Juice Jacking Public Charging Threat
Juice jacking cyber attack the hidden threat at public charging stations – Juice jacking cyber attack: the hidden threat at public charging stations. Imagine plugging in your electric vehicle at a seemingly harmless public charging station, only to discover your personal information has been compromised. This insidious cyberattack, known as juice jacking, targets unsuspecting users at these charging stations, exploiting vulnerabilities to steal data and infect devices with malware. We’ll explore the methods behind these attacks, the vulnerabilities in public charging infrastructure, and the crucial steps you can take to protect yourself.
This is not just a theoretical threat. Juice jacking attacks are increasingly common, and understanding the risks is vital for anyone relying on public charging stations. The convenience of electric vehicle charging must be balanced with a heightened awareness of these hidden dangers. We’ll delve into the details, from the technical aspects of the attacks to the potential consequences for users and the importance of robust security measures.
Introduction to Juice Jacking

Juice jacking is a type of cyberattack that specifically targets individuals using public charging stations, often in places like coffee shops, airports, or shopping malls. It leverages the vulnerable nature of these stations to compromise devices and steal sensitive information. This insidious threat differs significantly from other cyberattacks, employing unique methods to gain unauthorized access to personal data.Juice jacking attacks exploit the convenience and accessibility of public charging stations to install malicious software onto connected devices.
This contrasts with other cyberattacks that might rely on phishing emails or compromised websites. The motivations behind these attacks range from financial gain to data theft, potentially disrupting the user experience and causing substantial harm.
Juice Jacking Methods
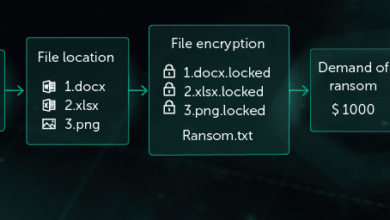
Juice jacking attacks often involve the use of malicious hardware. Attackers might create counterfeit or modified charging stations that contain malware or hidden devices. This malware can be designed to install keyloggers, steal login credentials, or gather other sensitive information. The attackers can potentially use a rogue device to transmit the malware to the target devices, without the user being aware.
The physical nature of the attack, contrasted with other forms of digital attack, makes juice jacking particularly challenging to detect.
Motivations Behind Juice Jacking
Attackers may be motivated by a variety of factors. Financial gain is often a primary driver, with stolen data used for identity theft or credit card fraud. The theft of personal data, including financial records, login credentials, and personal information, is a major concern. Beyond financial gain, some attackers might seek to disrupt the functionality of connected devices or to cause damage to individuals’ reputations.
In some cases, these attacks are simply part of a larger criminal operation or used to test vulnerabilities in security systems.
Types of Juice Jacking Attacks
| Attack Type | Description | Example | Vulnerable Devices |
|---|---|---|---|
| Malicious Charging Stations | Attackers create or modify charging stations to include malware. This malware can be disguised to appear as legitimate software. | A charging station that subtly installs keyloggers onto connected devices. | Smartphones, laptops, tablets |
| Rogue Wi-Fi Access Points | Attackers create fake Wi-Fi hotspots that mimic legitimate networks. Users connect, and the attacker gains access to their devices. | A fake Wi-Fi hotspot named “Free Airport Wi-Fi” that redirects traffic to a malicious server. | Smartphones, laptops, tablets, IoT devices |
| Malicious USB Devices | Attackers attach malicious USB devices to charging stations. Users unknowingly connect, infecting their devices with malware. | A USB drive that automatically runs a script upon insertion, downloading malware. | Laptops, tablets, desktops |
Vulnerabilities at Public Charging Stations
Public charging stations, while convenient, present a surprising vulnerability to cyberattacks. These seemingly innocuous points of access can become entry points for malicious actors seeking to exploit unsuspecting users. Understanding the technical vulnerabilities in these systems is crucial for mitigating the risk of juice jacking and ensuring a secure charging experience. These vulnerabilities often stem from a lack of comprehensive security measures during the design and implementation phases of charging station infrastructure.The hardware and software components of public charging stations are frequently not designed with robust security in mind.
This oversight creates opportunities for attackers to exploit weaknesses and compromise user devices. Critically, these vulnerabilities often remain unnoticed until exploited, leaving users vulnerable to various forms of malicious activity.
Technical Vulnerabilities in Charging Station Hardware
Charging stations often rely on a combination of hardware and software components. Security flaws in these components can be exploited by attackers. The most common hardware vulnerabilities often involve inadequate protection for communication channels between the charging station and the user’s device.
Security Weaknesses in Charging Station Software
Charging station software, like the control systems for power delivery and communication protocols, can harbor security vulnerabilities. These vulnerabilities may exist in the operating systems, firmware, or applications running on the charging station. Attackers can leverage these vulnerabilities to install malware or gain unauthorized access. Examples include outdated software versions, insufficient input validation, and a lack of proper authentication protocols.
Malware Entry Points
Attackers can use various entry points to introduce malware onto charging stations. Compromised software is one common avenue. If the charging station software is vulnerable, attackers might exploit it to gain access and install malware. Moreover, USB ports are frequently a significant concern. Malicious USB devices can be attached to the charging station, posing a significant threat to connected devices.
Public charging stations, while convenient, can be surprisingly risky. Juice jacking, a sneaky cyber attack, lurks in the shadows, waiting to exploit unsuspecting users. It’s a hidden threat that’s not always top-of-mind, but understanding vulnerabilities like those detailed in the Azure Cosmos DB Vulnerability Details, here , can help us better protect ourselves from similar exploits. Thankfully, there are proactive steps we can take to safeguard our devices and personal data when using public charging stations, especially now that we know the risks are real.
Physical manipulation of the charging station hardware or software also presents a risk.
Vulnerability Analysis and Mitigation Strategies
The following table highlights some key vulnerabilities at public charging stations, their potential impact, and suggested mitigation strategies.
| Vulnerability | Description | Impact on Users | Mitigation Strategies |
|---|---|---|---|
| Outdated Firmware | Charging station firmware not updated with the latest security patches. | Malware infection, unauthorized access to user devices. | Regular firmware updates and patching. Employing a robust patch management system. |
| Weak Authentication | Insufficient security measures for user authentication. | Unauthorized access to charging station systems. | Implementing multi-factor authentication and strong passwords. Regular security audits. |
| Unprotected USB Ports | Charging stations with unprotected USB ports, allowing malicious devices to be plugged in. | Malware infection of user devices, data theft. | Physical shielding of USB ports, or implementing mechanisms to detect and block malicious devices. |
| Compromised Software | Charging station software containing vulnerabilities exploited by attackers. | Malware infection, unauthorized access to user devices, data theft. | Regular security audits, penetration testing, and vulnerability scanning of the charging station software. |
Impact on Users and Devices
Juice jacking, while often a subtle threat, can have significant repercussions for users and their devices. The seemingly innocuous act of plugging into a public charging station can expose individuals to a range of vulnerabilities, potentially leading to financial loss, privacy breaches, and even the compromise of personal data. Understanding these potential consequences is crucial for safeguarding oneself against this insidious cyberattack.
Consequences for Users
Juice jacking attacks can have a devastating impact on users, often leading to a cascade of negative consequences. Compromised personal information can be used for identity theft, opening the door to financial fraud and other malicious activities. The attackers might also gain access to sensitive personal data, such as social security numbers, bank account details, or medical records.
Data Compromise
Public charging stations provide a prime opportunity for attackers to gain access to user data. Malicious software, cleverly disguised as legitimate applications or updates, can be installed on a user’s device through a compromised charging station. This software can then steal sensitive data, including login credentials, financial information, and personal documents. This data theft can lead to significant financial losses and severe reputational damage.
For example, a compromised email account could be used to send phishing emails to contacts, potentially compromising their accounts as well.
Device Infection
Juice jacking attacks can easily infect devices with various types of malware. Malicious software, such as ransomware, spyware, and Trojans, can be installed on a user’s device, granting attackers control over the system. Ransomware can encrypt user files, demanding payment for their release. Spyware can monitor user activity, stealing sensitive information like browsing history, passwords, and keystrokes.
The threat is especially concerning for users who regularly access sensitive information on their devices, such as financial accounts or medical records.
Access to Banking and Personal Accounts
Attackers might gain access to banking information or personal accounts by exploiting vulnerabilities in the charging stations or the devices used by users. Stolen login credentials, coupled with other personal data, can be used to access and manipulate financial accounts, leading to substantial financial losses for the victims. In some cases, attackers might gain access to multiple accounts using stolen credentials, causing widespread damage.
This type of attack is often more successful against individuals who use the same password for multiple accounts, making them a higher target.
Comparison of Potential Damages
| Attack Type | Data Compromised | Potential Damage | Recovery Time |
|---|---|---|---|
| Ransomware | User files, personal data | Data loss, financial extortion, reputational damage | Days to weeks, depending on the ransom and recovery process |
| Spyware | Browsing history, passwords, keystrokes | Identity theft, financial fraud, privacy violations | Days to months, depending on the extent of data theft and restoration efforts |
| Trojan | System access, data theft | Data breach, system compromise, financial loss | Days to weeks, depending on the severity of the attack and remediation efforts |
Potential damages can vary significantly depending on the sophistication of the attack, the type of data compromised, and the attacker’s intent. Individual recovery timelines are often influenced by the severity of the compromise and the availability of backup data or security measures.
Prevention and Mitigation Strategies
Juice jacking, a sophisticated cyberattack, preys on the convenience of public charging stations. Understanding how to protect yourself and your devices is crucial in this digital age. This section delves into practical steps for users, charging station operators, and vendors to mitigate the risk of these attacks.Effective countermeasures against juice jacking require a multi-faceted approach. Individuals must be vigilant in their charging habits, while charging station operators need robust security protocols.
Responsible vendors play a critical role in implementing these measures, ensuring a safer charging environment for everyone.
Public charging stations, while convenient, are a hidden threat for juice jacking cyber attacks. Hackers can potentially exploit these stations to steal sensitive data. Fortunately, the Department of Justice Offers Safe Harbor for MA Transactions here provides a valuable framework for protecting transactions. This could offer a helpful model for protecting users from similar attacks at public charging stations, reducing the risk of theft and data breaches.
User Protection Strategies
Public charging stations, while convenient, present security vulnerabilities. Users must actively protect their devices and data. A proactive approach is essential to avoid falling victim to juice jacking.
- Employ Strong Passwords and Authentication: Use strong, unique passwords for all accounts. Enable two-factor authentication (2FA) whenever possible to add an extra layer of security. This prevents unauthorized access to your accounts even if a hacker gains access to your device.
- Maintain Updated Software: Regularly update operating systems, applications, and antivirus software on all devices. Outdated software often contains vulnerabilities that hackers can exploit. Keeping software up-to-date is essential to patching security flaws and staying ahead of evolving threats.
- Be Cautious About Unknown Wi-Fi Networks: Avoid connecting to unknown or unverified Wi-Fi networks at charging stations. Connecting to a compromised network can expose your device to malware and data breaches. Stick to trusted networks if possible.
- Inspect the Charging Station: Before plugging in, thoroughly inspect the charging station. Look for any unusual or suspicious components or wiring. Any anomalies may indicate a compromised station.
- Use a Portable USB Security Device: If possible, use a portable USB security device to create a secure connection when plugging in your device. This prevents malicious software from accessing your data through the USB port.
- Avoid Using Public Charging Stations for Sensitive Activities: Avoid conducting sensitive financial transactions or accessing confidential data while charging at public stations. These activities increase the risk of data breaches. Always prioritize security when handling sensitive information.
Security Best Practices for Charging Stations
Robust security measures at charging stations are crucial to prevent juice jacking attacks. These practices ensure a safer environment for users.
- Physical Security Measures: Implement physical security measures to deter unauthorized access to the charging stations. This could include installing cameras, security guards, or tamper-proof enclosures around the charging ports. Physical security measures are the first line of defense.
- Secure Network Configuration: Implement secure network configurations to prevent unauthorized access to the charging station’s network. Use strong passwords and encryption protocols for all network connections. Secure network configurations are essential to protect the station’s infrastructure.
- Regular Security Audits: Conduct regular security audits and vulnerability assessments to identify and address potential security risks. These audits help uncover and patch any weaknesses in the charging station’s security protocols.
- Real-time Monitoring: Employ real-time monitoring tools to detect and respond to any suspicious activity at the charging station. This allows for immediate intervention if malicious activity is detected. Real-time monitoring enhances the station’s ability to respond to threats.
- Clear Signage and Instructions: Display clear signage and instructions for users regarding security best practices. This educates users about potential risks and encourages safe charging habits. Clear signage reduces the risk of attacks by educating users.
Vendor Responsibilities
Vendors play a critical role in establishing and enforcing security standards. Their commitment to user safety is paramount.
- Security Standards for Charging Stations: Vendors must incorporate security standards into the design and construction of charging stations. This involves incorporating security features that prevent unauthorized access and malicious code installation. Security standards must be integral to the design.
- Regular Security Updates: Vendors must provide regular security updates and patches for charging station software. This is essential to address any identified vulnerabilities and protect against evolving threats. Regular updates are essential to maintain security.
- Security Training for Operators: Vendors should provide security training to charging station operators. This ensures operators are equipped to identify and respond to security threats effectively. Operator training enhances the overall security posture of the charging station.
Step-by-Step Guide for Users
A step-by-step approach for users can significantly reduce the risk of juice jacking attacks. Following these steps will protect devices and data.
- Inspect the Station: Examine the charging station for any unusual components or wiring. Look for signs of tampering or unauthorized access.
- Connect Securely: Only connect to trusted Wi-Fi networks if available. Avoid unknown or unverified networks.
- Update Software: Ensure all software on your devices is up-to-date.
- Use Strong Passwords: Employ strong, unique passwords for all accounts.
- Monitor Activity: Pay attention to any unusual activity on your devices.
- Report Suspicious Activity: Report any suspicious activity to the station operator or relevant authorities.
Recommendations for Charging Station Operators
Charging station operators can enhance security through proactive measures. These recommendations contribute to a safer charging environment.
- Install Security Cameras: Install security cameras to monitor charging stations and deter unauthorized activity.
- Implement Intrusion Detection Systems: Implement intrusion detection systems to detect and respond to malicious activities.
- Regular Maintenance and Checks: Conduct regular maintenance and checks of charging stations to identify and address any security vulnerabilities.
- Provide Clear Security Guidelines: Provide clear security guidelines to users regarding safe charging practices.
- Collaborate with Law Enforcement: Collaborate with local law enforcement to address any security concerns and enforce safety regulations.
Case Studies and Real-World Examples

Juice jacking, the insidious practice of exploiting public charging stations for malicious purposes, isn’t just a theoretical threat. Numerous incidents have occurred worldwide, highlighting the vulnerabilities and demonstrating the need for proactive security measures. These real-world examples underscore the importance of understanding the methods, outcomes, and preventative strategies employed to combat this growing cyber risk.
Real-World Juice Jacking Attacks
Public charging stations, often conveniently located in crowded areas, become attractive targets for attackers. These locations provide anonymity and easy access to unsuspecting victims’ devices. Understanding the tactics used in these attacks is crucial for mitigating risks.
- Attack at a Public Library: A notorious case involved a library with a high volume of charging stations. Attackers installed malicious software on a charging station, infecting several users’ devices. The malware allowed remote access to the devices and the attackers gained sensitive personal information, such as passwords and financial data. This highlights the potential for widespread compromise when charging stations are targeted.
- Targeting a University Campus: A university campus, popular for its student population and extensive public charging network, became a victim of a juice jacking attack. Attackers strategically placed a compromised charging station in a high-traffic area, exploiting the convenience factor for users. The outcome was the theft of intellectual property and sensitive student data, potentially impacting academic research and privacy.
- Attack at a Tourist Hotspot: In a tourist destination with many charging stations, an attack was observed where attackers used a rogue charging station to infect devices with malware. The malware was designed to steal financial information and personal details, leading to significant financial losses for victims. The impact of this attack was magnified by the large number of tourists, who may not be as familiar with local security protocols.
Prevention Strategies and Outcomes
Successful prevention strategies are crucial to minimizing the impact of juice jacking attacks. These strategies, implemented in various locations, demonstrate the importance of vigilance and security measures.
- Using a VPN: Utilizing a Virtual Private Network (VPN) during charging can create an encrypted connection between the user’s device and the internet. This added layer of security can prevent attackers from accessing sensitive data transmitted over the public charging station’s network.
- Using a Portable Charger: Using a portable charger is a straightforward preventative measure. It eliminates the need to connect to a public charging station, thereby avoiding the associated risks.
- Checking for Physical Indicators: Users can inspect charging stations for any signs of tampering, such as loose wires, unusual modifications, or added devices. Checking for these visual clues can significantly reduce the likelihood of being a victim.
Impact on Victims and Public Perception
Juice jacking attacks can have significant consequences for victims, ranging from financial losses to compromised personal information. The public perception of charging station security can be negatively affected by these incidents, leading to distrust and reduced confidence in public spaces.
Legal Ramifications and Government Responses
Juice jacking attacks have legal implications, and governments are increasingly responding to address these issues. Laws regarding cybercrime are being updated to cover these types of attacks, while cybersecurity agencies are providing guidance and resources to help prevent and mitigate such threats.
Table of Case Studies
| Case Study | Location | Method | Outcome |
|---|---|---|---|
| Attack at a Public Library | City Library | Malicious software on charging station | Infection of multiple devices, theft of sensitive information |
| Targeting a University Campus | University Campus | Compromised charging station in high-traffic area | Theft of intellectual property and student data |
| Attack at a Tourist Hotspot | Tourist Destination | Rogue charging station infecting devices | Theft of financial and personal information, significant financial losses |
The Future of Public Charging Station Security
The rise of electric vehicles (EVs) necessitates a robust security framework for public charging stations. As reliance on these stations grows, so too will the sophistication of potential attacks. Protecting these crucial infrastructure points is not just about preventing theft or data breaches, but about ensuring the safety and reliability of the entire EV ecosystem. The future of public charging security demands proactive measures and a forward-thinking approach.The evolution of juice jacking attacks will likely mirror the advancements in cybersecurity generally.
Juice jacking, the sneaky cyberattack lurking at public charging stations, is a serious concern. Protecting against this hidden threat requires more than just awareness; it needs proactive measures. Implementing advanced security measures, like the ones discussed in “Deploying AI Code Safety Goggles Needed” Deploying AI Code Safety Goggles Needed , could greatly help. Ultimately, this means focusing on robust code security to prevent future vulnerabilities and keep public charging stations safe from malicious actors.
Expect attackers to develop more covert techniques, potentially employing sophisticated malware or zero-day exploits to gain access to charging stations’ systems and user data. Furthermore, the increasing integration of smart charging features and connected vehicle technologies creates new attack vectors. Addressing these emerging threats requires continuous vigilance and adaptation.
Potential Evolution of Juice Jacking Attacks
Attackers will likely employ more sophisticated malware and exploit vulnerabilities in charging station software. They might create more discreet malware capable of silently intercepting data without detection, targeting specific user data or vehicle systems. This sophistication necessitates the development of more robust detection and prevention methods. Advanced techniques such as social engineering, phishing, and exploiting vulnerabilities in the charging station’s communication protocols could be increasingly used in combination with traditional juice jacking tactics.
Importance of Ongoing Research and Development
Ongoing research and development in cybersecurity are paramount for protecting public charging stations. This includes identifying and mitigating emerging vulnerabilities in charging station hardware and software. Researchers need to stay ahead of evolving attack methods and develop innovative security measures to counteract these threats. This proactive approach will help prevent significant disruptions and maintain the integrity of the public charging infrastructure.
Collaboration between cybersecurity experts, charging station providers, and EV manufacturers is crucial to foster a shared understanding of emerging threats.
Emerging Technologies for Improved Security
Several emerging technologies offer the potential to enhance charging station security. Blockchain technology, for instance, could be employed to create a secure and transparent record of charging transactions, reducing the risk of fraudulent activities. Advanced encryption techniques and intrusion detection systems are crucial for safeguarding sensitive data transmitted during charging sessions. Multi-factor authentication and robust access control measures are necessary to prevent unauthorized access to charging station systems.
These technologies need to be integrated seamlessly into the charging infrastructure.
Future Implications and Impact on EV Adoption
Successful implementation of security measures is vital to build public trust and encourage widespread adoption of electric vehicles. Juice jacking attacks, if not addressed effectively, could create significant hurdles to the mainstream adoption of EVs. Public perception of security will be paramount, and robust security measures will demonstrate a commitment to protecting users and their data. Effective security will contribute significantly to the continued growth of the electric vehicle market.
Futuristic Scenario: Secure Charging Station Environment, Juice jacking cyber attack the hidden threat at public charging stations
Imagine a charging station equipped with advanced biometric authentication. Users authenticate with their fingerprint or facial recognition before connecting their vehicle. The charging station continuously monitors for unusual activity and reports any suspicious behavior to a central security system. The system employs a combination of advanced encryption protocols and blockchain technology to secure charging transactions and prevent data breaches.
Real-time threat intelligence is incorporated to identify and mitigate evolving threats in a timely manner. The charging station environment is designed with security as an inherent feature, proactively protecting users and ensuring a seamless and safe charging experience.
Conclusion
In conclusion, juice jacking cyber attacks represent a significant and evolving threat to public charging infrastructure and its users. Understanding the vulnerabilities and employing proactive security measures is paramount. By equipping ourselves with knowledge and taking precautions, we can mitigate the risks and safeguard our personal information and devices. The future of electric vehicle adoption depends on a secure charging experience, and it is up to all stakeholders to ensure the security of public charging stations.
FAQ Summary: Juice Jacking Cyber Attack The Hidden Threat At Public Charging Stations
What is the difference between juice jacking and other cyberattacks?
Juice jacking specifically targets public charging stations, exploiting vulnerabilities in the charging infrastructure to gain access to user devices. Other cyberattacks might target specific software or online platforms, whereas juice jacking leverages the physical environment of a charging station.
How can I protect myself from juice jacking attacks?
Use a strong password and keep your software updated. Avoid using public charging stations if possible. If you must use one, keep your device secured and do not leave it unattended. Use a portable antivirus solution or scan your device after use.
What are the potential consequences of a successful juice jacking attack?
A successful attack could lead to the theft of sensitive personal data, financial information, and the infection of your device with malware. This can lead to identity theft, financial loss, and disruption to your daily activities.
What can public charging station operators do to prevent juice jacking attacks?
Operators should implement robust security measures, including physical security enhancements, software updates, and regular security audits. Using tamper-proof charging stations and implementing multi-factor authentication can significantly reduce the risk of these attacks.