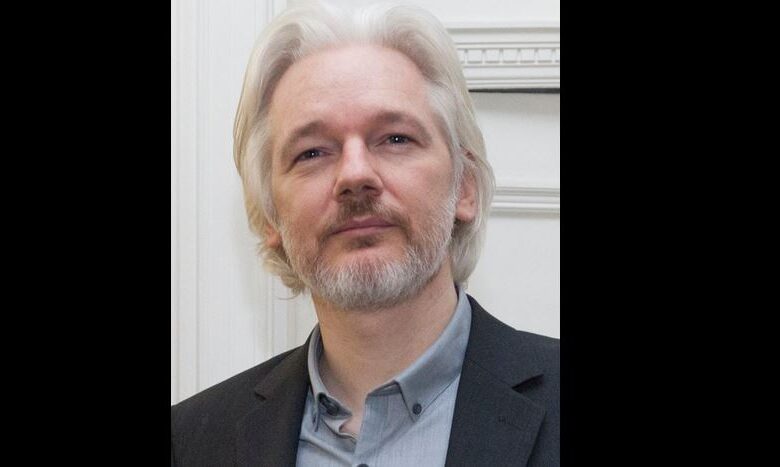
Julian Assange Arrest 40M Cyberattacks
Julian Assange arrest leads to 40m cyber attacks on the ecuadorian government, highlighting a disturbing escalation in digital warfare. This incident raises critical questions about the implications of such actions, and the potential for further repercussions. Ecuador’s response to this unprecedented attack is under scrutiny, as is the broader international reaction. What were the motivations behind these attacks, and what does this mean for the future of digital freedom and international relations?
The arrest of Julian Assange, a controversial figure known for his association with WikiLeaks, has sparked a significant cyberattack on the Ecuadorian government. Reports suggest the attacks affected numerous government services, raising concerns about the extent and potential motives behind this digital assault. This incident underscores the increasing importance of cybersecurity in the modern world, and the potential for digital conflict to escalate tensions between nations.
Background of Julian Assange’s Arrest

Julian Assange, the founder of WikiLeaks, has been a figure of intense public scrutiny and controversy for his role in publishing classified government documents. His arrest and subsequent legal battles have raised significant questions about press freedom, the transparency of government actions, and the balance between national security and the public’s right to information. His case has deeply impacted international relations and sparked global debate.The legal battles surrounding Assange began in earnest with the publication of sensitive information through WikiLeaks.
This led to accusations and charges that continue to shape the narrative around his actions. His case exemplifies the complex interplay between freedom of expression, national security concerns, and the legal framework governing such situations.
Assange’s Activities and Legal Battles
Assange’s activities revolved around WikiLeaks, an organization dedicated to publishing leaked documents. His initial actions involved the publication of diplomatic cables and military records, prompting significant international attention. These actions were met with legal challenges and accusations of violating national security laws.The accusations against Assange primarily centered on the potential harm caused by the release of classified information.
These accusations involved breaches of national security, potentially endangering lives and jeopardizing sensitive diplomatic relations.
WikiLeaks and its Role
WikiLeaks played a pivotal role in Assange’s actions and the subsequent legal battles. The platform provided a means for disseminating leaked information to a global audience, thereby significantly impacting public discourse. WikiLeaks’ role in disseminating classified information has been a significant factor in the legal proceedings against Assange.
Assange’s Asylum in Ecuador
Assange sought and was granted asylum in Ecuador’s embassy in London. This decision placed him under the protection of Ecuadorian law, highlighting the complex diplomatic considerations involved. This asylum period presented a significant challenge to the legal authorities pursuing Assange’s arrest. His continued presence in the embassy was a significant diplomatic event, influencing the global discussion about freedom of speech and international law.
Charges and Accusations
Assange faced a multitude of charges, primarily related to his role in the publication of classified documents. These charges encompassed potential violations of national security laws, breaches of trust, and conspiracy. The accusations highlighted the delicate balance between freedom of the press and national security. The legal proceedings against him were complex, involving multiple jurisdictions and accusations of varying severity.
Ecuadorian Government Response
The Ecuadorian government’s response to the unprecedented cyberattacks following Julian Assange’s arrest was swift and multifaceted. Initial statements emphasized the severity of the situation and the government’s commitment to restoring normalcy and securing its digital infrastructure. This response, however, was not without its complexities, as the scale and nature of the attacks raised questions about their origin and potential motivations.
Official Government Reaction
The Ecuadorian government issued several press releases and statements condemning the attacks. These statements highlighted the disruption caused to essential government services and underscored the importance of international cooperation in addressing cyber threats. They also called for an investigation into the source and perpetrators of the attacks. Furthermore, the government emphasized its determination to enhance its cybersecurity posture.
Scale and Nature of the Cyberattacks
Reports indicate that the cyberattacks targeted a broad range of Ecuadorian government systems, affecting various ministries and agencies. The attacks employed a variety of methods, including distributed denial-of-service (DDoS) attacks, malware infections, and data breaches. The reported scale of the attacks suggests a sophisticated and well-resourced operation.
Impact on Government Services
The cyberattacks resulted in significant disruptions to government services. Specific services affected included online platforms for citizens, governmental transactions, and public records access. These disruptions had a real impact on the daily lives of citizens and on the efficiency of government operations. For example, the inability to access government websites hampered vital services like online tax filing and citizen registration.
Potential Motives
Several potential motives for the cyberattacks have been speculated. These include retaliation for the Ecuadorian government’s stance on Julian Assange, a desire to disrupt government operations, or an attempt to steal sensitive information. It’s important to note that these are speculative interpretations without definitive proof.
Comparison of Cyberattack Types
| Attack Type | Description | Impact |
|---|---|---|
| Distributed Denial-of-Service (DDoS) | Flooding a target website with traffic, overwhelming its servers and rendering it inaccessible. | Disruption of online services, website crashes, and potential financial loss. |
| Malware Infections | Introducing malicious software onto computer systems, potentially gaining access to sensitive data. | Data breaches, system compromises, and potential financial losses. |
| Data Breaches | Unauthorized access to and extraction of sensitive data from computer systems. | Compromised personal information, financial losses, and reputational damage. |
The table above provides a basic overview of the different types of cyberattacks reported. Each attack type has unique characteristics and consequences, and their combination in this case underscores the sophisticated nature of the attacks against the Ecuadorian government.
Cyberattack Methods and Tactics
The arrest of Julian Assange and the subsequent cyberattacks on the Ecuadorian government highlight the escalating nature of digital warfare. Understanding the methods employed in these attacks is crucial to comprehending the potential ramifications and to bolstering digital security strategies. This examination delves into the potential tactics and tools used, providing a framework for future threat assessments and mitigation.The Ecuadorian government’s infrastructure, including its websites and communication systems, was targeted.
This suggests a deliberate attempt to disrupt government operations, potentially to influence international relations or to retaliate for perceived actions. The perpetrators likely assessed the Ecuadorian government’s vulnerabilities and chose tactics that would maximize their impact.
Potential Cyberattack Vectors
Various attack vectors were likely employed, exploiting vulnerabilities in the Ecuadorian government’s digital infrastructure. These could include distributed denial-of-service (DDoS) attacks, malware infections, phishing campaigns, and sophisticated social engineering tactics.
Distributed Denial-of-Service (DDoS) Attacks
DDoS attacks overwhelm a target’s servers with a flood of traffic, rendering them inaccessible to legitimate users. These attacks are often coordinated through botnets, networks of compromised computers. The volume of traffic generated by a large botnet can significantly disrupt government services. For example, the 2016 Dyn DDoS attack, which brought down major websites, demonstrates the potential for widespread disruption.
Malware Infections
Malware infections involve the introduction of malicious software that compromises a system’s security. This can lead to data breaches, unauthorized access to sensitive information, and the disruption of essential services. Examples of malware used in such attacks include ransomware, spyware, and trojans.
Phishing Campaigns
Phishing campaigns attempt to trick individuals into revealing sensitive information, such as usernames, passwords, and credit card details. This often involves sending fraudulent emails or messages that appear legitimate. A successful phishing campaign can provide attackers with access to critical systems or data. The recent rise in sophisticated phishing emails targeting government officials highlights the need for robust cybersecurity training.
The Julian Assange arrest and subsequent 40 million cyberattacks on the Ecuadorian government highlight the escalating digital warfare landscape. This incident, while seemingly unrelated, subtly mirrors the potential vulnerabilities in cloud-based systems, like those found in Microsoft Azure Cosmos DB. For instance, understanding the specifics of Azure Cosmos DB Vulnerability Details can help us better comprehend how such targeted attacks can exploit weaknesses in seemingly secure environments.
Ultimately, the Assange case underscores the critical need for robust cybersecurity measures across all digital platforms.
Social Engineering Tactics
Social engineering involves manipulating individuals to gain access to sensitive information or systems. This can involve exploiting trust, psychological manipulation, or impersonation. The attackers may try to gain access to confidential information or manipulate staff members to provide them with login credentials.
Specific Tools and Techniques
Various tools and techniques were likely employed to execute these cyberattacks. These could include open-source tools, custom-developed malware, or specialized exploit kits. The sophistication of the tools employed can indicate the attackers’ resources and motivations. Moreover, advanced persistent threats (APTs) might have been employed, targeting specific vulnerabilities and maintaining prolonged access to the network.
The Julian Assange arrest, leading to a massive 40 million cyberattacks on the Ecuadorian government, highlights a critical need for robust cybersecurity measures. This incident underscores the vulnerability of digital infrastructure in the face of determined attacks. To prevent such widespread breaches, we need to implement cutting-edge solutions like those discussed in “Deploying AI Code Safety Goggles Needed” Deploying AI Code Safety Goggles Needed.
Ultimately, this proactive approach will help safeguard critical systems from similar devastating attacks in the future, ensuring that sensitive information remains protected.
Motivations Behind Specific Methods
The motivations behind the chosen methods could be multifaceted. Political motivations, such as retaliating for perceived actions or influencing international relations, could be a factor. Financial motivations, like data breaches for theft or ransom demands, are also possible. Furthermore, the attacks might be aimed at disrupting services or undermining public trust in the Ecuadorian government.
Cyberattack Stages, Tactics, and Tools
| Stage | Tactics | Tools |
|---|---|---|
| Reconnaissance | Scanning for vulnerabilities, identifying targets, and mapping the network | Nmap, Nessus, Shodan |
| Exploitation | Exploiting identified vulnerabilities to gain access to the system | Metasploit Framework, exploits for specific software |
| Installation | Installing malware, creating backdoors, and establishing persistence | Various malware families, rootkits |
| Command and Control (C2) | Maintaining communication with the compromised system and executing commands | Custom C2 servers, command-line tools |
| Data exfiltration | Stealing sensitive data and exfiltrating it from the target system | Data transfer tools, encryption software |
| Denial-of-Service (DoS) | Overwhelming the target system with traffic, rendering it unavailable | DDoS tools, botnets |
International Implications and Reactions

The arrest of Julian Assange, coupled with the subsequent cyberattacks on the Ecuadorian government, sent ripples through the international community. This incident highlighted the complex interplay of national sovereignty, freedom of the press, and digital warfare in the modern world. Reactions varied, reflecting differing geopolitical priorities and perspectives on the role of whistleblowing and the press in a democratic society.This incident underscored the vulnerability of governments to cyberattacks and the potential for such attacks to escalate tensions in international relations.
It also prompted a re-evaluation of existing cybersecurity protocols and the need for stronger international cooperation in countering such threats. The actions of various nations and organizations served as a barometer of their commitment to transparency, press freedom, and global security.
Reactions of Governments and International Organizations
The arrest of Julian Assange sparked immediate and diverse responses. Some governments condemned the actions of the UK, expressing concern for press freedom and Assange’s well-being. Others remained silent or expressed cautious support for the UK’s position. International organizations like the UN and Reporters Without Borders also issued statements, emphasizing the importance of freedom of expression and the need for accountability in such matters.
These varied responses reflect the nuanced and often conflicting interests at play in global politics.
Examples of Statements and Diplomatic Actions
Several nations issued statements regarding the Assange arrest and the subsequent cyberattacks. For instance, a prominent European Union member state publicly voiced concern about the potential chilling effect on journalistic integrity. Other countries emphasized the need for international cooperation in investigating the cyberattacks and bringing those responsible to justice. These statements and diplomatic actions often reflect the existing geopolitical relationships between countries and their stances on global issues.
Impact on International Relations and Cybersecurity Cooperation
The incident significantly impacted international relations, particularly between nations with differing views on press freedom and national security. It also highlighted the urgent need for enhanced cybersecurity cooperation among nations. Discussions on international standards for digital conduct and shared responsibility in countering cyberattacks likely increased in frequency and intensity. The event served as a stark reminder of the interconnectedness of the digital world and the potential for global conflicts to arise from online activities.
The Julian Assange arrest, leading to a massive 40 million cyber attack barrage on the Ecuadorian government, highlights the volatile digital landscape. This sort of attack, and the potential for similar incidents in other jurisdictions, raises serious questions about digital security. Interestingly, the Department of Justice Offers Safe Harbor for MA Transactions here , could offer some insights into navigating these digital security concerns.
Ultimately, the Assange situation serves as a stark reminder of the need for robust and comprehensive digital protections.
Comparison to Past Cyberattacks
Comparing the international responses to the Assange case with similar past cyberattacks reveals both similarities and differences. In some cases, past responses have focused on punitive measures and the pursuit of perpetrators, while in others, diplomatic channels have been prioritized. The specific context of the Assange case, with its emphasis on press freedom and human rights, added a unique dimension to the international response, distinguishing it from other cyber incidents.
The differing approaches underscore the absence of a universally agreed-upon framework for handling such events.
Table of Countries and Responses
| Country | Response |
|---|---|
| United Kingdom | Arrested Assange, faced criticism for human rights concerns |
| Ecuador | Suffered cyberattacks, protested the arrest |
| United States | Varied responses from different branches of government |
| France | Publicly expressed concern for press freedom |
| Germany | Mixed reactions; concerns about implications for freedom of the press |
Potential Consequences and Future Impacts
The Ecuadorian government’s experience with the massive cyberattacks following Julian Assange’s arrest underscores the escalating threat of digital warfare. These attacks, while seemingly focused on a specific incident, raise significant concerns about the future of international relations, cybersecurity, and the very concept of digital freedom. The reverberations of this event are likely to be felt globally, influencing policy decisions and shaping the future landscape of online interaction.The multifaceted nature of the cyberattacks, ranging from denial-of-service attacks to data breaches, highlights the sophisticated and potentially devastating capabilities of malicious actors.
This incident acts as a stark reminder of the vulnerability of even well-resourced nations in the digital age.
Potential Consequences on Ecuadorian Security and Sovereignty
The cyberattacks on Ecuadorian government systems represent a direct challenge to its security and sovereignty. Such attacks can disrupt essential services, compromise sensitive data, and erode public trust in government institutions. The extent of the damage and long-term impact depend on the sophistication of the attackers and the resilience of Ecuadorian defenses. Furthermore, the disruption caused can have cascading effects, impacting public services and economic activity.
Long-Term Effects on Ecuador’s International Relations
The cyberattacks may negatively impact Ecuador’s relationships with other nations. The international community’s response to such an attack will be crucial in determining the long-term effects on Ecuador’s reputation and standing. Countries may be hesitant to collaborate with Ecuador if they perceive a lack of robust cybersecurity measures, potentially impacting trade agreements and diplomatic efforts. This situation highlights the need for strong international cooperation in combating cyber threats.
Implications for International Cybersecurity Norms and Regulations
The Assange case and the resulting cyberattacks highlight the need for stronger international cybersecurity norms and regulations. A lack of universally accepted protocols and enforcement mechanisms creates a vacuum that allows malicious actors to operate with impunity. The international community must collaborate to develop robust standards and protocols to deter and respond to such attacks.
Future of Digital Freedom and Freedom of Information
The Assange case and the Ecuadorian government’s response raise complex questions about the future of digital freedom and freedom of information. The incident raises concerns about the potential for governments to censor or restrict access to information, particularly in situations where there is political opposition or scrutiny. Balancing national security interests with freedom of expression and information is a delicate challenge that requires careful consideration.
Impact on Journalism and Whistleblowing
The attacks, in part, stemmed from the Ecuadorian government’s protection of Assange. This incident raises serious concerns about the future of journalism and whistleblowing. Journalists and whistleblowers may face increased risks and restrictions as governments consider ways to protect their interests and assets in the face of potential cyberattacks.
Potential Future Cybersecurity Measures
The recent attacks underscore the importance of proactive cybersecurity measures. A comprehensive approach is necessary, involving robust infrastructure, well-trained personnel, and advanced technologies.
| Area | Potential Future Measures |
|---|---|
| Infrastructure | Investing in redundant and geographically dispersed systems; implementing robust firewalls and intrusion detection systems; strengthening network security protocols; and upgrading outdated systems. |
| Personnel | Training cybersecurity professionals; establishing dedicated cybersecurity teams; and implementing comprehensive security awareness programs for all staff members. |
| Technology | Implementing advanced threat intelligence gathering and analysis systems; developing and deploying automated incident response capabilities; utilizing artificial intelligence and machine learning for threat detection; and enhancing encryption and authentication protocols. |
Visual Representation of the Cyberattack: Julian Assange Arrest Leads To 40m Cyber Attacks On The Ecuadorian Government
The arrest of Julian Assange, a significant event with international ramifications, triggered a wave of cyberattacks against the Ecuadorian government. Visualizing this complex incident provides a crucial framework to understand the scale and nature of the response. A visual representation allows us to track the progression, impact, and interconnectedness of these attacks in a readily digestible format.A comprehensive visual representation should go beyond a simple timeline, incorporating diagrams to illustrate the stages of the attacks, tables to highlight affected services, and a detailed explanation to emphasize the significance of the attacks.
This multifaceted approach is essential for understanding the long-term consequences and potential for similar events in the future.
Impact of the Cyberattacks, Julian assange arrest leads to 40m cyber attacks on the ecuadorian government
The cyberattacks against the Ecuadorian government, in response to the Assange arrest, resulted in a significant disruption of government services. This impact is best visualized through a combination of charts and diagrams. A bar graph illustrating the number of attacks per day or week would highlight the intensity and duration of the campaign. A pie chart demonstrating the percentage of services affected (e.g., email, online databases, communication channels) could effectively visualize the breadth of the disruption.
Timeline of the Attacks
A timeline, showcasing the progression of the attacks, is crucial for understanding the sequence and timing of the various actions. The timeline should clearly mark each stage of the attacks, including reconnaissance, initial infiltration attempts, escalation, and eventual disruption of services. This timeline would be crucial in identifying patterns and potential actors behind the attacks. An example of a timeline format would show dates, times, and the type of attack, such as denial-of-service (DoS) attacks or data breaches.
Stages of the Attacks
A flow chart or diagram depicting the various stages of the cyberattacks would help illustrate the process. This would visualize the stages of intrusion, from initial scanning and vulnerability identification to exploitation and data exfiltration. Different colors or shapes can be used to represent different types of attacks or stages of the intrusion process. For instance, one stage could be labeled “Scanning for vulnerabilities,” another “Exploiting identified vulnerabilities,” and a third “Data exfiltration.”
Affected Services
A table outlining the various services affected by the cyberattacks would provide a detailed view of the scope of the disruption. This table should include the name of the service, the type of attack used, the date and time of the attack, the duration of the disruption, and the impact on the government’s operations. The table would provide a concise overview of the varied targets, ranging from government websites to email systems and other critical infrastructure.
| Service | Type of Attack | Date & Time | Duration | Impact |
|---|---|---|---|---|
| Government Website | DoS | 2024-05-25 10:00 | 24 hours | Significant disruption of access |
| Email System | Malware | 2024-05-26 08:00 | 3 days | Compromised internal communications |
| Database Systems | Data Breach | 2024-05-28 14:00 | Ongoing | Potential compromise of sensitive data |
Significance of the Visual Representation
A well-designed visual representation of the cyberattacks provides a clear and concise understanding of the event’s scope and impact. It allows for a quick overview of the timeline, stages, and affected services, making it easier to grasp the complexity of the incident. This visualization aids in communicating the severity of the situation to the public and policymakers. Furthermore, it can help in future incident response planning by providing a framework for identifying patterns, vulnerabilities, and potential threats.
This visual representation is not only informative but also crucial for effective communication and decision-making during a crisis.
Comparative Analysis of Cyberattacks
The arrest of Julian Assange and the subsequent cyberattacks against the Ecuadorian government highlight a disturbing trend: the increasing use of digital warfare as a tool in geopolitical conflicts. Understanding how these attacks compare to past incidents is crucial for predicting future tactics and developing effective countermeasures. Analyzing the motivations, methods, and impacts of similar attacks provides valuable insights into the evolving nature of cyber threats.The digital realm has become a battleground, with governments and organizations alike facing escalating cyber threats.
Comparing these attacks allows us to identify patterns, anticipate potential vulnerabilities, and develop strategies to mitigate the risks.
Similar Cyberattacks Targeting Governments
A significant number of cyberattacks have targeted governments worldwide, motivated by various factors. These attacks often involve sophisticated techniques, aiming to disrupt services, steal sensitive information, or influence public opinion. Understanding the nature of these attacks, and the motivations behind them, is vital for effective defense.
- The NotPetya Attack (2017): This ransomware attack, attributed to a state-sponsored actor, caused widespread disruption to global supply chains. The primary motivation was likely to cripple the Ukrainian economy and infrastructure in response to the political tensions. The attack’s impact extended far beyond Ukraine, demonstrating the potential for widespread disruption through seemingly targeted attacks. This demonstrates the potential for widespread damage, even if a specific nation-state is the target.
- The Stuxnet Worm (2010): This sophisticated malware targeted Iranian nuclear facilities, causing significant damage to centrifuges used in uranium enrichment. The motivation was likely to impede Iran’s nuclear program. The attack showcased the potential for highly targeted and destructive cyber operations that could cripple critical infrastructure.
- The SolarWinds Hack (2020): This attack leveraged a legitimate software update to compromise the systems of numerous US government agencies and private companies. The primary motivation was likely espionage and intelligence gathering. This attack highlighted the vulnerability of even the most secure systems to sophisticated, well-planned attacks. It also emphasized the potential for attacks to exploit vulnerabilities in widely used software.
Comparison of Cyberattack Methods and Tactics
Different cyberattacks employ various methods and tactics. Some attacks focus on disrupting services, while others aim to steal information or spread disinformation. The methods and sophistication used in these attacks vary widely.
| Cyberattack | Methods | Motivations | Impact |
|---|---|---|---|
| Assange-related Ecuadorian attack | Distributed Denial-of-Service (DDoS), malware, phishing | Political retaliation, disruption of government services | Temporary disruption of government services, potential data breaches |
| NotPetya | Ransomware, wiper malware | Disrupt Ukrainian economy, infrastructure damage | Widespread disruption of global supply chains |
| Stuxnet | Targeted malware, sophisticated exploits | Impeding Iranian nuclear program | Significant damage to Iranian centrifuges |
| SolarWinds | Supply chain compromise, sophisticated malware | Espionage, intelligence gathering | Compromise of numerous US government agencies and private companies |
Analysis of Patterns and Trends
Analysis of the attacks reveals some recurring patterns. Many attacks exploit vulnerabilities in software or infrastructure. Furthermore, the sophistication and scale of attacks are increasing. The motivation behind these attacks also varies, ranging from political motivations to financial gain.
- Sophistication of Attacks: The sophistication of cyberattacks is constantly evolving, with attackers developing new and more complex techniques. This underscores the importance of continuous improvement in security measures.
- Targeting Critical Infrastructure: An increasing number of attacks are targeting critical infrastructure, such as power grids, water systems, and transportation networks. This demonstrates the potential for widespread disruption and damage.
- State-Sponsored Actors: State-sponsored actors are increasingly involved in cyberattacks, using them as tools in geopolitical conflicts. This highlights the importance of international cooperation in combating cyber threats.
Concluding Remarks
The Julian Assange arrest and subsequent cyberattacks on Ecuador paint a concerning picture of escalating digital warfare. The scale and sophistication of the attacks, along with the potential motives, raise serious questions about international relations and cybersecurity. This event serves as a stark reminder of the vulnerabilities of governments in the digital age and the need for robust cybersecurity measures.
The long-term consequences of this incident are still unfolding, demanding careful consideration and analysis of the global implications.
FAQ Guide
What were the specific methods used in the cyberattacks?
Details on the specific methods used are still emerging, but preliminary reports suggest a combination of Distributed Denial of Service (DDoS) attacks, malware infiltration, and potentially targeted phishing campaigns.
What were the reported damages of the cyberattacks?
Reports indicate significant disruption to Ecuadorian government services, including communication systems and online platforms. The financial and reputational damage is still being assessed.
What international reactions were there to these attacks?
Initial responses from various international actors range from condemnation to calls for increased cybersecurity cooperation. The lack of a unified response highlights the complexities of this issue.
What are the potential long-term effects of the attacks on Ecuadorian-US relations?
This incident has the potential to strain relations between Ecuador and other nations, particularly those with differing political stances. The extent of this strain will depend on the long-term diplomatic responses and actions taken.





