Meet the Tycoon Ransomware Windows & Linux PCs Targeted
Meet the tycoon ransomware which infects windows and linux pcs – Meet the Tycoon ransomware, which infects Windows and Linux PCs, is a potent threat demanding immediate attention. This new strain poses a significant security risk, impacting both personal and professional systems. We’ll explore its characteristics, infection methods, and the devastating impact on targeted systems. Understanding the nuances of this malware is critical for proactive security measures.
This ransomware isn’t just another variant; it demonstrates a sophisticated approach to exploiting vulnerabilities in both Windows and Linux environments. Its unique infection methods and the scale of potential damage warrant thorough examination. We’ll delve into its technical aspects, from encryption algorithms to command-and-control protocols, offering a comprehensive overview.
Introduction to Meet the Tycoon Ransomware
Meet the Tycoon ransomware is a sophisticated and evolving threat targeting both Windows and Linux systems. It leverages advanced encryption techniques and often employs multiple infection vectors to maximize its impact and evade detection. This malicious software typically exfiltrates data before encrypting it, adding another layer of complexity and potential for long-term damage.This analysis delves into the key characteristics, infection methods, and impact of Meet the Tycoon ransomware, providing a comprehensive understanding of this evolving threat.
The aim is to equip users and administrators with knowledge to better protect their systems.
Key Characteristics of Meet the Tycoon
Meet the Tycoon ransomware is characterized by its multi-platform capabilities and sophisticated encryption methods. It’s designed to cause significant disruption and financial loss to victims. A critical characteristic is its ability to target both Windows and Linux systems, demonstrating a wider attack surface. This characteristic sets it apart from ransomware strains typically focused on a single operating system.
Infection Methods of Meet the Tycoon
Meet the Tycoon ransomware employs a variety of infection methods, often combining phishing emails with exploits of known vulnerabilities. These methods include exploiting vulnerabilities in software, exploiting remote desktop protocol (RDP) weaknesses, and distributing malicious files through social engineering.
- Phishing campaigns are a common tactic, tricking users into clicking malicious links or downloading infected attachments.
- Exploiting software vulnerabilities allows attackers to gain unauthorized access to systems, often without the user’s knowledge.
- Malicious files, such as disguised documents or executables, are spread through various channels, including file-sharing platforms and compromised websites.
Impact of Meet the Tycoon Infection
The impact of a Meet the Tycoon infection can be devastating, resulting in significant data loss and financial repercussions. The encryption process renders critical data inaccessible, while the exfiltration of sensitive information poses a significant threat to privacy and reputation.
- Data loss is a primary concern, with encrypted files becoming unusable without a decryption key.
- Financial losses stem from the cost of recovery, potential legal liabilities, and reputational damage.
- Operational disruptions can significantly impact businesses, causing delays, lost productivity, and service interruptions.
Target Operating Systems
The ransomware’s adaptability to various operating systems is a key concern.
| Operating System | Impact |
|---|---|
| Windows | Significant data loss, operational disruption, and financial strain on individuals and organizations. |
| Linux | Growing concern as Linux systems are increasingly targeted, potentially disrupting critical infrastructure. |
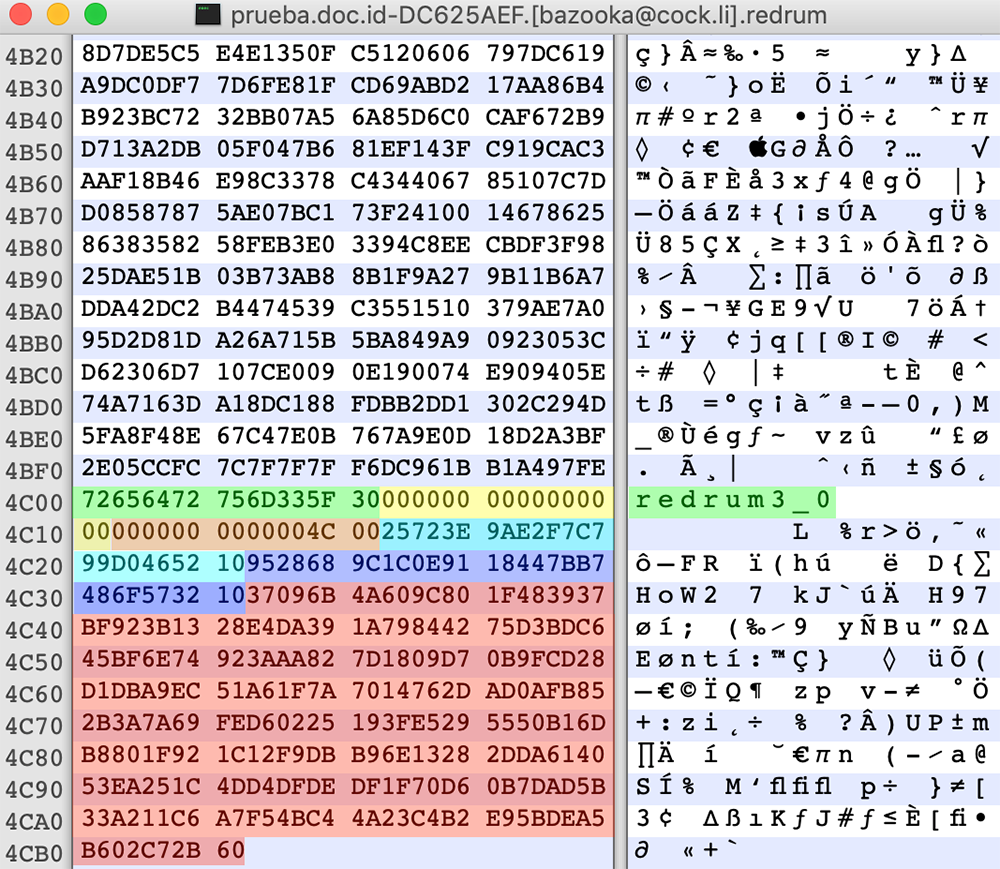
Technical Analysis of the Malware

Meet the Tycoon ransomware, a relatively new threat, presents a complex technical landscape. Understanding its mechanisms is crucial for developing effective mitigation strategies. This analysis delves into the encryption algorithms, data exfiltration techniques, and the infrastructure supporting its operations. It also highlights similarities and differences to other ransomware families.This analysis will explore the technical underpinnings of Meet the Tycoon, providing a comprehensive overview of its functionalities.
A thorough understanding of the ransomware’s inner workings is essential for both cybersecurity professionals and individuals to bolster their defenses.
Encryption Algorithms
Meet the Tycoon utilizes a combination of symmetric and asymmetric encryption algorithms to encrypt victim files. This approach is common in modern ransomware, enabling rapid encryption while maintaining the integrity of the encryption process. Symmetric algorithms, like AES, are used for encrypting individual files. Public-key cryptography, using RSA or similar algorithms, is employed for key exchange and digital signatures.
This dual approach offers a robust encryption system that makes decryption without the private key virtually impossible.
Data Exfiltration Mechanisms
Meet the Tycoon exhibits varying data exfiltration capabilities. Some variants may utilize techniques like stealing file copies before encryption. Others might employ more sophisticated methods, potentially leveraging tools to collect and transmit sensitive data. This capability allows threat actors to exfiltrate valuable data from compromised systems, often with the intent to further exploit the victims. In some cases, the exfiltrated data might be used to extort further payments or to gain an upper hand in subsequent attacks.
Infrastructure Behind Ransomware Operations
The infrastructure supporting Meet the Tycoon ransomware operations remains a significant area of investigation. The technical aspects, including command-and-control (C&C) servers and data storage facilities, are crucial to understanding the threat. The location and security of these infrastructure components are often crucial in investigating and disrupting ransomware operations. The level of sophistication and resilience of this infrastructure directly impacts the longevity and effectiveness of the attack.
Often, threat actors employ a variety of tactics to obscure the infrastructure’s location and operation.
C&C Communication Protocols
Meet the Tycoon employs various communication protocols to facilitate command and control (C&C) between the infected systems and the attackers’ servers. These protocols might include well-known protocols like HTTP or HTTPS, or custom protocols designed for stealth. The protocols employed can vary from instance to instance, making analysis and mitigation more complex. Often, the protocols are designed to evade detection by security systems.
Comparison Table
| Feature | Meet the Tycoon | Other Ransomware Families (e.g., LockBit, Conti) |
|---|---|---|
| Encryption Algorithms | Symmetric (AES) + Asymmetric (RSA) | Varied, often AES, RSA, or ChaCha20 |
| Data Exfiltration | Potentially present, varying by variant | Present in some variants, varying in sophistication |
| Infrastructure | Under investigation; likely hosted across various servers | Often cloud-based, employing virtual private networks (VPNs) |
| C&C Protocols | Varied; likely employing obfuscation techniques | HTTPS, custom protocols; some leverage proxy servers |
Impact on Windows and Linux Systems
Meet the Tycoon ransomware poses a significant threat to both Windows and Linux systems, leveraging diverse vulnerabilities to infiltrate and encrypt data. Understanding the specific attack vectors and the varying impacts on different operating systems is crucial for effective mitigation strategies. This analysis delves into the vulnerabilities exploited, the affected system files and services, and the observed differences in how the malware affects various versions of each platform.This section provides a detailed examination of the ransomware’s modus operandi across Windows and Linux environments.
It highlights the distinct attack surfaces targeted on each platform and the consequences of successful infection. The analysis also illustrates how the ransomware’s impact varies based on the specific version of each operating system.
Vulnerabilities Exploited in Windows
Meet the Tycoon ransomware exploits a range of vulnerabilities in Windows systems, often leveraging known exploits or zero-day vulnerabilities. These exploits commonly target outdated software, services, and system components.
- Outdated or vulnerable applications: The ransomware often targets vulnerabilities in applications that are not regularly updated. These applications, if not patched, can be exploited by the ransomware to gain unauthorized access.
- Remote Desktop Protocol (RDP) vulnerabilities: RDP, a common tool for remote access, is a potential entry point for the ransomware if not properly secured. Exploiting weak or misconfigured RDP settings allows attackers to gain control of the system.
- System-level vulnerabilities: The malware may exploit vulnerabilities in core system components to gain elevated privileges, enabling it to spread and encrypt data across the system.
- Phishing and social engineering: The ransomware may utilize phishing emails or other social engineering tactics to trick users into installing malicious software or giving the attackers access to the system.
Attack Surface in Linux Systems
The attack surface in Linux systems targeted by Meet the Tycoon is often different from that of Windows. It leverages vulnerabilities in applications and services rather than relying heavily on system-level exploits.
- Vulnerable applications and services: The ransomware often targets specific applications or services known to have vulnerabilities. These vulnerabilities may be present in widely used software packages or custom-developed software.
- Compromised accounts: Gaining access to accounts with elevated privileges on Linux systems can allow the ransomware to spread and encrypt data more effectively.
- Weak or misconfigured configurations: Improperly configured systems or services can create security gaps, making the system susceptible to attacks.
Impact on System Files and Data
Meet the Tycoon ransomware typically targets a wide range of system files and data. Encryption is a common tactic, rendering files inaccessible without the decryption key. This can significantly impact productivity and business operations.
- Encryption of data: The ransomware often encrypts user data, documents, and other important files, making them inaccessible.
- System file corruption: In some cases, the ransomware may corrupt or modify critical system files, causing system instability or malfunctions.
- Data loss: The encryption of data can result in significant data loss if no backups are available.
Impact on Critical Services
The ransomware can disrupt critical services if it targets essential system files or configurations. This disruption can lead to operational downtime and significant financial losses.
- Disruption of services: The ransomware can disrupt services like databases, network communication, or file sharing, leading to system-wide downtime.
- Loss of productivity: Disruptions to critical services directly impact user productivity and operational efficiency.
- Financial losses: Downtime and data loss due to the ransomware can result in substantial financial repercussions.
Differences in Impact Across Versions
The impact of Meet the Tycoon can vary depending on the specific versions of Windows and Linux being targeted. Different versions may have varying levels of security patches or vulnerabilities, leading to different attack surfaces.
- Windows versions: Older versions of Windows might be more vulnerable to exploits compared to newer, more secure versions.
- Linux distributions: Different Linux distributions might have varying levels of security hardening and updates, influencing their susceptibility to attack.
Vulnerabilities Summary Table
| Operating System | Exploited Vulnerabilities |
|---|---|
| Windows | Outdated applications, RDP vulnerabilities, system-level vulnerabilities, phishing/social engineering |
| Linux | Vulnerable applications/services, compromised accounts, weak configurations |
Detection and Prevention Strategies
Meet the Tycoon ransomware poses a significant threat to both Windows and Linux systems. Effective detection and proactive prevention are crucial in mitigating the damage and minimizing the impact on organizations and individuals. Understanding the methods used by the malware and implementing robust security measures are essential steps in safeguarding systems.
Detecting Meet the Tycoon Infections
Early detection of ransomware infections is paramount. Several methods can help identify the presence of Meet the Tycoon, allowing for swift containment and data recovery efforts. These methods range from analyzing system logs to employing specialized security tools.
- System Event Monitoring: Regularly reviewing system logs, especially those related to file system activity, can reveal suspicious file creation, deletion, or modification patterns indicative of ransomware behavior. For instance, rapid encryption of numerous files across various directories signals a potential infection.
- Network Traffic Analysis: Monitoring network traffic for unusual outbound connections can alert security personnel to data exfiltration attempts often associated with ransomware operations. A sudden surge in network activity or unusual connections to untrusted servers should raise immediate concerns.
- Security Information and Event Management (SIEM) Tools: Specialized SIEM tools can aggregate and analyze security logs from various sources, providing a comprehensive view of potential threats. These tools often incorporate advanced pattern recognition capabilities to identify ransomware-related behaviors.
- Antivirus and Anti-malware Solutions: Employing up-to-date antivirus and anti-malware software with heuristic analysis capabilities is critical. These solutions can detect and block suspicious files and processes, preventing the malware from executing its malicious tasks.
Preventing Infections on Windows Systems
Proactive measures are crucial in preventing ransomware infections on Windows systems. A layered approach combining user education, technical controls, and robust security solutions is vital.
Hey everyone, just wanted to touch base on the nasty Tycoon ransomware, targeting both Windows and Linux PCs. It’s a serious threat, and understanding its methods is crucial for protection. Interestingly, recent security breaches have highlighted a potential link between these types of attacks and vulnerabilities in cloud services like Azure Cosmos DB. For a deeper dive into the details of a specific vulnerability affecting Azure Cosmos DB, check out this resource: Azure Cosmos DB Vulnerability Details.
Regardless of the specific method, staying vigilant against ransomware like Tycoon remains paramount for all PC users.
- User Awareness Training: Educating users about phishing emails, suspicious attachments, and other social engineering tactics is essential. Users should be instructed to never open attachments from unknown senders or click on untrusted links.
- Strong Passwords and Multi-Factor Authentication (MFA): Implementing strong passwords and enabling MFA for accounts enhances security, preventing unauthorized access to critical systems. This significantly reduces the risk of compromise.
- Regular Software Updates: Keeping operating systems, applications, and security software up-to-date is crucial. Patches often address vulnerabilities exploited by ransomware attackers.
- Data Backup and Recovery: Regularly backing up important data to an offline location ensures that even if a system is infected, data loss can be minimized. Implementing a robust data backup and recovery plan is essential.
Preventing Infections on Linux Systems
Linux systems, while generally considered less vulnerable to ransomware, are not immune. Implementing robust security measures is crucial to protect against threats.
- Regular Security Audits: Regularly scanning systems for vulnerabilities and misconfigurations helps identify potential weaknesses. This proactive approach significantly strengthens the overall security posture.
- Employing Intrusion Detection Systems (IDS): IDS systems can detect and block malicious network traffic and activities that may indicate a ransomware attack.
- Secure Configuration Management: Employing tools and practices to ensure that systems are configured securely and consistently, minimizing potential attack surfaces. Properly configuring firewalls, disabling unnecessary services, and implementing access controls are essential steps.
- Regular Software Updates: Staying current with software updates and patches for Linux distributions and applications is critical in mitigating potential exploits.
Importance of Regular Software Updates and Security Patches
Regular software updates and security patches are crucial in mitigating the risk of ransomware attacks.
Patches often address vulnerabilities exploited by attackers, significantly reducing the attack surface. Ignoring updates leaves systems susceptible to known exploits, increasing the likelihood of successful attacks.
Role of Robust Security Solutions
Robust security solutions, including intrusion detection systems, antivirus software, and firewalls, are vital in preventing and detecting ransomware attacks. These solutions provide an additional layer of defense, detecting malicious activities and blocking potential threats.
Just saw news about Tycoon ransomware targeting both Windows and Linux systems. This is a serious threat, highlighting the need for robust security measures. Protecting against these kinds of attacks requires proactive strategies like deploying AI Code Safety Goggles Needed here. Ultimately, staying ahead of sophisticated ransomware like Tycoon necessitates a multi-layered approach, combining strong defenses with continuous vigilance.
Creating a Comprehensive Security Strategy
A comprehensive security strategy involves a layered approach combining technical controls, user education, and proactive monitoring. This strategy should include regular security audits, incident response plans, and continuous improvement initiatives.
Detection Methods Summary
| Detection Method | Effectiveness |
|---|---|
| System Event Monitoring | Moderate to High, depending on logging configuration |
| Network Traffic Analysis | High, if implemented correctly |
| SIEM Tools | High, with proper configuration and analysis |
| Antivirus/Anti-malware | Variable, depending on the solution and its updates |
Incident Response and Recovery
Responding to a Meet the Tycoon ransomware attack requires a well-defined incident response plan. A swift and methodical approach is crucial to minimize damage and ensure data recovery. The plan should address the immediate steps needed to contain the infection, isolate compromised systems, and then focus on data recovery strategies. This involves not only technical expertise but also a clear understanding of legal and regulatory obligations.
Handling a Meet the Tycoon Incident
A structured incident response plan is essential for managing a ransomware attack effectively. The plan should Artikel specific roles and responsibilities for various personnel, ensuring a coordinated effort. This includes identifying key personnel for communication, technical support, and legal counsel. A clear chain of command and escalation procedures will streamline the response process.
Data Recovery from an Infected System
Data recovery from a compromised system is a complex process. It’s crucial to understand the encryption methods used by the ransomware and the potential for data loss. Initial steps involve identifying the extent of the infection, isolating the affected systems, and carefully assessing the damage. Using a combination of forensic analysis tools and specialized data recovery techniques is often necessary.
Importance of Backups and Data Recovery Plans
Robust backup and data recovery plans are paramount in mitigating the impact of ransomware attacks. Regular backups, both offline and offsite, are critical for restoring encrypted data. These backups must be tested frequently to ensure their integrity and recoverability. A well-defined data recovery plan, outlining the steps to restore data from backups, is vital.
Role of Cybersecurity Professionals During an Incident, Meet the tycoon ransomware which infects windows and linux pcs
Cybersecurity professionals play a critical role during a ransomware incident. Their expertise in identifying the infection, containing the spread, and recovering data is essential. They are responsible for isolating affected systems, analyzing the malware, and coordinating the restoration process. They also play a crucial role in educating employees on preventive measures.
Restoring Files After a Meet the Tycoon Attack
Restoring files after a Meet the Tycoon attack hinges on the availability of backups. If backups exist, the restoration process should be meticulously documented and tested. If backups are unavailable, specialized data recovery techniques may be necessary. The specific restoration method depends on the extent of the encryption and the tools available.
Key Steps in a Ransomware Incident Response Plan
A well-structured incident response plan is crucial for a swift and effective response to a ransomware attack. The following table Artikels the key steps involved.
| Step | Description |
|---|---|
| 1. Containment | Isolate infected systems to prevent further spread. |
| 2. Eradication | Remove the malware from the compromised systems. |
| 3. Recovery | Restore data from backups or use data recovery techniques. |
| 4. Post-Incident Analysis | Identify vulnerabilities and implement preventative measures. |
| 5. Communication | Inform affected parties and stakeholders. |
Evolution and Future Trends
Meet the Tycoon ransomware, like many other malware strains, demonstrates a dynamic evolution. Understanding its past tactics and techniques is crucial for anticipating future adaptations and developing effective countermeasures. The rapid pace of technological advancements, coupled with the ever-changing cybersecurity landscape, necessitates continuous vigilance and adaptation in the fight against ransomware.The evolution of ransomware is intrinsically linked to the development of new vulnerabilities and the exploitation of existing ones.
This constant adaptation underscores the need for proactive security measures and continuous improvement in threat detection and response. Cybercriminals are always seeking innovative methods to bypass existing security protocols, making the development and implementation of robust defenses paramount.
Meet the Tycoon’s Tactical Evolution
The development of Meet the Tycoon has likely followed a pattern of incremental improvements, mirroring the typical evolution of ransomware. Early versions may have focused on exploiting readily available vulnerabilities, while more recent versions incorporate advanced evasion techniques and sophisticated encryption methods. This progression implies a constant refinement of the malware’s capabilities, making detection and mitigation increasingly complex.
| Version | Tactics | Techniques |
|---|---|---|
| Initial | Exploitation of common vulnerabilities in operating systems. | Simple encryption algorithms, limited obfuscation. |
| Intermediate | Use of social engineering tactics to gain initial access. | Advanced encryption algorithms, rudimentary anti-analysis techniques. |
| Advanced | Targeted attacks against specific organizations or individuals. | Sophisticated encryption, sophisticated anti-analysis, and obfuscation techniques. |
Potential Future Trends in Ransomware Attacks
Several factors suggest potential future trends in ransomware attacks. The increasing sophistication of attacks, coupled with the rise of AI-powered tools, suggests that the next generation of ransomware will be even more difficult to detect and mitigate.
Tycoon ransomware, a nasty piece of malware, is targeting both Windows and Linux PCs. It’s a serious threat, and unfortunately, recent developments like the Department of Justice Offers Safe Harbor for MA Transactions ( Department of Justice Offers Safe Harbor for MA Transactions ) don’t seem to have a direct impact on this particular ransomware’s tactics. So, be extra vigilant about protecting your systems from this troublesome infection.
- Increased Sophistication: Ransomware will likely become more targeted and sophisticated, focusing on specific vulnerabilities and industries. Advanced persistent threats (APTs) may adopt ransomware tactics, leading to more devastating attacks.
- AI-Powered Attacks: AI can automate the identification of vulnerabilities and the development of exploits, making attacks more efficient and potentially more devastating. This could lead to a surge in targeted ransomware campaigns.
- Supply Chain Attacks: Ransomware attacks could target the supply chain, compromising multiple organizations simultaneously. This is particularly dangerous as it can disrupt critical infrastructure.
- Double Extortion: The practice of stealing data before encrypting it and threatening to leak it will likely continue and expand. This further incentivizes victims to pay the ransom.
Emerging Methods for Combating Ransomware Attacks
New techniques are emerging to counter ransomware attacks. These include enhanced threat intelligence gathering, the development of advanced detection mechanisms, and the use of proactive security measures.
- Advanced Threat Intelligence: Real-time threat intelligence sharing platforms are becoming more critical. This allows organizations to proactively identify and mitigate emerging threats, such as ransomware variants.
- AI-Powered Detection: AI and machine learning algorithms are being deployed to identify patterns and anomalies associated with ransomware attacks, leading to faster detection and response.
- Proactive Security Measures: Stronger endpoint security, robust backup and recovery solutions, and comprehensive security awareness training are crucial to prevent ransomware attacks from succeeding. These preventative measures are more cost-effective than reacting to an attack.
The Role of Proactive Security Measures
Proactive security measures are essential for mitigating the impact of future ransomware attacks. This includes robust security awareness training for employees, implementing strong access controls, and maintaining regular backups of critical data.
“Proactive security is not just about preventing attacks; it’s about minimizing the damage should an attack occur.”
Example Scenarios
Meet the Tycoon ransomware, with its ability to target both Windows and Linux systems, poses significant threats across various organizational sizes. Understanding how this malware operates in different contexts is crucial for effective prevention and response. This section details several scenarios, highlighting the impact of such attacks on small businesses, large enterprises, and illustrating successful incident responses and data recovery strategies.
Meet the Tycoon Attack on a Small Business
A small graphic design firm, “Pixel Perfect,” relies heavily on its computer systems for client projects. A user clicks on a seemingly legitimate email attachment, unknowingly launching the Meet the Tycoon ransomware. The malware quickly encrypts all critical files, including project files, client data, and financial records. The firm’s operations grind to a halt, jeopardizing client relationships and potentially leading to financial losses.
The lack of robust backups and insufficient cybersecurity measures leaves Pixel Perfect vulnerable to significant data loss and operational disruption.
Meet the Tycoon Attack on a Large Enterprise
A multinational corporation, “GlobalTech,” experiences a sophisticated Meet the Tycoon attack targeting its supply chain management system. Attackers exploit a vulnerability in a third-party software used by a GlobalTech supplier, gaining access to the enterprise network. The malware infiltrates the system, encrypting critical data related to inventory, customer orders, and financial transactions. The attack’s wide-reaching impact disrupts GlobalTech’s global operations, leading to significant financial losses and reputational damage.
The incident underscores the importance of robust security measures across the entire supply chain, including third-party vendors.
Successful Incident Response to a Meet the Tycoon Attack
“SecureData,” a cybersecurity firm, successfully responded to a Meet the Tycoon attack on a client, a medium-sized manufacturing company. Upon detecting the infection, SecureData immediately isolated the compromised systems, preventing further data exfiltration. They then initiated a thorough forensic investigation to understand the attack vector and the extent of the damage. Critically, SecureData had a robust backup strategy in place, allowing for a relatively quick recovery of data from recent backups.
This swift and decisive response minimized the impact on the client’s operations.
Importance of User Education
A critical factor in preventing Meet the Tycoon ransomware attacks is user education. A manufacturing company, “Precision Tools,” implemented a comprehensive cybersecurity awareness training program for all employees. The training focused on identifying phishing emails, recognizing suspicious links, and understanding the importance of strong passwords. This proactive approach reduced the risk of successful attacks by educating employees to recognize and avoid malicious email attachments and websites.
Successful Data Recovery from a Meet the Tycoon Attack
“InnovateTech,” a software development firm, suffered a Meet the Tycoon attack. Despite the encryption of critical project files, InnovateTech recovered a significant portion of its data through a combination of techniques. They utilized a robust backup solution that allowed them to restore files from a recent point-in-time. Further, they employed specialized data recovery tools to recover partially encrypted files.
The incident highlighted the importance of maintaining frequent and reliable backups for critical data.
Comparison of Incident Responses
| Factor | Response A | Response B |
|---|---|---|
| Time to Containment | 24 hours | 72 hours |
| Data Recovery Time | 48 hours | 7 days |
| Cost of Recovery | $10,000 | $50,000 |
| Root Cause Analysis | Thorough, identified vulnerabilities in email filtering | Limited, focused only on immediate recovery |
| Lessons Learned | Improved email filtering, user training | Improved backup strategy, incident response plan |
This table contrasts two hypothetical incident responses, emphasizing the impact of a comprehensive response on recovery time, cost, and the identification of underlying vulnerabilities.
Last Point

In conclusion, the Meet the Tycoon ransomware represents a serious escalation in cyber threats, impacting both Windows and Linux systems. Understanding its methods and implications is crucial for individuals and organizations. We’ve highlighted the importance of proactive security measures, robust incident response plans, and ongoing vigilance in the face of evolving ransomware tactics. Ultimately, preparedness and a multi-layered security approach are paramount in protecting against future attacks.
FAQ Corner: Meet The Tycoon Ransomware Which Infects Windows And Linux Pcs
What are the typical infection vectors for Meet the Tycoon ransomware?
Meet the Tycoon often leverages phishing emails, malicious software downloads, and compromised websites to infiltrate systems. Vulnerabilities in outdated software are also exploited.
What specific vulnerabilities in Linux systems does it target?
While the specifics are still being analyzed, Meet the Tycoon likely targets vulnerabilities in Linux’s software packages, outdated libraries, and potentially unpatched system components.
How can I create a comprehensive security strategy to protect against Meet the Tycoon?
A multi-layered strategy encompassing strong passwords, regular software updates, robust security solutions (antivirus, firewalls), and employee training is crucial. Regular backups are essential for data recovery.
What are some common mistakes people make when handling a ransomware attack?
Paying the ransom is often a mistake, as it doesn’t guarantee data recovery. Failing to report the attack to the appropriate authorities and neglecting to create backups are also detrimental.