Cybersecurity
-
Technology

How to Keep Your Smartphone Mobile Security Intact
How to keep your smart phones mobile security intact is crucial in today’s digital world. Protecting your phone isn’t just…
Read More » -
Technology

How to Elevate Your Mobile Security
How to elevate your mobile security? This guide dives deep into safeguarding your mobile devices, covering everything from understanding threats…
Read More » -
Cybersecurity
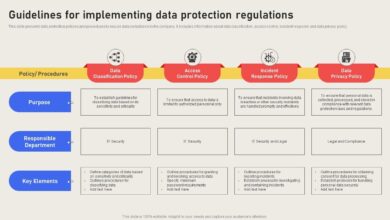
How to Draft an Effective Data Protection Strategy
How to draft an effective data protection strategy is crucial in today’s digital landscape. This comprehensive guide will walk you…
Read More » -
Cybersecurity
How to Defend Against Zero-Click Attacks
How to defend against zero click attacks – How to defend against zero-click attacks is crucial in today’s threat landscape.…
Read More » -
Cybersecurity

How to Defend Lean Security Teams
How to defend lean security teams against cyber threats is crucial in today’s digital landscape. Lean security teams, often operating…
Read More » -
Cybersecurity
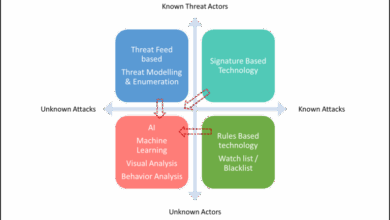
Connecting Dots Complex Threat Landscape
How to connect all the dots in a complex threat landscape is crucial for modern security. This exploration delves into…
Read More » -
Cybersecurity

How to Combat APT Cyber Threats A Comprehensive Guide
How to combat APT cyber threats a comprehensive guide sets the stage for a deep dive into the world of…
Read More » -
Business Management

How to Comply with FTC Safeguards Rule
How to comply with FTC safeguards rule is crucial for businesses handling sensitive data. This guide dives deep into understanding…
Read More » -
Cybersecurity

How to Become a CISO in 5 Steps
How to become a CISO in 5 steps: Ready to lead the charge in cybersecurity? This guide breaks down the…
Read More » -
Data Security
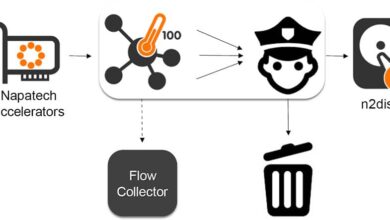
How to Achieve Maximum Security in Virtualized Data Centers
How to achieve maximum security in virtualized data centers is a critical concern for organizations today. Virtualization offers agility and…
Read More »
