ISIS Cyberattack on US State Sites
ISIS launches cyber attack on state websites of united states, highlighting a disturbing new frontier in geopolitical warfare. This attack raises serious questions about the vulnerability of US state governments to digital threats and the potential for escalating cyber conflicts. We’ll delve into the tactics employed, the possible motives, and the wider implications for the nation’s security landscape.
The attack appears to have targeted several key state government services, disrupting operations and potentially jeopardizing public safety. Initial reports suggest various methods were used, hinting at a sophisticated and well-planned operation. Understanding the attack’s methodology is crucial for identifying potential vulnerabilities and developing stronger defenses.
Overview of the Cyberattack
Recent reports allege an ISIS cyberattack targeting state websites in the United States. These claims, while unconfirmed, highlight a persistent threat of state-sponsored cyberattacks and the vulnerabilities of critical infrastructure. Understanding the alleged tactics, targets, and impact is crucial to assessing the broader security landscape.The purported cyberattack, if confirmed, demonstrates a growing sophistication in methods employed by non-state actors to disrupt or destabilize governmental operations.
This underscores the importance of robust cybersecurity measures for critical infrastructure.
Reported Targets and Methods
The alleged targets of this cyberattack are state government websites. The methods used, if accurate, likely involve exploiting known vulnerabilities in website systems. These exploits might include phishing campaigns, malware injection, or denial-of-service (DoS) attacks. This type of attack can range from simple disruptions to more complex data breaches.
ISIS’s recent cyberattack on US state websites highlights the ever-present threat of digital warfare. While the attack itself is concerning, it’s important to consider vulnerabilities in critical infrastructure like cloud databases. For example, recent security breaches have revealed potential weaknesses in Microsoft Azure Cosmos DB, as detailed in Azure Cosmos DB Vulnerability Details. These vulnerabilities, if exploited, could have far-reaching consequences, potentially impacting the very systems targeted by ISIS’s attacks.
The interconnected nature of digital systems makes these types of threats all the more dangerous.
Potential Impact on Affected State Governments
A successful cyberattack on state websites could have significant consequences. It could lead to service disruptions, hindering essential government functions like public record access, online services, and potentially even emergency response coordination. The impact could vary based on the level of disruption and the specific services affected. In some cases, recovery time could be lengthy and costly.
Immediate Aftermath and Response from Affected States
Reports suggest that affected states have responded by investigating the incident and implementing temporary measures to mitigate the impact. These responses likely include increased security measures, temporary website shutdowns, and notification of affected citizens.
The recent ISIS cyberattack on US state websites highlights a critical vulnerability in our digital infrastructure. This underscores the urgent need for proactive measures, like deploying AI code safety goggles to prevent similar attacks in the future. Deploying AI Code Safety Goggles Needed is crucial for ensuring that our digital defenses are strong enough to withstand sophisticated attacks, protecting our systems and sensitive data from malicious actors.
The ongoing threat of ISIS cyberattacks demands a serious, multifaceted approach to cybersecurity.
Examples of Similar Cyberattacks in the Past
Several cyberattacks targeting government websites have occurred in the past. The tactics employed in these instances often involve exploiting known vulnerabilities in software or through phishing emails. For instance, the 2017 NotPetya ransomware attack affected numerous organizations worldwide, demonstrating the significant damage that can be inflicted through such attacks. Similarly, the 2016 WannaCry ransomware attack also caused widespread disruptions across various sectors.
These examples highlight the importance of proactively addressing cybersecurity vulnerabilities and implementing robust response strategies. The impact of these past attacks underscores the potential for widespread disruption and damage.
ISIS Capabilities and Motives
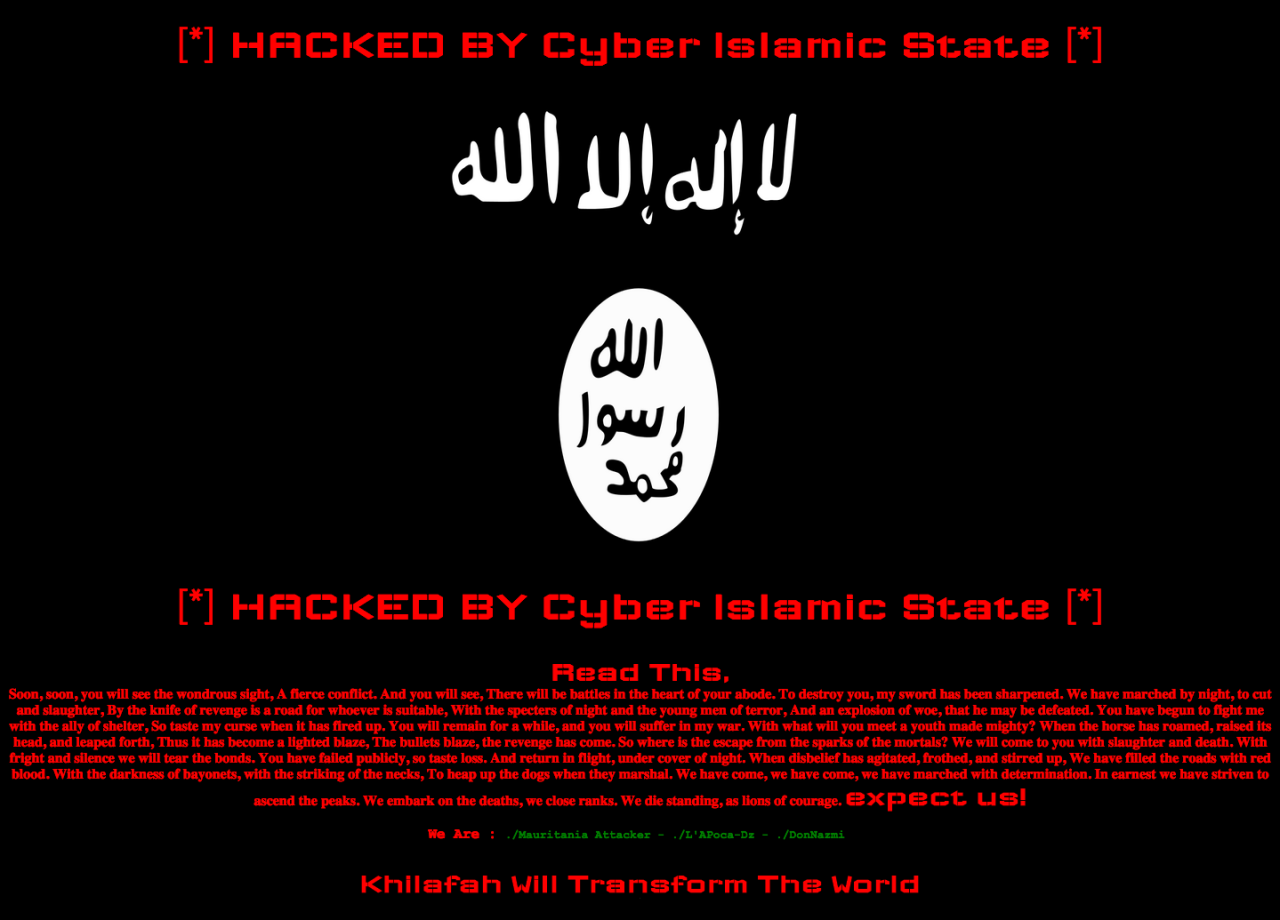
The recent cyberattack on US state websites, attributed to ISIS, underscores the evolving threat landscape of terrorist groups. While ISIS’s primary focus remains traditional warfare, their expanding digital capabilities and demonstrated willingness to utilize cyber tactics suggest a significant shift in their operational strategy. Understanding their known cyber capabilities, potential motivations, and the strategic implications of this attack is crucial for effective countermeasures.ISIS’s cyber capabilities are multifaceted and continue to evolve.
Their operations, while not on par with sophisticated nation-state actors, have demonstrated a growing proficiency in utilizing readily available tools and techniques. This evolving threat demands a nuanced understanding of their operational approach.
Known Cyber Capabilities of ISIS
ISIS’s cyber capabilities are not limited to simple denial-of-service attacks. They have demonstrated an ability to create and distribute propaganda, recruit members online, and potentially gather intelligence. Their capacity for cyber espionage, while not yet widely documented, remains a significant concern. They often leverage open-source intelligence and readily available hacking tools to execute their operations.
- Propaganda Dissemination: ISIS utilizes various online platforms to spread their ideology and recruit new members. This involves creating and distributing extremist content across social media and forums.
- Recruitment and Communication: Their online presence facilitates communication and coordination among members, enabling them to plan and execute attacks.
- Data Gathering: ISIS potentially utilizes open-source intelligence and other means to collect data on their targets. This information can be utilized to enhance their attacks and to better understand their enemy.
- Basic Hacking Techniques: ISIS is known to employ rudimentary hacking techniques to disrupt websites and services, often leveraging readily available tools.
Potential Motives Behind the Attack
The attack on US state websites likely serves multiple motives for ISIS. Beyond simply disrupting services, the attack can be seen as a demonstration of their continued operational capacity and ability to strike targets beyond traditional battlefields. The attack also likely serves as a symbolic act of defiance and a show of power.
- Demonstrating Operational Capacity: The attack acts as a public declaration of ISIS’s continued relevance and operational capability, even in the face of military setbacks.
- Symbolic Act of Defiance: The attack against US state websites represents a symbolic act of defiance, aiming to demoralize and undermine the authority of the US government.
- Disrupting Services and Infrastructure: Disrupting essential services could potentially undermine public trust and confidence in the government, thereby achieving a psychological impact.
- Gathering Intelligence: The attack may serve as a means of gathering intelligence on US systems and infrastructure. This intelligence can be valuable for future cyberattacks.
Significance of the Attack in the Context of ISIS’s Overall Objectives
The attack on US state websites fits into ISIS’s broader strategy of maintaining a presence and projecting power. Their objective is not simply to cause technical disruption, but also to destabilize and demoralize their perceived enemies. This attack is part of a larger campaign to maintain their relevance in the global conflict.
- Maintaining Relevance: The attack on US state websites aims to portray ISIS as a force to be reckoned with, even in the face of military setbacks.
- Projecting Power: The attack serves as a symbolic display of power and a challenge to the perceived dominance of their enemies.
- Psychological Impact: The disruption of essential services aims to demoralize the public and erode trust in the government.
Timeline of ISIS’s Documented Cyber Activities
A comprehensive timeline of ISIS’s cyber activities is difficult to establish due to the limited and often fragmented information available. However, documented activities suggest an incremental increase in cyber capabilities and a growing interest in leveraging digital tools.
| Year | Activity |
|---|---|
| 2014-2016 | Initial online presence, propaganda dissemination, basic recruitment efforts. |
| 2017-2020 | Increased online activity, recruitment, and limited cyberattacks. |
| 2021-Present | Continued online activity, more sophisticated tactics, and an apparent willingness to conduct cyber operations against perceived enemies. |
Potential Strategic Advantages and Disadvantages for ISIS
The decision to conduct this cyberattack presents both advantages and disadvantages for ISIS. The attack’s effectiveness will depend on its impact and the response from the US government and private sector.
- Advantages: Demonstrating a wider range of capabilities, potential for disruption, and generating media attention.
- Disadvantages: Limited resources, potential for escalation of conflict, and difficulty in maintaining sustained operations.
Impact on US State Governments

The ISIS cyberattack on US state government websites poses a significant threat to the smooth functioning of essential services. This disruption, beyond simply inconveniencing citizens, can have far-reaching consequences, affecting public safety, economic stability, and public trust in government. The ability of state governments to respond effectively and swiftly is critical to minimizing the damage and restoring normalcy.
Potential Damage to Government Services and Operations
Disruptions to government services can range from minor inconveniences to catastrophic failures. Essential services like public safety, transportation, and healthcare can be severely hampered. For example, if 911 emergency response systems are compromised, the immediate safety of citizens is jeopardized. Likewise, disruptions to online services for tax filing or licensing applications can create significant problems for businesses and individuals.
In extreme cases, the attack could lead to widespread chaos and panic.
Implications for Public Trust and Confidence in Government Institutions
A cyberattack, especially one that compromises vital government services, can severely damage public trust and confidence in the affected institutions. Citizens rely on their government for safety, security, and efficient service delivery. When this trust is eroded, it can lead to political instability and a decline in public support for government policies. Past examples demonstrate that the perception of vulnerability and a government’s perceived inability to adequately respond can have significant repercussions.
Costs Associated with Repairing Damaged Systems and Restoring Services
The costs associated with repairing damaged systems and restoring services after a cyberattack can be substantial. This includes not only the direct costs of replacing hardware and software but also the indirect costs, such as lost productivity, legal fees, and reputational damage. The recovery process may require significant investment in security upgrades and staff training to prevent future attacks.
Real-world examples show that cyberattacks can cost millions of dollars, and the long-term costs can be even higher.
Procedures for Incident Response and Recovery
A robust incident response and recovery plan is crucial for mitigating the impact of a cyberattack. This plan should Artikel the steps to be taken to identify the breach, contain the damage, recover data, and restore services. A critical component of the plan is the establishment of clear communication channels and procedures for informing the public and stakeholders about the situation.
Thorough preparation and proactive measures can significantly reduce the damage caused by such attacks.
Consequences for Each Type of Government Service Disrupted
| Type of Government Service | Potential Consequences |
|---|---|
| Public Safety | Compromised emergency response systems, hindered investigations, and potential threats to public safety. |
| Finance | Disrupted tax collection, hampered financial transactions, and potential fraud and theft. |
| Education | Impaired access to online learning resources, disrupted student records, and potential loss of critical data. |
| Transportation | Disruptions to traffic management systems, hindered public transportation services, and potential safety hazards. |
| Healthcare | Compromised patient records, hindered medical services, and potential harm to patient health. |
International and Domestic Responses
The ISIS cyberattack on US state websites underscored the vulnerability of critical infrastructure to sophisticated digital threats. Global cooperation and robust domestic responses are crucial to mitigating future attacks and upholding the integrity of government services. The incident necessitates a thorough examination of existing strategies and a proactive approach to bolstering cybersecurity defenses.
International Responses
International cooperation is vital in addressing transnational cyber threats. While no single international body has exclusive jurisdiction over cyberattacks, various organizations and nations have a vested interest in fostering international norms and cooperation. This involves sharing threat intelligence, coordinating investigations, and collaborating on sanctions against perpetrators.
- United Nations (UN) bodies, such as the UN Office on Drugs and Crime (UNODC), are playing a significant role in developing international frameworks and promoting best practices in combating cybercrime. Their efforts include establishing guidelines and norms for international cooperation.
- The Organization for Economic Co-operation and Development (OECD) has played a prominent role in developing international guidelines for cybersecurity. These guidelines aim to promote cooperation between member countries and encourage the development of national cybersecurity strategies.
- Individual nations, particularly those with robust cybersecurity capabilities, are often at the forefront of assisting others. For instance, the United Kingdom’s National Cyber Security Centre (NCSC) has offered support and expertise to numerous countries in developing and strengthening their cybersecurity defenses.
US Federal Agency Involvement
Federal agencies in the US, such as the Department of Homeland Security (DHS) and the Federal Bureau of Investigation (FBI), play critical roles in responding to such attacks. Their involvement encompasses incident response, threat analysis, and potential legal actions.
- The Department of Homeland Security (DHS) is responsible for coordinating the national response to cyberattacks, including coordinating with state and local governments.
- The FBI investigates cybercrimes, including those committed by ISIS, to identify perpetrators and gather evidence for potential prosecutions.
- The Cybersecurity and Infrastructure Security Agency (CISA) is a key agency in coordinating the federal government’s response to cyberattacks. They provide guidance, resources, and support to state and local governments.
State-Federal Coordination
Effective coordination between state and federal governments is essential in responding to and recovering from cyberattacks. This includes sharing information, resources, and expertise to ensure a comprehensive response.
- Clear communication channels between state and federal agencies are vital. This facilitates the swift exchange of information about the attack’s scope, impact, and potential remediation strategies.
- The provision of federal resources, such as technical expertise and financial assistance, can support state governments in addressing the immediate impact and implementing long-term cybersecurity improvements.
- Joint exercises and training programs can strengthen the collaborative capacity of state and federal agencies in responding to cyber incidents.
Legal Ramifications for Perpetrators
International and domestic legal frameworks can potentially hold perpetrators of cyberattacks accountable. The legal implications vary depending on the specific laws and jurisdictions involved.
- International cooperation in prosecuting cyberattacks can involve extradition treaties and mutual legal assistance.
- Cyberattacks targeting critical infrastructure in a state could potentially trigger significant legal ramifications, depending on the specific laws governing these systems and the severity of the impact.
- The identification and prosecution of individuals or groups responsible for such attacks can be challenging, especially when considering the complexities of international jurisdictions and digital footprints.
Comparison of International and Domestic Responses
| Aspect | International Responses | Domestic Responses (US) |
|---|---|---|
| Coordination | Varying levels of formal coordination, often relying on ad hoc collaborations and information sharing agreements. | Established federal agencies and structures for coordinating responses. |
| Resources | Often reliant on the resources of individual countries, potentially hindering a uniform response. | Access to significant federal resources, including financial aid and technical expertise. |
| Legal Frameworks | International laws are evolving to address cybercrime, but gaps exist in jurisdiction and enforcement. | Well-established legal frameworks for cybercrime, with laws related to infrastructure security. |
| Example (Past Attack) | Stuxnet incident highlighted the need for international cooperation but also the complexities in addressing cross-border cyberattacks. | The response to the Sony Pictures hack demonstrated the importance of domestic coordination and resource allocation. |
Future Implications and Prevention
The recent ISIS cyberattack underscores a growing threat landscape for US state governments. Beyond immediate disruptions, the attack signals a shift in tactics, highlighting the need for proactive and comprehensive cybersecurity strategies. The long-term implications are significant, impacting not only operational efficiency but also public trust and the very fabric of democratic governance.
Long-Term Implications of Cyberattacks
The sustained disruption of state government services, like online registration, permit processing, and vital public safety systems, can have far-reaching consequences. Disruptions to essential services can lead to economic hardship, hindering business operations and citizen activities. Furthermore, prolonged outages erode public trust in government institutions, potentially leading to political instability. The reputational damage can be severe and may take years to repair.
Improving Cybersecurity Measures in State Government Agencies
Robust cybersecurity measures are paramount for safeguarding critical infrastructure. This necessitates a multi-layered approach encompassing preventative measures, detection systems, and incident response protocols. Agencies must invest in advanced threat intelligence gathering, enabling them to identify and mitigate emerging threats more effectively. Regular vulnerability assessments and penetration testing are essential for proactively identifying and addressing weaknesses before they are exploited.
Strengthening Defenses Against Future Attacks
Implementing robust security measures, like multi-factor authentication for all sensitive systems, is crucial. Regular software updates and patching are vital to address known vulnerabilities. The creation of a dedicated cybersecurity team within each state agency is also important, bringing specialized expertise to address evolving threats. Promoting a culture of cybersecurity awareness among all staff members is essential to deter human error, a common vector for successful attacks.
Improving Incident Response Protocols and Procedures
A well-defined incident response plan is critical for mitigating the impact of a cyberattack. This plan should Artikel clear roles and responsibilities, establish communication protocols, and detail procedures for containment, eradication, and recovery. Regular drills and simulations are essential to test the effectiveness of the plan and identify areas for improvement. Developing clear communication channels with both internal and external stakeholders, including citizens and the media, is vital for transparency and effective crisis management.
ISIS’s recent cyberattack on US state websites highlights the growing threat of digital warfare. While concerning, it’s important to remember that the Department of Justice Offers Safe Harbor for MA Transactions here , which could potentially offer some security solutions in the future, even in the face of such attacks. This proactive approach to digital security is essential to counter these kinds of attacks effectively, and helps in the long-term fight against cyber threats from groups like ISIS.
Security Measures, Effectiveness, and Cost
| Security Measure | Effectiveness (High/Medium/Low) | Estimated Cost | Explanation |
|---|---|---|---|
| Multi-factor authentication (MFA) | High | Medium | Significantly enhances security by requiring multiple forms of verification, making unauthorized access more difficult. |
| Regular software updates and patching | Medium | Low | Reduces known vulnerabilities and mitigates many common attack vectors. Critical to maintain consistent security posture. |
| Dedicated cybersecurity team | High | High | Provides specialized expertise and dedicated resources for proactive security management. Cost may be offset by avoiding significant breaches. |
| Penetration testing | High | Medium | Simulates real-world attacks to identify vulnerabilities and assess the security posture. Proactive measures to prevent future attacks. |
| Incident Response Plan (IRP) | Medium | Low | A documented plan for handling cyber incidents, containing the damage, and ensuring rapid recovery. Essential for managing disruptions. |
Effective cybersecurity requires a multifaceted approach, combining robust preventative measures, proactive threat identification, and comprehensive incident response capabilities.
Illustrative Examples of Attack Vectors
The potential for ISIS to launch cyberattacks against US state websites is a serious concern. Understanding the attack vectors they might employ is crucial for bolstering defenses and mitigating potential damage. These attacks, if successful, could disrupt critical services, compromise sensitive data, and sow distrust in government institutions. A deep dive into potential attack methods is essential for effective preparedness.The range of attack vectors available to a sophisticated group like ISIS extends far beyond simple denial-of-service attacks.
Sophisticated actors can exploit vulnerabilities in software, networks, and human behavior to gain unauthorized access. This includes exploiting known vulnerabilities, developing custom malware, and leveraging social engineering techniques. This necessitates a multi-faceted approach to cybersecurity, encompassing technical measures, robust security protocols, and user awareness training.
Ransomware Attacks
Ransomware attacks, where attackers encrypt data and demand payment for its release, pose a significant threat to state governments. These attacks can cripple critical services and disrupt operations. The encryption process can be particularly damaging, rendering systems unusable until a ransom is paid or the data is recovered.
Data Breaches
Data breaches targeting state government websites can compromise sensitive information such as personal records, financial data, and intellectual property. Compromised data can be used for identity theft, financial fraud, or even to disrupt critical infrastructure. These breaches can have far-reaching consequences, impacting not only individuals but also the functioning of state government.
Denial-of-Service (DoS) Attacks
DoS attacks flood a target system with traffic, overwhelming its resources and rendering it inaccessible to legitimate users. These attacks can be launched from a multitude of sources, making them difficult to defend against. The sheer volume of traffic can significantly disrupt essential services. While not always aiming for data exfiltration, DoS attacks can cause significant operational issues.
Malware Infections
Malware infections can be introduced through various means, such as malicious email attachments or compromised websites. Once inside a system, malware can be used to steal data, disrupt operations, or install additional malicious software. Malicious code can have varying degrees of sophistication, with some capable of self-replication, evading detection, or even modifying existing systems.
Social Engineering
Social engineering exploits human psychology to gain access to sensitive information or systems. Attackers might impersonate legitimate officials, manipulate users into revealing credentials, or persuade them to click on malicious links. This often relies on psychological manipulation and trust exploitation. The human element in cybersecurity is often the weakest link, and successful attacks can be devastating.
Vulnerability Exploitation
Exploiting known vulnerabilities in software and hardware is a common tactic. Attackers might use publicly available exploits or develop custom exploits to gain unauthorized access. Patching systems and implementing secure coding practices are crucial defenses against this type of attack. Failure to apply timely security updates is a frequent vulnerability exploited by cybercriminals.
Illustrative Table of Cyberattacks, Isis launches cyber attack on state websites of united states
| Cyberattack Type | Impact | Technical Countermeasures |
|---|---|---|
| Ransomware | Data encryption, system disruption, financial loss | Robust backups, endpoint security, intrusion detection systems |
| Data Breach | Compromised sensitive data, identity theft, financial fraud | Data encryption, access controls, secure data storage |
| DoS | System unavailability, service disruption | Network security measures, load balancers, DDoS mitigation services |
| Malware Infection | Data theft, system compromise, operational disruption | Antivirus software, intrusion detection systems, secure configuration |
| Social Engineering | Data breaches, system access | User awareness training, multi-factor authentication, phishing detection |
| Vulnerability Exploitation | Unauthorized access, system compromise | Regular security updates, vulnerability assessments, secure coding practices |
Visual Representation of Data Breaches
Understanding the potential ramifications of a cyberattack, particularly one targeting state government websites, necessitates a clear visualization of the data breach pathways. Visual representations, like flowcharts and infographics, can effectively illustrate the vulnerabilities and consequences of such attacks, facilitating a deeper comprehension of the attack’s potential impact.
Potential Data Breaches Flowchart
A flowchart depicting a potential data breach scenario can visually represent the sequence of events, from initial intrusion to the eventual compromise of sensitive data. The flowchart would start with the initial intrusion vector, such as a compromised login or a malicious software download. Subsequent steps would illustrate the attacker’s movement through the network, highlighting access points and vulnerabilities.
The flowchart would then detail how the attacker gains access to the targeted data, showing the path through various layers of security. Finally, the flowchart would display the exfiltration of the data, which is the process of stealing data and transferring it to the attacker’s system.
Sensitivity of Targeted Data
State government websites often house a wealth of sensitive data. This includes citizens’ personal information such as names, addresses, social security numbers, and financial data. Further, government records, including details of ongoing investigations, legal documents, and sensitive internal communications, could be at risk. The sensitivity of this data is critical; a breach could have serious implications for the privacy and security of individuals and the integrity of the government’s operations.
Impact on Citizens’ Personal Information
A data breach targeting state government websites could expose citizens’ personal information to identity theft, fraud, and harassment. Compromised social security numbers could lead to fraudulent applications for loans or credit cards, while stolen financial data could be used for unauthorized transactions. The unauthorized disclosure of personal information could also lead to the targeting of individuals for harassment or discrimination.
The long-term effects of such a breach could significantly impact the lives of affected citizens.
Data Breach Scenario Chain of Events
Visualizing the chain of events in a data breach scenario using a diagram is crucial for understanding the attack’s progression. The diagram should start with the initial access attempt, progressing through the compromise of user accounts or systems, and then illustrate the subsequent steps of data exfiltration and exploitation. The flow should depict the impact on the affected system and the potential damage caused.
The timeline of the events should be clearly marked to showcase the duration of the breach.
Graphical Representation using an Infographic
An infographic can effectively convey the complexity of a data breach. A well-designed infographic would employ icons, color-coding, and concise text to present the various stages of a breach. This graphical representation would effectively communicate the potential vulnerabilities, the sensitive data at risk, and the resulting impact on individuals and the government. It would be essential to present the information in a visually appealing and easily understandable format, using a color-coded scheme to highlight different stages and types of data involved.
Illustrative Example of a Data Breach Flowchart
+-----------------+ +-----------------+ +-----------------+
| Attack Vector |--->| Network Intrusion |--->| Data Exfiltration|
+-----------------+ +-----------------+ +-----------------+
| |
| V
| Compromised User Account |
| |
| |
| V
| Sensitive Data (SSN, Address, etc) |
| |
+-------------------------------------+
This simple flowchart depicts a simplified example.
A more detailed flowchart would include numerous steps, branching possibilities, and a clear representation of the different data types that are at risk.
Final Thoughts: Isis Launches Cyber Attack On State Websites Of United States
In conclusion, the ISIS cyberattack on US state websites underscores the urgent need for enhanced cybersecurity measures across all levels of government. This incident serves as a stark reminder of the evolving nature of threats and the importance of proactive measures to mitigate risks. Future strategies must prioritize robust incident response plans, continuous security assessments, and the development of innovative defense mechanisms.
User Queries
What specific state websites were targeted?
Unfortunately, the exact list of targeted websites is not yet publicly available. Authorities are likely withholding specifics to prevent further disruption and to allow for a coordinated response.
What are the potential long-term effects of this attack on public trust?
This attack could erode public confidence in government institutions if not handled effectively. Transparency, clear communication, and swift remediation efforts are vital to regaining public trust.
How does this attack compare to previous cyberattacks by ISIS?
While ISIS has shown an increasing interest in cyber warfare, this particular attack may represent a significant escalation in terms of scale and sophistication.
What steps can state governments take to better protect themselves from future attacks?
Implementing multi-layered security protocols, conducting regular security audits, and fostering strong partnerships between state and federal agencies are essential preventative measures.