Incident Response
-
Cybersecurity

How to Survive a Ransomware Attack A Comprehensive Guide
How to survive a ransomware attack is a critical question for businesses and individuals alike. This guide dives deep into…
Read More » -
Cybersecurity

Negotiating Ransomware Attacks A Guide
How to negotiate ransomware attacks a strategic guide sets the stage for understanding the complex world of ransomware. This guide…
Read More » -
Cybersecurity

How to Make Threat Intelligence Practical
How to make threat intelligence practical for your organization is crucial in today’s complex digital landscape. This guide dives deep…
Read More » -
Cybersecurity

How to Defend Lean Security Teams
How to defend lean security teams against cyber threats is crucial in today’s digital landscape. Lean security teams, often operating…
Read More » -
Cybersecurity
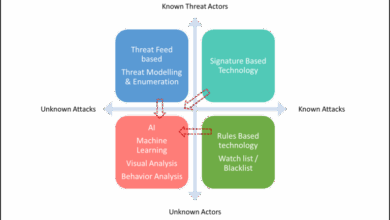
Connecting Dots Complex Threat Landscape
How to connect all the dots in a complex threat landscape is crucial for modern security. This exploration delves into…
Read More » -
Cybersecurity
Getting Ahead of the Attack
Getting ahead of the attack isn’t just about reacting to threats; it’s about proactively building a fortress around your digital…
Read More » -
Cybersecurity

Early Detection The Key to Tackling Security Breaches
Early detection is the key to tackling security breaches. We live in a hyper-connected world, where a single vulnerability can…
Read More » -
Cybersecurity

Does XDR Need a New Kill Chain?
Does XDR need a new kill chain? That’s the burning question we’re tackling today. The evolution of cyberattacks has outpaced…
Read More » -
Cybersecurity
Deception Breaches Seeding the Hunt Offensively
Deception breaches and going on the offense to seed the hunt – it sounds like a spy thriller, doesn’t it?…
Read More » -
IT Security

Creating a Culture of Cybersecurity 2 A Deeper Dive
Creating a Culture of Cybersecurity 2 isn’t just about installing software; it’s about fundamentally shifting how your organization thinks about…
Read More »
