulation. |
| Access Controls | High – Prevents unauthorized changes to pacemaker settings. | High – Prevents unauthorized changes to insulin delivery profiles. | High – Prevents unauthorized changes to stimulation parameters. |
| Secure Communication Protocols | High – Crucial for remote monitoring and configuration. | High – Crucial for remote monitoring and configuration, essential for managing dosage. | High – Crucial for remote monitoring and configuration, vital for adapting stimulation patterns. |
| Isolated Systems | High – Limits the impact of a potential breach. | High – Limits the impact of a potential breach. | High – Limits the impact of a potential breach. |
| Regular Updates | High – Addresses vulnerabilities and enhances device performance. | High – Addresses vulnerabilities and enhances device performance. | High – Addresses vulnerabilities and enhances device performance. |
The effectiveness of each measure depends on the specific implant type and the implementation details. For example, the complexity of an insulin pump’s control algorithms will influence the level of sophistication required for its security protocols.
Ethical Considerations and Implications
The integration of technology into medical implants presents a paradigm shift, offering unprecedented possibilities but also introducing profound ethical and legal complexities. These implanted devices, while enhancing quality of life, are susceptible to cyberattacks, potentially jeopardizing patient safety, privacy, and the very trust inherent in the physician-patient relationship. Addressing these vulnerabilities requires a comprehensive understanding of the ethical implications, and a proactive approach from all stakeholders.The potential for harm from cyberattacks on medical implants extends beyond the technical realm, touching upon critical ethical and legal dimensions.
The safety and well-being of patients are paramount, demanding a robust framework to protect them from these emerging risks. Understanding the responsibilities of manufacturers, healthcare providers, and regulatory bodies is crucial to establishing a system of accountability and safeguarding patient rights.
Ethical Implications of Implant Vulnerabilities
The vulnerability of medical implants to cyberattacks raises serious ethical concerns regarding patient safety and privacy. A compromised implant could lead to incorrect diagnoses, inappropriate treatment, or even life-threatening complications. The potential for unauthorized access to sensitive patient data stored within or transmitted by these implants also poses a significant privacy risk.
Manufacturer Responsibility
Manufacturers of medical implants bear a significant responsibility in ensuring the security of their products. This includes proactive design and development of secure implants, implementing robust security protocols, and providing clear instructions on safe use and maintenance. Thorough testing and validation of security measures are crucial to minimize the risk of vulnerabilities being exploited. Furthermore, manufacturers should be transparent about potential vulnerabilities and take proactive measures to mitigate them.
Healthcare Provider Responsibility
Healthcare providers play a critical role in managing the security of implanted devices. They should implement appropriate security protocols within their facilities, educate patients and staff about potential risks, and adhere to best practices for managing and maintaining these devices. Providers should be trained on identifying and responding to potential cyberattacks, and they need to maintain clear communication channels with patients regarding implant security.
Medical implants are surprisingly vulnerable to cyberattacks, leaving patients at serious risk. Protecting these sensitive devices requires a proactive approach, like deploying AI code safety goggles – a crucial step to secure code. This is especially important given the potential for malicious actors to exploit vulnerabilities in medical devices, impacting patient safety. Thankfully, solutions like Deploying AI Code Safety Goggles Needed are emerging to help mitigate this risk and ensure the safety of medical implant code.
Ultimately, safeguarding these implants remains a critical area of focus.
Regulatory Body Responsibility
Regulatory bodies have a critical role in establishing and enforcing standards for the security of medical implants. This includes developing comprehensive security guidelines, conducting regular audits of implant manufacturers, and imposing penalties for non-compliance. Regulatory bodies must also stay abreast of evolving cybersecurity threats and adapt standards accordingly. Effective regulations should promote innovation in secure implant design and operation.
Potential Legal Ramifications
Cyberattacks on medical implants could lead to a range of legal ramifications, including product liability lawsuits, negligence claims, and violations of patient privacy laws. Patients harmed by a cyberattack may pursue legal action against the manufacturer, healthcare provider, or both. Understanding the legal implications is critical for all parties involved in the medical implant industry.
Potential Legal and Ethical Dilemmas
- Patient Consent and Disclosure: Patients may not fully understand the potential risks associated with cyberattacks on their implanted devices, raising questions about informed consent. Manufacturers and providers need to transparently disclose the risks and benefits of the technology.
- Liability and Accountability: Determining liability in cases of cyberattacks on implants can be complex. Who is responsible if a patient is harmed? Is it the manufacturer, the healthcare provider, or both? Clear legal frameworks are needed to establish accountability.
- Data Security and Privacy: Implanted devices often store and transmit sensitive patient data. Protecting this data from unauthorized access and ensuring compliance with privacy regulations is paramount. Protecting sensitive data within the implant’s operational system is crucial to avoid breaches and ensure patient privacy.
- Cost of Security Measures: Implementing robust security measures in medical implants can be expensive. Balancing the cost of security with the need to protect patient safety is a critical ethical and practical challenge.
Regulatory Landscape and Standards: Medical Implants Are Super Vulnerable To Cyber Attacks
The burgeoning field of medical implants demands a robust regulatory framework to ensure patient safety and the efficacy of these intricate devices. As cyber threats become increasingly sophisticated, ensuring the security of medical implants is paramount. A comprehensive regulatory landscape must address cybersecurity vulnerabilities and provide clear guidelines for manufacturers.The existing regulatory landscape for medical devices, while generally robust, has gaps in explicitly addressing cybersecurity for implantable devices.
This necessitates a proactive approach to establish standards and regulations that align with the evolving threat landscape. Compliance with these standards is critical for manufacturers to demonstrate their commitment to patient safety and uphold the integrity of the medical device ecosystem.
Existing Regulations and Standards for Medical Device Cybersecurity
Existing regulations, primarily focused on the safety and efficacy of medical devices, often lack explicit cybersecurity provisions. The Food and Drug Administration (FDA) in the United States, and various international organizations like the International Electrotechnical Commission (IEC), play crucial roles in defining safety standards for medical devices. These standards are frequently updated to reflect advancements in technology and evolving threats.
Examples of Regulatory Frameworks and their Impact on Implant Security
The FDA’s Quality System Regulation (QSR) and its emphasis on risk management procedures, while not explicitly cybersecurity focused, provide a foundation for manufacturers to incorporate cybersecurity considerations into their design and development processes. Similarly, international standards, such as IEC 60601-1, which Artikels general safety requirements for medical electrical equipment, can be adapted to include cybersecurity provisions. However, these frameworks need to be strengthened and expanded to address the unique vulnerabilities of implantable devices.
Importance of Compliance with Relevant Standards for Medical Implant Manufacturers
Compliance with cybersecurity standards is not just a regulatory requirement but a crucial aspect of responsible manufacturing. Manufacturers who adhere to these standards demonstrate a commitment to patient safety and data integrity. This commitment fosters trust among healthcare professionals and patients, ultimately enhancing the adoption of innovative medical implants. Failure to comply can result in severe consequences, including product recalls, legal action, and reputational damage.
Table Outlining Regulatory Bodies and their Roles in Medical Implant Cybersecurity
| Regulatory Body | Specific Role | Examples of Guidelines |
|---|---|---|
| Food and Drug Administration (FDA) | Sets standards for medical device safety and efficacy, including risk management. While not solely focused on cybersecurity, the FDA is actively addressing cybersecurity in its guidelines and guidance documents. | Premarket notification (510(k)) requirements, risk management strategies, and guidance documents on cybersecurity for medical devices. |
| International Electrotechnical Commission (IEC) | Develops international standards for electrical and electronic equipment, including medical devices. These standards often include cybersecurity aspects. | IEC 60601-1 (general safety requirements), IEC 62304 (software development for medical devices), and related cybersecurity standards under development. |
| European Union (EU) | Establishes regulations for medical devices, including cybersecurity aspects. The Medical Device Regulation (MDR) aims to strengthen safety and quality standards, which encompasses cybersecurity considerations. | Medical Device Regulation (MDR), and associated guidelines on cybersecurity. |
Future Trends and Research Directions

The burgeoning field of medical implant cybersecurity faces a dynamic landscape of evolving threats and opportunities. Advancements in technology, coupled with increasing reliance on these implants, necessitate proactive research and development to ensure their safety and efficacy. This section explores emerging trends, potential challenges, and ongoing research to illuminate the future trajectory of medical implant security.The need for robust security protocols for medical implants is paramount.
This stems from the critical role these devices play in patient care and the potential for catastrophic consequences from cyberattacks. Malicious actors could potentially disrupt essential functionalities, compromise patient data, or even cause physical harm. Therefore, future research must prioritize the development of impenetrable defenses and resilient systems to mitigate these risks.
Emerging Technologies and Research Areas
Numerous technological advancements hold the promise of enhancing the security of medical implants. Advanced encryption techniques, incorporating quantum-resistant algorithms, will be crucial to safeguard sensitive data transmitted between implants and external systems. Secure communication protocols, such as those based on blockchain technology, can provide enhanced transparency and immutability, making it harder for attackers to tamper with data.
Secure Communication Protocols
Secure communication protocols for medical implants are evolving rapidly. The development of robust, tamper-proof communication channels is essential. Researchers are investigating methods to authenticate devices, encrypt data in transit, and ensure data integrity. This includes exploring the use of advanced cryptographic techniques to resist known and emerging attacks. One promising area is the utilization of blockchain technology, which could provide a decentralized and tamper-proof record of implant interactions.
This approach could significantly enhance the security and trust in the system.
Advanced Encryption Techniques
The development of quantum-resistant encryption algorithms is a crucial area of research. Traditional encryption methods may become vulnerable to attacks from quantum computers in the future. Researchers are actively working on cryptographic techniques that are resistant to these emerging threats. These algorithms will be essential to protect sensitive data transmitted by implants and stored within the devices themselves.
This includes research into post-quantum cryptography, exploring the implementation of quantum-safe encryption methods for securing implant data.
Potential Future Challenges and Opportunities
The increasing sophistication of cyberattacks poses a significant challenge to medical implant security. As attackers develop more sophisticated techniques, researchers must constantly adapt and develop more advanced countermeasures. This requires ongoing vigilance, collaborative efforts between researchers, manufacturers, and regulatory bodies, and investment in cutting-edge technologies. Opportunities arise in the development of new standards and regulations that can foster innovation and ensure interoperability across different implant types and manufacturers.
Ongoing Research in the Field of Medical Implant Security
Numerous research institutions and organizations are actively investigating the security of medical implants. This includes universities, hospitals, and technology companies, all collaborating to advance the state-of-the-art in implant security. Research efforts are focused on developing secure communication protocols, robust encryption techniques, and advanced authentication methods. The results of this research are critical for mitigating the risks of cyberattacks on medical implants.
Medical implants are surprisingly vulnerable to cyberattacks, leaving patients at risk. Protecting these sensitive devices is crucial, and initiatives like the Department of Justice Offers Safe Harbor for MA Transactions ( Department of Justice Offers Safe Harbor for MA Transactions ) could potentially offer some safeguards, though their direct application to implantable medical devices is still unclear. Ultimately, the vulnerability of these implants highlights the need for stronger security measures in the healthcare sector.
A key aspect is developing security protocols compatible with existing medical infrastructure.
Timeline for Expected Advancements
Predicting precise timelines for advancements in medical implant cybersecurity is challenging, as research and development efforts are constantly evolving. However, based on current trends, significant progress is anticipated over the next decade. Within the next five years, more robust encryption standards and secure communication protocols will likely be adopted. Within the next seven to ten years, quantum-resistant encryption techniques will likely become more prevalent.
Medical implants, unfortunately, are incredibly vulnerable to cyberattacks. This isn’t just a theoretical threat; recent vulnerabilities in systems like Azure Cosmos DB, as detailed in Azure Cosmos DB Vulnerability Details , highlight the serious risk to interconnected medical devices. These vulnerabilities could have devastating consequences, emphasizing the urgent need for stronger security measures around these implantable technologies.
This timeline reflects the ongoing research and development efforts in the field. However, advancements will depend on sustained investment in research and collaboration.
Last Point
In conclusion, the vulnerability of medical implants to cyberattacks is a serious and growing concern. The potential harm to patients is significant, necessitating a proactive and multi-faceted approach to bolstering security. Manufacturers, healthcare providers, and regulatory bodies all share responsibility in mitigating these risks. The development of robust security protocols, adherence to stringent regulations, and ongoing research are crucial to ensuring the safety and reliability of these vital medical devices.
Frequently Asked Questions
What are some common types of medical implants susceptible to cyberattacks?
Pacemakers, insulin pumps, neurostimulators, and implantable defibrillators are among the most vulnerable types of medical implants. Their reliance on wireless communication and embedded firmware makes them susceptible to various attack vectors.
What are the potential consequences of a successful cyberattack on a medical implant?
The consequences can range from incorrect drug dosage to complete device malfunction, causing severe harm to the patient. Data breaches are also a concern, potentially exposing sensitive patient information.
What are some existing security protocols employed in medical implant designs?
Current security protocols often include encryption methods and access controls. However, these measures are not always sufficient to deter sophisticated attacks.
What is the role of regulatory bodies in medical implant cybersecurity?
Regulatory bodies like the FDA and international standards organizations play a critical role in setting guidelines and standards for medical device cybersecurity. Compliance with these standards is essential for manufacturers.





