Incident Response
-
Cybersecurity

Managed Security Operations Center (SOC) Explained
Managed security operations center soc explained – Managed security operations center (SOC) explained delves into the world of centralized security…
Read More » -
Cybersecurity

NIST Update 3 Reasons for Threat Hunting
3 reasons the next NIST update should include threat hunting: The cybersecurity landscape is constantly evolving, becoming more complex and…
Read More » -
Cybersecurity

5 Types of Threat Hunting A Deep Dive
5 types of threat hunting are crucial in today’s cybersecurity landscape. This exploration dives deep into the five distinct approaches,…
Read More » -
Business Security

10 Ways to Ensure Employee Security
10 ways to ensure your employees practice excellent security. This comprehensive guide covers crucial aspects of employee security, from training…
Read More » -
Cybersecurity
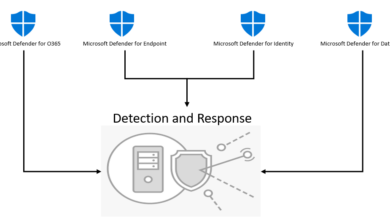
XDR Cybersecurity Infrastructures Foundation
Is extended detection and response xdr the ultimate foundation of cybersecurity infrastructure – Is extended detection and response (XDR) the…
Read More » -
Risk Management

Lightspeed Remediation Integrated Risk Prioritization
Integrated risk prioritization for lightspeed remediation is crucial for navigating the complexities of fast-paced risk mitigation. This approach allows organizations…
Read More » -
Cybersecurity

Insider Threats Detect, Remediate, Prevent Attacks – Live Webinar
Insider threats detect remediate prevent insider attacks live webinar. This webinar dives deep into the insidious world of insider threats,…
Read More » -
Cybersecurity

Insider Threat Alert Data Theft by Exiting Employees
Insider threat alert as employees take data while leaving a job is a growing concern for businesses. This issue highlights…
Read More » -
Cybersecurity

Insider Threat and Mitigation Best Practices
Insider threat and mitigation best practices are crucial for organizations to protect sensitive data and systems. Understanding the different types…
Read More » -
Cybersecurity

How to Track Ransomware Attacks A Guide
How to track ransomware attacks a comprehensive guide sets the stage for this detailed exploration of a critical cybersecurity concern.…
Read More »
