DevSecOps
-
Cybersecurity

Embracing Advanced Frameworks for Vulnerability Management
Embracing advanced frameworks for effective vulnerability management sets the stage for a robust and proactive security approach. This involves more…
Read More » -
Cybersecurity

Future-Proofing Vulnerability Management
How to prepare for the future of vulnerability management is crucial in today’s rapidly evolving threat landscape. Cybersecurity threats are…
Read More » -
Cybersecurity

Continuous Security Testing Strengthening Your Cybersecurity
Continuous security testing is the key to strengthening your cybersecurity. In today’s rapidly evolving threat landscape, relying on outdated, reactive…
Read More » -
IT Security

Businesses Shift Toward Compliance as Code
Businesses shift toward compliance as code – it sounds like a techy buzzword, right? But it’s actually a game-changer for…
Read More » -
Security

Breaking the Cycle of Traditional Vulnerability Management
Breaking the cycle of traditional vulnerability management isn’t just about patching holes; it’s about fundamentally changing how we think about…
Read More » -
Cybersecurity
Automating the API Security Lifecycle An Interview with Subbu Iyer
Automating the api security lifecycle an interview with subbu iyer of cequence security – Automating the API Security Lifecycle: An…
Read More » -
Software Development

7 Steps to Secure Design Patterns A Robust Software Security Foundation
7 Steps to implement secure design patterns a robust foundation for software security – that’s what we’re diving into today!…
Read More » -
Cybersecurity
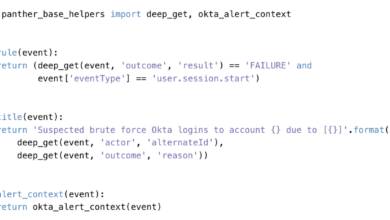
5 Benefits of Detection as Code
5 Benefits of Detection as Code: Ever felt like your security systems are playing catch-up with the ever-evolving threat landscape?…
Read More » -
Cybersecurity

The 5Ws of Software Supply Chain Security
The 5ws of the software supply chain how security teams can prevent costly mistakes – The 5Ws of the software…
Read More » -
Cybersecurity

Traditional Network Scannings Limits & Software Risk Underestimation
The limitations of traditional network based vulnerability scanning and the systematic underestimation of software risks – Traditional Network Scanning’s Limits…
Read More »
