Irans Cyber Threat to North America
Iran to launch cyber attacks on North America, raising serious concerns about potential targets and motivations. This escalating cyber threat demands careful consideration of the methods, potential impacts, and crucial defensive strategies needed to protect North American interests.
The potential motivations behind such a move range from political retribution to economic disruption. Iran’s history of cyber activities, including past attacks, suggests a pattern of calculated actions. This analysis explores the potential scenarios, examining vulnerabilities in North American systems and the likely responses from governments and organizations. Understanding the potential targets, such as critical infrastructure and financial institutions, is vital for assessing the risks.
Potential Motivations for Cyberattacks: Iran To Launch Cyber Attacks On North America
Iran’s potential motivations for launching cyberattacks against North America are multifaceted and deeply rooted in a complex interplay of political, economic, and social factors. These motivations are often intertwined and may not be mutually exclusive, driving a range of actions from retaliatory measures to strategic advancements. Understanding these motivations is crucial for assessing the potential risks and developing appropriate countermeasures.
Potential Political Motivations
Iran’s pursuit of regional influence and its desire to challenge perceived US dominance in the Middle East are key drivers for cyberattacks. Aimed at disrupting critical infrastructure, financial institutions, or media outlets, such actions can be seen as a demonstration of power and a way to retaliate against perceived American interference in Iranian affairs. For example, past actions by Iranian actors or those suspected of being linked to Iran, such as the 2012 attack on the Iranian nuclear facilities, highlight the potential for disrupting essential services and critical infrastructure.
Potential Economic Motivations
Economic grievances, such as sanctions and trade disputes, could also incentivize cyberattacks. Disrupting the economic stability of North American entities could be seen as a way to retaliate against economic restrictions imposed on Iran. This includes targeting financial institutions to inflict financial losses and undermine the economic power of the United States.
Potential Social Motivations
Social and ideological motivations, though less readily quantifiable, can also play a role. A desire to promote a particular ideology or express opposition to US policies might drive actions intended to influence public opinion or undermine political systems. While this is a more nuanced factor, the potential for cyberattacks motivated by social or ideological objectives should not be discounted.
Comparison with Other Motivations
Other potential motivations for cyberattacks, such as those originating from state-sponsored actors or criminal organizations, often share some commonalities with Iranian motivations. However, the specific political and ideological contexts of each actor will influence the nature and scope of the cyberattacks. For instance, state-sponsored actors might focus on espionage or intelligence gathering, while criminal organizations prioritize financial gain.
Iranian motivations, in contrast, are frequently intertwined with political and ideological aims.
Potential Targets and Risks
Cyberattacks against North America could target a wide range of entities, from critical infrastructure to financial institutions and media outlets. The potential impact of these attacks can be severe, leading to disruptions in essential services, economic losses, and social unrest.
Worried about Iran potentially launching cyberattacks on North America? While that’s a serious concern, it’s also important to keep an eye on other important legal developments, like the Department of Justice’s recent Safe Harbor policy for MA transactions. Department of Justice Offers Safe Harbor for MA Transactions could have implications for businesses and individuals in the region, which, in turn, could potentially bolster defenses against future cyber threats.
This all raises the question of how prepared North America is for the potential Iranian cyberattacks.
| Motivation | Potential Target | Risk Assessment | Impact |
|---|---|---|---|
| Political Retaliation | Critical Infrastructure (power grids, water systems) | High | Widespread disruption of essential services, potential for loss of life |
| Economic Retaliation | Financial Institutions | High | Significant financial losses, market instability |
| Ideological Opposition | Media Outlets | Moderate | Disinformation campaigns, erosion of public trust |
| Espionage | Government Agencies | Moderate to High | Compromised national security, potential for intelligence leaks |
Examples of Past Cyberattacks
Numerous cyberattacks have been attributed to or suspected of being linked to Iran, targeting various entities and reflecting the diverse range of motivations discussed above. Examples include attacks on US government websites and infrastructure, as well as those targeting financial institutions and energy companies. These incidents underscore the potential for significant harm and the need for robust cybersecurity measures.
Long-Term Impacts, Iran to launch cyber attacks on north america
The potential long-term impacts of such actions on the international political landscape are significant. Escalation of cyber conflicts could lead to a further deterioration of relations between nations, potentially escalating into more traditional forms of conflict. This makes proactive measures and de-escalation strategies crucial.
Methods and Capabilities

Iran’s cyber capabilities, while not on par with nation-states like the US or Russia, have demonstrated a growing sophistication and a willingness to leverage cyberattacks for political and strategic objectives. This capability, coupled with the potential motivations already discussed, makes understanding their methods and potential targets crucial. A deep dive into their tactics, techniques, and procedures (TTPs) reveals a range of potential methods, from relatively simple distributed denial-of-service (DDoS) attacks to more advanced and targeted exploits.
Potential Attack Methods
Iran possesses a diverse toolkit of cyberattack methods, ranging from exploiting vulnerabilities in software and hardware to leveraging social engineering tactics. These methods are often employed in conjunction, creating a layered approach to achieve maximum impact. The effectiveness of these attacks is highly dependent on the specific target and the level of preparedness of the victim.
- Exploiting Software Vulnerabilities: Iran’s cyber actors are known to exploit publicly disclosed and zero-day vulnerabilities in software to gain unauthorized access to systems. They often target critical infrastructure components, aiming to disrupt services or steal sensitive data. Examples include the Stuxnet worm, which demonstrated the ability to target industrial control systems. Iranian actors might adapt these methods to target North American systems, aiming to disable power grids or water treatment plants.
- Phishing and Social Engineering: This method relies on tricking individuals into revealing sensitive information, such as usernames and passwords. These attacks often target employees with seemingly legitimate emails or messages, aiming to gain initial access to a network. A successful phishing campaign could lead to widespread data breaches and the compromise of sensitive systems.
- Distributed Denial-of-Service (DDoS) Attacks: These attacks flood a target system with traffic, overwhelming its resources and rendering it unavailable to legitimate users. DDoS attacks are often used as a preliminary step to distract security teams and pave the way for more sophisticated attacks. The scale of such attacks can vary, from small-scale disruptions to massive outages, disrupting critical services.
- Advanced Persistent Threats (APTs): These attacks involve a long-term campaign to infiltrate a target network, often to steal sensitive data or disrupt operations. Iran’s APT groups are known to employ sophisticated malware and exploit zero-day vulnerabilities to maintain persistent access. This allows for ongoing monitoring and manipulation of systems.
Cyberweapons and Tactics
The cyberweapons employed by Iran are likely a combination of open-source tools, custom-developed malware, and potentially acquired or stolen technologies. The tactics used will vary depending on the target and objectives.
- Malware: Iranian actors have developed and used various types of malware, including ransomware, spyware, and Trojans. These are designed to achieve different goals, from data exfiltration to system disruption.
- Exploit Kits: Pre-packaged tools used to exploit vulnerabilities in software. These are frequently updated and improved, and Iranian actors may use readily available exploit kits, adapting them for their own use.
- Zero-Day Exploits: These exploits target vulnerabilities unknown to the software vendor, providing a high degree of stealth and effectiveness. Iran might obtain or develop these exploits to gain unauthorized access to critical systems.
Comparative Analysis of Capabilities
Iran’s cyber capabilities are considered mid-tier compared to advanced nations like the United States and Russia. While they have shown progress in certain areas, they still face challenges in terms of sustained operations and the development of truly innovative attack methods. Their cyber capabilities are primarily focused on disruptive and espionage activities, rather than large-scale infrastructure attacks.
Potential Vulnerabilities in North American Systems
North American systems, like those in many developed nations, often share common vulnerabilities. These vulnerabilities may stem from outdated software, inadequate security protocols, and a lack of staff training.
- Outdated Software: Failure to patch known vulnerabilities in outdated software leaves systems susceptible to exploitation. This is a prevalent issue across various sectors, from critical infrastructure to financial institutions.
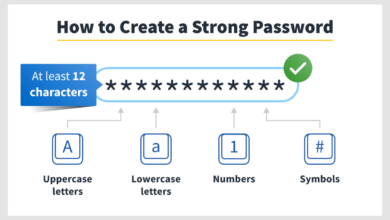
- Weak Passwords: Simple or easily guessed passwords are a significant vulnerability for many systems. This allows attackers to gain access using readily available tools.
- Insufficient Security Protocols: Lack of robust security protocols and procedures, such as multi-factor authentication, can leave systems vulnerable to unauthorized access.
- Lack of Staff Training: Employees who lack adequate security training are more likely to fall victim to social engineering attacks.
Cyberattack Methods, Impacts, and Effectiveness
The table below presents a potential overview of different cyberattack methods, their potential targets, and their estimated effectiveness and impact.
| Method | Target | Impact | Effectiveness |
|---|---|---|---|
| DDoS Attack | Government Websites | Disruption of services, loss of public trust | Medium |
| Malware Infection | Financial Institutions | Data breaches, financial losses | High |
| Supply Chain Attack | Critical Infrastructure | System disruption, potential physical damage | High |
Technical Aspects of Attacks
The technical aspects of these attacks will likely involve exploiting known and unknown vulnerabilities, developing custom malware, and employing advanced techniques for network reconnaissance and persistence. Advanced Persistent Threats (APTs) will likely be the most complex and sophisticated attacks. The use of botnets to amplify attacks is also a potential tactic.
Potential Impacts and Consequences
Iranian cyberattacks, if launched against North American critical infrastructure, could have devastating consequences, impacting everything from energy grids to financial systems. The potential for widespread disruption and economic damage is significant, requiring a proactive and well-coordinated response from both governments and private sector organizations. Such attacks could also exacerbate existing social and political tensions, potentially leading to a wider conflict.
Consequences on Critical Infrastructure
North American critical infrastructure, including power grids, water systems, and transportation networks, is highly interconnected and vulnerable to cyberattacks. A successful attack could lead to widespread power outages, water shortages, and disruptions in transportation. The cascading effects of such disruptions could have far-reaching consequences, affecting essential services and causing significant economic damage. The 2015 cyberattack on the Ukrainian power grid, for example, demonstrated the potential for significant disruption and the ripple effects of such an incident.
Economic Ramifications
The economic impact of a successful cyberattack could be substantial. Financial losses could result from damage to critical infrastructure, disruption of services, and reputational damage. Businesses relying on these systems could face substantial losses, leading to job losses and a decline in economic activity. Furthermore, the disruption of essential services could cause a significant decline in productivity across various sectors, impacting GDP growth.
For instance, a prolonged outage of a major power grid could result in billions of dollars in lost productivity and repair costs.
Social and Political Implications
Cyberattacks can have profound social and political implications. Public trust in critical infrastructure and government institutions could be eroded, leading to social unrest. Disruptions to essential services could exacerbate existing social inequalities, particularly for vulnerable populations. The perception of a state-sponsored cyberattack could also strain international relations and escalate existing geopolitical tensions. Historical examples, such as the Stuxnet worm attack, highlight the potential for such attacks to create a lasting impact on national security and international relations.
Government and Organizational Responses
North American governments and organizations must be prepared for potential cyberattacks and develop robust response plans. This includes strengthening cybersecurity defenses, investing in incident response capabilities, and fostering collaboration between government agencies and the private sector. Developing early warning systems and robust communication protocols are essential to mitigate the impact of any cyberattack.
Potential Impacts on Various Sectors
| Sector | Impact | Mitigation Strategies |
|---|---|---|
| Energy | Widespread power outages, disruption of energy supply chains, economic losses due to production halt. | Strengthening grid security, implementing advanced threat detection systems, developing emergency response plans. |
| Finance | Disruption of financial transactions, data breaches, financial losses, reputational damage. | Implementing robust cybersecurity protocols, encrypting sensitive data, establishing secure transaction systems. |
| Healthcare | Disruption of patient care, data breaches, compromise of medical records. | Implementing robust cybersecurity measures for electronic health records, ensuring data encryption, training staff on cybersecurity best practices. |
| Transportation | Disruption of transportation networks, delays, potential safety hazards. | Securing critical transportation systems, implementing cybersecurity protocols for automated systems, establishing emergency response plans. |
Escalation of Conflicts and International Relations
A cyberattack, particularly if attributed to a state actor, could significantly escalate geopolitical tensions and strain international relations. The potential for miscalculation and retaliatory actions is high. The use of cyberattacks as a means of coercion or conflict escalation is a growing concern in the international arena. The ambiguity surrounding attribution and responsibility can further complicate the situation and potentially lead to unintended consequences.
Defense Strategies and Countermeasures

Iran’s potential for cyberattacks on North America necessitates robust defensive strategies. Proactive measures and international cooperation are crucial to mitigate the risk and ensure the resilience of critical infrastructure. A layered approach, encompassing technical, procedural, and human elements, is vital to effectively deter and respond to such threats.Understanding the motivations, methods, and capabilities of potential attackers, coupled with comprehensive defensive strategies, forms the cornerstone of a proactive cybersecurity posture.
This requires a multifaceted approach that combines advanced technologies with well-defined protocols and trained personnel.
Potential Defensive Strategies
Proactive measures are essential to mitigate the risk of cyberattacks. These include implementing strong security protocols, conducting regular security assessments, and developing incident response plans. The goal is to anticipate and address potential vulnerabilities before they are exploited. The success of these strategies hinges on the commitment of organizations and governments to invest in robust cybersecurity measures.
News about Iran potentially launching cyberattacks on North America is concerning. This underscores the urgent need for robust cybersecurity measures, especially given the evolving threat landscape. We need to be proactive in bolstering our defenses, and that includes deploying AI Code Safety Goggles Needed Deploying AI Code Safety Goggles Needed to help prevent vulnerabilities in critical infrastructure.
Ultimately, staying ahead of these potential attacks requires a multi-faceted approach.
Specific Countermeasures and Preventative Measures
Implementing strong access controls and multi-factor authentication can significantly reduce the risk of unauthorized access. Regular software updates and patching are essential to address known vulnerabilities. Implementing intrusion detection and prevention systems (IDS/IPS) helps identify and block malicious activity. Regular security awareness training for personnel is critical in preventing social engineering attacks. These preventative measures form the foundation of a strong defensive posture.
Comparison of Defensive Strategies
Different defensive strategies have varying strengths and weaknesses. A layered approach, combining multiple strategies, often yields the most effective results. For example, strong network segmentation can limit the impact of a successful attack. Firewalls provide a crucial first line of defense. Implementing a robust incident response plan allows for a swift and coordinated response to any detected threat.
Regular penetration testing helps identify vulnerabilities before they are exploited.
Measures to Enhance the Security of Critical Infrastructure
Critical infrastructure, such as power grids and financial systems, is a primary target for cyberattacks. Implementing advanced threat detection and response systems is crucial. Robust data encryption and secure communication protocols are vital. Establishing clear communication channels and protocols for incident response teams is essential. Regular security audits and vulnerability assessments of critical infrastructure systems are necessary to identify and address potential weaknesses.
Table of Defensive Strategies
| Strategy | Strengths | Weaknesses | Applicability |
|---|---|---|---|
| Network Segmentation | Limits the impact of a successful attack, isolating compromised systems. | Requires careful planning and can be complex to implement in large networks. | Wide range of organizations, especially those with interconnected systems. |
| Intrusion Detection/Prevention Systems (IDS/IPS) | Identify and block malicious activity in real-time. | Can generate false positives, requiring careful configuration and monitoring. | Essential for organizations with high-value data or critical infrastructure. |
| Security Awareness Training | Reduces the risk of social engineering attacks. | Requires ongoing effort and commitment from personnel. | Applicable to all organizations, as human error is a significant vulnerability. |
| Regular Security Assessments | Identify vulnerabilities before they are exploited. | May not detect all vulnerabilities, and requires ongoing effort. | Critical for organizations with high-value data or critical infrastructure. |
Role of International Cooperation
International cooperation is vital in countering cyber threats. Sharing information and best practices among nations can significantly enhance the collective response to cyberattacks. Joint exercises and training programs can help build collective capabilities. Standardizing security protocols and regulations across borders is essential for greater effectiveness. Harmonizing legal frameworks for international cybercrime can strengthen collaborative efforts in the fight against cyber threats.
Illustrative Case Studies
Iran’s alleged involvement in cyberattacks has raised significant concerns about the potential for future malicious activity. Analyzing past incidents provides valuable insights into the tactics, techniques, and procedures (TTPs) employed, allowing for a more informed understanding of the potential threats posed by future attacks. This analysis explores past attacks attributed to or suspected of being linked to Iran, examining their methods, outcomes, and impact, to better assess the evolving cyber landscape.Past cyberattacks, even those not directly attributable to Iran, can still offer valuable lessons.
Studying the methods and motivations of past attacks allows for the development of more robust defenses and countermeasures. Understanding the potential consequences of these attacks helps anticipate future threats and tailor responses accordingly. Analyzing the impact on previous targets highlights the importance of proactive security measures.
Past Cyberattacks Linked to or Suspected of Originating from Iran
The attribution of cyberattacks to specific nation-states is often complex and reliant on circumstantial evidence. Determining the precise origin of an attack requires careful examination of technical indicators and forensic analysis. Several instances raise concerns about Iranian involvement, although definitive proof may be elusive. The motivations behind these attacks often remain ambiguous, though political and economic motivations are frequently cited.
Recent news about Iran potentially launching cyberattacks on North America has got me thinking about vulnerabilities in cloud systems. For example, a critical security flaw in Microsoft Azure Cosmos DB, detailed in Azure Cosmos DB Vulnerability Details , highlights the need for robust security measures across the board. Knowing this, the potential Iranian cyberattacks become even more concerning; a well-executed attack could exploit such weaknesses, amplifying the impact on North American infrastructure.
Examples of Cyberattacks Attributed to or Suspected of being Linked to Iran
| Attack Name | Date | Target | Methods | Outcomes |
|---|---|---|---|---|
| Operation Olympic Games | 2010-2011 | Various US entities, including corporations and government agencies | Malware deployment, data breaches, and denial-of-service attacks. | Significant damage to targeted organizations. Limited public information available on precise financial and reputational losses. |
| Shamoon | 2012 | Saudi Arabian oil facilities | Malware designed to delete data on infected systems. | Significant operational disruption at Saudi Aramco facilities. Demonstrated the destructive potential of targeted attacks on critical infrastructure. |
| APT33 | 2010-Present | International organizations and governments | Advanced persistent threats (APTs) using spear-phishing, malware, and social engineering tactics. | Compromise of sensitive data and intellectual property, but precise outcomes are often kept confidential. |
Comparison of Past Attacks and Potential Future Threats
Past attacks, such as those in the table above, demonstrate the potential for Iranian-linked cyberattacks to target critical infrastructure and disrupt operations. Future attacks could potentially leverage more sophisticated methods and advanced persistent threats (APTs), targeting broader sectors and employing novel tactics to evade detection. The potential impact of future attacks could be even greater, considering the increasing interconnectedness of systems and the rise of critical infrastructure vulnerabilities.
Impact of Cyberattacks on Target Nations
The impact of cyberattacks attributed to or suspected of being linked to Iran can range from financial losses to reputational damage and operational disruption. In some cases, attacks have directly impacted critical infrastructure, causing significant disruption and potentially threatening public safety. The long-term economic and societal repercussions of such attacks are often substantial and difficult to quantify.
Final Thoughts
The prospect of Iranian cyberattacks on North America presents a complex and multifaceted challenge. The potential for significant damage, from economic disruption to societal upheaval, underscores the urgent need for proactive defense strategies. International cooperation and a robust understanding of potential vulnerabilities are paramount in mitigating the risks. This analysis highlights the crucial importance of preparedness and a multi-faceted approach to cybersecurity.
FAQs
What are some potential targets of Iranian cyberattacks?
Critical infrastructure, financial institutions, and government systems are all potential targets. The aim could be to disrupt services, cause economic damage, or spread misinformation.
What are the potential long-term impacts of such attacks?
Long-term impacts could include damage to international relations, a decline in public trust, and lasting economic instability. The effects could ripple through various sectors of the economy.
What are the most effective defensive strategies against such attacks?
A combination of proactive security measures, robust threat intelligence, and international cooperation is crucial. This includes hardening critical infrastructure, investing in cybersecurity personnel, and sharing threat information.
What role does international cooperation play in countering such threats?
International cooperation is essential for sharing threat intelligence, coordinating responses, and developing effective countermeasures. Information sharing and collaboration are key to protecting against these complex threats.