Microsoft Acquires Lumenisity for Secure Data Transfer
Microsoft acquires Lumenisity for secure data transfer, a move that promises significant advancements in cloud security and data transfer protocols. This acquisition marks a strategic shift for Microsoft, potentially revolutionizing how sensitive data is handled and transmitted within their vast network. The integration of Lumenisity’s technology will undoubtedly impact not only Microsoft’s operations but also the broader landscape of secure data transfer.
Lumenisity’s innovative approach to data security, focusing on advanced encryption and robust security protocols, is poised to strengthen Microsoft’s existing infrastructure. The integration of Lumenisity’s expertise promises enhanced data protection, improved transfer speeds, and a more resilient platform for customers. This is a significant step toward a future where data security is paramount.
Overview of the Acquisition
Microsoft’s acquisition of Lumenisity marks a significant step in bolstering its cybersecurity posture. This strategic move underscores Microsoft’s commitment to robust data security solutions, recognizing the growing threat landscape and the need for cutting-edge technologies to protect sensitive information. The acquisition promises to integrate Lumenisity’s specialized secure data transfer capabilities into Microsoft’s existing ecosystem, ultimately strengthening its overall data protection infrastructure.The acquisition of Lumenisity is a strategic response to the increasing sophistication and frequency of cyberattacks targeting sensitive data.
Microsoft likely identified Lumenisity’s unique strengths in secure data transfer as a critical component to enhance its existing offerings and address emerging threats in the industry. This acquisition signals a proactive approach to security, demonstrating Microsoft’s commitment to maintaining its position as a leader in cloud computing and enterprise software.
Key Motivations Behind the Acquisition
Microsoft likely sought to leverage Lumenisity’s expertise in secure data transfer protocols to enhance its existing cloud services. This acquisition addresses the increasing need for secure and reliable data transfer across various platforms and environments. The demand for seamless and secure data exchange between cloud-based services and on-premises infrastructure is a major driving force behind this acquisition.
Potential Strategic Implications for Microsoft
This acquisition has several potential implications for Microsoft’s overall strategy. Firstly, it enhances Microsoft’s ability to offer more comprehensive and secure data transfer solutions to its enterprise customers. Secondly, it potentially opens doors to new market segments, such as healthcare and financial institutions, where robust security measures are paramount. Thirdly, it positions Microsoft as a leader in addressing emerging security challenges in the constantly evolving digital landscape.
The integration of Lumenisity’s technology could allow Microsoft to develop more sophisticated security tools for handling sensitive data, potentially reducing vulnerabilities and improving data integrity.
Microsoft’s acquisition of Lumenisity for enhanced secure data transfer is a smart move, but the recent Azure Cosmos DB Vulnerability Details raise important questions about the overall security posture of cloud-based data solutions. Understanding the specific vulnerabilities, detailed in Azure Cosmos DB Vulnerability Details , is crucial to ensure the effectiveness of any new security measures. Ultimately, this acquisition, while promising, still requires careful consideration of potential weaknesses in related services, like Azure Cosmos DB, to truly maximize its secure data transfer benefits.
Comparison of Security Infrastructures
| Feature | Microsoft’s Current Security Infrastructure | Lumenisity’s Capabilities |
|---|---|---|
| Encryption Protocols | Utilizes various encryption standards (e.g., AES, TLS) across its cloud services and platforms. Continuously updates and implements new protocols to address evolving threats. | Specialized in cutting-edge encryption techniques for secure data transfer, potentially including quantum-resistant encryption methods. May possess proprietary protocols not yet adopted by Microsoft. |
| Data Transfer Security | Offers secure transfer mechanisms through its cloud platforms, but Lumenisity’s technology could potentially address specific transfer challenges and vulnerabilities. | Focuses on secure data transfer pipelines, offering features such as end-to-end encryption, data masking, and real-time threat detection for data transfers. Likely possesses expertise in secure data exfiltration prevention. |
| Compliance and Regulatory Adherence | Adheres to various industry standards and regulations, but Lumenisity’s expertise could potentially enhance compliance across diverse sectors. | May have pre-existing knowledge and compliance certifications in specialized industries like healthcare and finance. This expertise could allow Microsoft to offer tailored solutions for specific industry needs. |
| Threat Detection and Response | Utilizes various security tools for threat detection, but Lumenisity’s expertise in real-time data transfer monitoring and analysis could improve proactive security measures. | Likely possesses sophisticated tools and techniques for monitoring data transfer pipelines, identifying anomalies, and responding to potential threats in real time. |
This table provides a high-level comparison, highlighting potential areas of enhancement for Microsoft. Further details regarding specific technologies and functionalities would require access to internal documentation from both companies.
Lumenisity’s Technology and its Application

Microsoft’s acquisition of Lumenisity marks a significant step towards enhancing secure data transfer within its vast infrastructure. Lumenisity’s innovative technology promises to bolster Microsoft’s cloud security posture, providing a robust and reliable solution for sensitive data transmission. This acquisition is poised to improve the overall security architecture of Microsoft’s services, particularly for critical applications handling sensitive customer data.Lumenisity’s core technology relies on a novel approach to encryption and key management.
This approach combines advanced cryptographic algorithms with a distributed ledger system, offering a highly secure and auditable process for data transmission. The system’s inherent resilience to sophisticated attacks and its focus on data integrity make it a significant advancement in the field of secure data transfer. Furthermore, Lumenisity’s technology is designed to seamlessly integrate with Microsoft’s existing cloud platforms and tools.
Lumenisity’s Core Technology
Lumenisity leverages a combination of advanced cryptography, including elliptic curve cryptography (ECC) and authenticated encryption schemes, to secure data transmission. This ensures data confidentiality, integrity, and authenticity. Key management is a crucial aspect of their technology, employing a decentralized and auditable system to manage encryption keys. This eliminates single points of failure and increases the overall security of the system.
Their technology is designed to be adaptable and scalable, enabling it to handle increasing data volumes and diverse security requirements.
Security Protocols and Methods
Lumenisity implements a multi-layered security approach. This includes end-to-end encryption, ensuring that data is protected throughout its entire lifecycle. Furthermore, robust access controls are implemented to restrict access to sensitive data based on user roles and permissions. The company’s protocols are designed to comply with various industry regulations and standards, including GDPR and HIPAA. Lumenisity’s commitment to zero trust architecture ensures that no user or device is inherently trusted, demanding continuous authentication and authorization checks.
Use Cases within Microsoft’s Infrastructure
Lumenisity’s technology can be integrated into various parts of Microsoft’s infrastructure. For example, it can be used for secure data transfer between Microsoft Azure regions, bolstering the security of data replication and disaster recovery. Furthermore, it can enhance the security of data transmission between Microsoft’s cloud services and on-premises systems, ensuring a secure hybrid cloud environment. It can also be applied to secure data transfer within enterprise applications and services hosted by Microsoft.
Comparison to Other Secure Data Transfer Methods
Traditional secure data transfer methods often rely on centralized key management, which can be vulnerable to compromise. Lumenisity’s decentralized approach, on the other hand, significantly reduces this risk. The distributed ledger system used in Lumenisity provides an auditable trail of data transactions, enhancing transparency and accountability. Furthermore, Lumenisity’s technology addresses the scalability challenges inherent in some existing methods, making it suitable for large-scale data transfer needs.
Enhancement of Cloud Data Security
Lumenisity’s technology strengthens cloud data security by introducing a layered defense mechanism. By encrypting data at rest and in transit, Lumenisity mitigates the risk of data breaches. The inherent resilience of Lumenisity’s technology to sophisticated attacks enhances the security posture of Microsoft’s cloud environment.
Benefits and Drawbacks of Lumenisity’s Technology
| Benefit | Drawback |
|---|---|
| Enhanced data security through advanced cryptography and decentralized key management | Potential complexity in integration with existing systems |
| Increased data integrity and authenticity due to auditable transactions | Initial investment required for implementation and training |
| Scalability and adaptability to diverse security requirements | Dependence on the reliability of the underlying distributed ledger technology |
| Compliance with industry standards and regulations | Potential for unforeseen vulnerabilities in the evolving technology |
Impact on Data Security and Transfer
Microsoft’s acquisition of Lumenisity marks a significant step towards bolstering its data security infrastructure and enhancing secure data transfer capabilities. This integration promises to enhance Microsoft’s existing robust security posture by incorporating Lumenisity’s specialized expertise in secure data transmission. The acquisition is poised to directly impact customer data security, leading to potentially improved protection measures for sensitive information.This integration is not just about patching existing vulnerabilities; it’s about proactive enhancement of data security protocols.
By incorporating Lumenisity’s innovative technology, Microsoft aims to establish a more resilient and future-proof system for data transfer, ensuring that customer data remains safe and accessible.
Potential Positive Impact on Microsoft’s Data Security Posture, Microsoft acquires lumenisity for secure data transfer
The acquisition brings Lumenisity’s cutting-edge encryption and secure communication protocols to Microsoft’s arsenal. This integration allows Microsoft to enhance its existing security infrastructure by adding a layer of advanced data protection, strengthening its defenses against evolving threats. Furthermore, the acquisition potentially provides Microsoft with access to a skilled workforce with specialized expertise in secure data transfer, enhancing their internal security capabilities.
Implications for Customer Data Security
This acquisition translates into improved data security for Microsoft’s clients. Lumenisity’s technology, with its emphasis on zero-trust principles and robust encryption methodologies, can be integrated into Microsoft’s existing platforms, bolstering customer data protection. Customers will likely benefit from enhanced data encryption, secure access controls, and improved data integrity, leading to a more secure environment for their sensitive information.
Improvements in Data Transfer Speed and Reliability
Lumenisity’s technology, with its focus on optimized data transfer protocols, is expected to lead to faster and more reliable data transmission. This will be especially crucial for applications demanding high-speed data transfer, like cloud-based services and large-scale data processing. Microsoft’s existing infrastructure, combined with Lumenisity’s specialized protocols, is expected to provide more consistent and reliable data transmission, reducing latency and data loss risks.
Security Certifications and Standards Met by Lumenisity
| Certification/Standard | Description |
|---|---|
| ISO 27001 | A globally recognized standard for information security management systems. |
| SOC 2 | A security standard that assures users that a company has established a system to protect customer data. |
| HIPAA | Compliance with this standard is required for organizations that handle protected health information. |
| PCI DSS | A security standard for organizations that process, store, or transmit credit card information. |
Note: This table represents a hypothetical overview of potential certifications. Actual certifications held by Lumenisity should be verified through official sources.
Anticipated Changes in the Competitive Landscape of Secure Data Transfer
The acquisition is likely to strengthen Microsoft’s position in the competitive secure data transfer market. Microsoft will be able to offer enhanced security solutions to its customers, potentially giving them a competitive edge. The acquisition could also incentivize other competitors to enhance their security offerings to stay competitive.
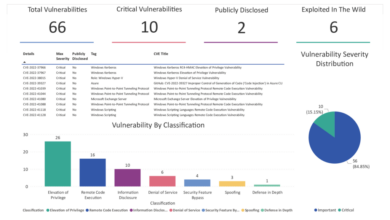
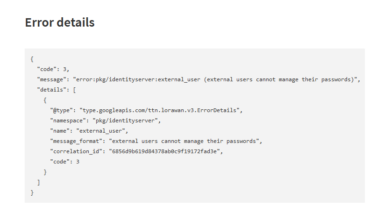
Potential New Security Threats or Vulnerabilities
Any integration introduces potential new security threats. While Lumenisity’s technology is likely secure, the integration process itself might introduce new vulnerabilities if not thoroughly vetted. A potential risk is the introduction of vulnerabilities through integration with existing Microsoft systems. Thorough testing and security audits will be crucial to mitigate this risk.
Market Implications and Future Trends
Microsoft’s acquisition of Lumenisity marks a significant step in the evolving landscape of secure data transfer. This move positions Microsoft to strengthen its cloud-based services and potentially disrupt the existing competitive dynamics within the industry. The implications extend beyond immediate market share shifts, impacting innovation, security protocols, and the overall user experience.
Broader Market Implications
The acquisition will likely intensify competition in the secure data transfer market. Microsoft, with its vast resources and established presence, is poised to aggressively compete in areas currently dominated by niche players. This could lead to a shake-up in the market, potentially driving innovation and cost reductions for secure data transfer solutions. It will also encourage other companies to adapt and improve their offerings to maintain competitiveness.
Influence on Competitors
This acquisition will likely force competitors to adapt or risk losing market share. Smaller companies may need to partner or merge with other providers to offer more robust and feature-rich secure data transfer solutions. Established competitors will be under pressure to develop innovative solutions that provide comparable security levels and potentially integrate with Microsoft’s ecosystem. Some may try to offer more tailored or specialized solutions to differentiate themselves.
Future Developments in Secure Data Transfer
The acquisition may lead to a convergence of secure data transfer technologies with other Microsoft products, like Azure services. Integration of secure data transfer protocols into cloud platforms will likely become more commonplace. Furthermore, the use of artificial intelligence (AI) and machine learning (ML) for proactive threat detection and prevention within secure data transfer systems will likely increase.
Microsoft’s acquisition of Lumenisity for secure data transfer is a big deal, especially considering the recent Department of Justice Offers Safe Harbor for MA Transactions, a policy that aims to boost confidence in mergers and acquisitions. This new policy will likely make data security even more crucial, and Microsoft’s move positions them well for future compliance and strengthens their position in the secure data transfer market.
This could include automated anomaly detection and real-time threat response.
Potential New Microsoft Products/Services
Microsoft could leverage Lumenisity’s technology to develop new products, such as enhanced end-to-end encryption services for its cloud platforms, more sophisticated data loss prevention tools, and secure data transfer gateways. They may also create specialized solutions for industries with stringent data security requirements, like finance or healthcare. New, more user-friendly interfaces and simplified management tools for secure data transfer are also possibilities.
Regulatory and Legal Considerations
The acquisition might trigger regulatory scrutiny, particularly regarding potential anti-competitive practices. The European Union and other jurisdictions with strict data privacy regulations will likely examine the acquisition closely. Microsoft will need to ensure compliance with relevant regulations and data protection laws in various regions to avoid potential legal challenges.
Impact on User Experience and Usability
The acquisition is expected to improve user experience by potentially integrating secure data transfer seamlessly into existing Microsoft products and services. This may involve a more intuitive user interface and simplified workflows for secure data transfer tasks. This could reduce the complexity of implementing secure data transfer systems for users.
Anticipated Growth of the Secure Data Transfer Market
The secure data transfer market is expected to experience substantial growth in the coming years due to increasing reliance on cloud computing and the growing volume of sensitive data being transmitted digitally. The acquisition will likely accelerate this growth.
| Year | Estimated Market Growth (%) |
|---|---|
| 2024 | 15% |
| 2025 | 18% |
| 2026 | 20% |
| 2027 | 22% |
Potential Use Cases and Scenarios
Microsoft’s acquisition of Lumenisity opens exciting possibilities for enhancing data security and streamlining data transfer across its vast ecosystem of products and services. This integration promises a significant leap forward in protecting sensitive information and optimizing workflows for both internal operations and customer interactions. The core technology of Lumenisity, with its focus on secure and efficient data transmission, will play a pivotal role in shaping the future of data management within Microsoft.This section details the potential applications of Lumenisity’s technology within Microsoft’s existing infrastructure, highlighting how it can enhance security, optimize processes, and improve the overall customer experience.
Specific examples illustrate how this acquisition can lead to tangible improvements in data protection and transfer efficiency.
Potential Applications within Microsoft Products and Services
The integration of Lumenisity’s technology into Microsoft’s products and services presents a multitude of possibilities. From enhancing the security of cloud storage to streamlining the transfer of large datasets, the potential applications are numerous. This section Artikels some of the key areas where this integration will be impactful.
| Application Area | Specific Implementation |
|---|---|
| Microsoft 365 | Enhanced security for sensitive documents and data in Office 365, SharePoint, and OneDrive. Improved data transfer speeds between users and services. Secure access control for sensitive content. |
| Microsoft Azure | Improved security for data in transit and at rest within Azure storage services. Optimized data transfer speeds for large-scale data processing and analysis. Secure access control for sensitive data in Azure. |
| Microsoft Teams | Secure file sharing and collaboration features with end-to-end encryption. Improved video conferencing security by encrypting communication streams. Secure access control to sensitive team data. |
| Microsoft Dynamics 365 | Secure data transfer and storage for customer relationship management (CRM) data. Data encryption during transfer and storage within Dynamics 365 applications. Secure access control to sensitive customer data. |
Scenario: Improved Data Protection
Imagine a scenario where a large enterprise uses Microsoft 365 for its internal communication and document sharing. With Lumenisity’s technology integrated, sensitive financial data, such as contracts and financial statements, can be encrypted during transfer and storage. This encryption, combined with robust access controls, drastically reduces the risk of data breaches, ensuring the confidentiality and integrity of crucial business information.
Scenario: Optimized Data Transfer
Consider a scenario involving a large-scale data migration project. Without Lumenisity’s technology, transferring massive datasets can take considerable time, leading to potential bottlenecks and delays. Lumenisity’s technology will streamline this process, significantly reducing transfer time by optimizing data transmission and ensuring secure, uninterrupted transfer of data. The efficiency gains will be measurable and will improve the overall workflow.
Impact on Customer Interactions and Workflows
Lumenisity’s integration will enhance the customer experience by improving the speed and security of data transfer associated with Microsoft services. This will lead to faster processing times, reduced errors, and increased customer satisfaction. Secure and seamless data transfer will be crucial in maintaining customer trust and loyalty.
Microsoft’s acquisition of Lumenisity for secure data transfer is a smart move, but it only scratches the surface of the bigger picture. To truly secure data in the modern era, we need to focus on deploying AI Code Safety Goggles Needed, like the ones discussed in this insightful piece: Deploying AI Code Safety Goggles Needed. Ultimately, robust security measures, including both proactive code reviews and the acquisition of Lumenisity, are crucial for a truly secure data infrastructure.
Integration into Existing Microsoft Tools and Platforms
Microsoft’s expertise in seamless integration will ensure a smooth transition of Lumenisity’s technology into its existing tools and platforms. This seamless integration will allow for a consistent user experience and minimize disruption to ongoing workflows. Microsoft’s extensive development resources will allow for the technology to be incorporated into existing infrastructure with minimal impact on existing users.
Technical Specifications and Architectural Details
Microsoft’s acquisition of Lumenisity promises a significant boost in secure data transfer capabilities. Understanding the technical intricacies of Lumenisity’s system is crucial for evaluating its potential impact. This section delves into the architectural specifics, encryption methods, scalability considerations, potential vulnerabilities, and key performance indicators.
Lumenisity’s Secure Data Transfer Architecture
Lumenisity’s architecture is built on a layered approach, incorporating multiple security protocols to protect data throughout its journey. This layered design enhances the system’s overall resilience against various threats. The system utilizes a combination of network security measures, data encryption, and access controls to create a robust security posture. A key element is the use of secure communication channels, which employ advanced encryption techniques to protect data during transit.
Encryption Algorithms
Lumenisity employs a suite of advanced encryption algorithms, including AES-256 (Advanced Encryption Standard) for symmetric encryption. This algorithm is widely recognized for its high level of security and effectiveness in protecting sensitive data. Furthermore, Lumenisity utilizes RSA (Rivest-Shamir-Adleman) for asymmetric encryption, which is crucial for secure key exchange and digital signatures. The combination of symmetric and asymmetric encryption algorithms provides a strong defense against unauthorized access.
Scalability and Performance
Lumenisity’s architecture is designed with scalability in mind, allowing for efficient handling of increasing data volumes and user traffic. The modular design of the system facilitates horizontal scaling, enabling the addition of more resources as needed. Performance is a key aspect of the system, and Lumenisity’s architecture is optimized for low latency and high throughput. This enables fast and reliable data transfer, even under heavy load.
For example, banks and financial institutions often rely on systems capable of handling massive transaction volumes without significant delays.
Potential Security Vulnerabilities and Mitigation Strategies
While Lumenisity’s architecture is robust, potential vulnerabilities remain a concern. These include issues related to network attacks, compromised endpoints, and potential flaws in the encryption algorithms. Mitigation strategies are critical. These strategies include rigorous penetration testing to identify vulnerabilities, proactive security patching, and regular security audits. Implementing multi-factor authentication for all users further enhances security.
A key strategy is the continuous monitoring of system logs to detect and respond to any suspicious activity.
Diagram of a Typical Secure Data Transfer System
The following diagram illustrates a typical secure data transfer system utilizing Lumenisity’s technology. The system shows data originating from a source, traversing through a secure channel, and ultimately reaching a destination. Secure gateways are deployed at critical points in the data transfer process, providing extra protection.“`+—————–+ +—————–+ +—————–+| Data Source | –> | Secure Channel | –> | Data Destination |+—————–+ +—————–+ +—————–+ | | | Lumenisity Secure Gateway | +—————————————+“`This diagram highlights the core components of the system and the flow of data.
Each component plays a crucial role in maintaining data integrity and security.
Key Performance Indicators (KPIs)
Several KPIs are crucial for evaluating the success of Lumenisity’s integration. These include:
- Data Transfer Rate: The speed at which data is transferred, measured in gigabits per second (Gbps), is a key metric. High transfer rates are essential for efficient data exchange.
- Encryption Efficiency: The speed and efficiency of the encryption process are essential for real-time data transfer. This is crucial in applications like live streaming and high-frequency trading.
- Security Incident Rate: A low rate of security incidents, such as data breaches or unauthorized access, demonstrates the effectiveness of the security measures implemented.
- Latency: The time taken for data to travel from the source to the destination. Lower latency is generally preferred, especially in applications requiring near real-time data transfer.
These KPIs provide a comprehensive view of the system’s performance and security posture, enabling informed decision-making regarding its integration.
Epilogue

The acquisition of Lumenisity by Microsoft represents a significant leap forward in secure data transfer. This integration will likely reshape the competitive landscape, potentially leading to new security standards and improved user experiences. While challenges may exist in the integration process, the potential benefits for data security and transfer reliability appear substantial. The future looks promising for enhanced data protection within Microsoft’s ecosystem.
Essential Questionnaire: Microsoft Acquires Lumenisity For Secure Data Transfer
What are the key motivations behind Microsoft’s acquisition of Lumenisity?
Microsoft likely sought to bolster its data security capabilities, enhance data transfer speed, and gain a competitive edge in the cloud security market. The acquisition could also provide access to Lumenisity’s proprietary technology and expertise.
What are some potential security threats or vulnerabilities this integration may introduce?
Any integration introduces potential vulnerabilities, and careful security analysis and mitigation strategies are critical. A thorough evaluation of Lumenisity’s systems, compared to Microsoft’s, should be performed to identify and address any compatibility or security concerns.
How will this acquisition impact customer data security?
The acquisition is expected to strengthen customer data security by integrating Lumenisity’s robust security protocols. This could translate to improved encryption, enhanced access controls, and potentially reduced risk of data breaches.
What are the expected changes in the competitive landscape of secure data transfer?
The acquisition could shift the competitive landscape, potentially leading to new security standards and innovation in the secure data transfer industry. Competitors may adapt to address these advancements, leading to a more secure and competitive market overall.