Cybersecurity
-
Technology

IoT Worm Threatens City Smart Lights
An IoT worm could hack all smart lights in a city, potentially crippling vital infrastructure. This poses a significant threat…
Read More » -
Cybersecurity

IP Cameras IoTs Cyber Attack Hotspots
IP cameras among IoT devices are most vulnerable to cyber attacks. The Internet of Things (IoT) is rapidly changing our…
Read More » -
Data Security

IOC Indane Leak 6.7M Aadhaar Details Exposed
Ioc indane leaks aadhaar details of 6 7 million indian citizens – IOC Indane leaks Aadhaar details of 6.7 million…
Read More » -
Cybersecurity

Investigating the Top 10 Application Vulnerabilities
Investigating the top 10 application vulnerabilities is crucial in today’s digital landscape. These weaknesses represent potential entry points for malicious…
Read More » -
Technology

New Zealand Internet Outage DDoS Attack Impact
Internet in New Zealand disrupted due to a DDoS cyber attack. This crippling blow to New Zealand’s digital infrastructure highlights…
Read More » -
Technology

Criminals Spy on You Connected Home Devices
Internet connected household electronics are helping criminals spy on you. From smart thermostats to security cameras, our homes are increasingly…
Read More » -
Cybersecurity
Intel Zombieload Hacker Target
Intel Zombieload vulnerability might expose sensitive data like passwords to hackers. This sophisticated attack leverages a previously unknown flaw in…
Read More » -
Technology

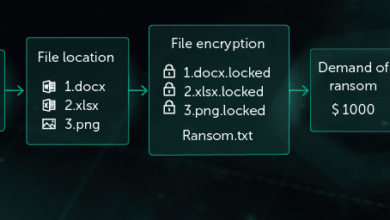
Intel Processors Recognizing Ransomware at Hardware Level
Intel processors to recognize ransomware attacks at hardware level sets the stage for a fascinating new approach to cybersecurity. This…
Read More » -
Cybersecurity
Intel & Check Point Ransomware Defense Partnership
Intel and Check Point software extend partnership for ransomware protection, forging a powerful alliance to combat the escalating threat of…
Read More » -
Risk Management

Lightspeed Remediation Integrated Risk Prioritization
Integrated risk prioritization for lightspeed remediation is crucial for navigating the complexities of fast-paced risk mitigation. This approach allows organizations…
Read More »
