Israel Warns AI Cyber Attacks
Israel issues warning on AI cyber attacks, signaling a growing concern about the potential for sophisticated and devastating digital assaults. This warning highlights the escalating threat posed by artificial intelligence in the cyber realm, emphasizing the need for proactive measures and international cooperation to combat this emerging danger. Israel’s historical focus on cybersecurity, coupled with its technological prowess, places it at the forefront of this discussion, raising questions about the future of digital warfare and the vulnerabilities of critical infrastructure.
The warning details various types of AI-powered attacks, from sophisticated phishing campaigns to the potential for autonomous weapons systems. Israel’s assessment suggests a concerning evolution in cyber threats, with the potential for targeting critical infrastructure and causing significant economic and societal damage. This article delves into the specific types of attacks, their potential impacts, and the proposed countermeasures.
Background of Israeli AI Cyber Threat Warnings
Israel has consistently demonstrated a proactive and forward-thinking approach to emerging cyber threats, including those leveraging artificial intelligence. This proactive stance is rooted in a deep understanding of the nation’s strategic vulnerabilities and a recognition of the potential for AI to be weaponized. The country’s unique geopolitical position and history of conflict have fostered a culture of vigilance and preparedness in the cybersecurity sphere.Israel’s cyber security strategies have evolved significantly, incorporating AI at multiple levels.
Initially focused on traditional defensive measures, the nation’s approach has shifted to include proactive threat detection and response systems powered by AI. This evolution is driven by the understanding that traditional security measures alone may not be sufficient to counter sophisticated, AI-driven attacks.
Historical Overview of Israel’s Approach to AI-related Cyber Threats
Israel’s approach to AI-related cyber threats is deeply intertwined with its overall national security strategy. Recognizing the potential for AI to be used in sophisticated cyberattacks, the country has invested heavily in research and development of AI-powered security solutions. This investment is complemented by a strong focus on international collaboration and knowledge sharing. The nation has been a key player in developing and deploying advanced cyber security technologies for both its own protection and the protection of its allies.
Evolution of Israeli Cyber Security Strategies, Emphasizing the Role of AI
The evolution of Israeli cyber security strategies reflects a gradual but significant shift towards AI-driven solutions. Initial strategies emphasized traditional methods, such as intrusion detection systems and network security. However, as AI capabilities matured, Israel adapted its strategies to incorporate AI-powered threat analysis, predictive modeling, and automated response mechanisms. This evolution is crucial in addressing the escalating sophistication of cyberattacks.
Examples of Past Instances Where Israel Warned About AI-Driven Cyberattacks
Public pronouncements by Israeli security officials, though often veiled in strategic ambiguity, have hinted at specific instances where AI-powered cyberattacks were identified as a growing concern. These instances typically involve warnings about the potential for AI-enhanced phishing campaigns, automated denial-of-service attacks, and sophisticated malware development.
Perceived Severity of AI-Driven Cyber Threats by Israel
Israel perceives AI-driven cyber threats as a significant and evolving challenge to national security. The country recognizes that the potential for AI to be used in malicious ways is not limited to traditional cyberattacks. The potential for AI-powered attacks to disrupt critical infrastructure and cause widespread societal damage is a significant concern. This perception underscores the urgent need for proactive measures to mitigate these risks.
Potential Motivations Behind Israeli Warnings, Israel issues warning on ai cyber attacks
Several motivations lie behind Israel’s warnings regarding AI-driven cyber threats. These include a desire to highlight the growing threat landscape, to encourage international collaboration on countermeasures, and to bolster domestic investment in AI-powered cybersecurity solutions. The warnings also serve to position Israel as a leader in this critical area.
Comparison of Israel’s Approach to Other Countries’ Approaches
| Feature | Israel | United States | China |
|---|---|---|---|
| Focus | Proactive threat detection and response, strong international collaboration | Focus on defensive measures, proactive incident response | Focus on AI development, potential use in offensive operations |
| Investment | High investment in AI-powered cybersecurity R&D | Significant investment in cybersecurity infrastructure | Large-scale investment in AI development, including military applications |
| International Cooperation | Strong emphasis on international collaboration and information sharing | Active participation in international cybersecurity initiatives | Limited transparency in cybersecurity cooperation |
Types of AI Cyber Threats Israel Has Highlighted
- Sophisticated Phishing Campaigns: AI can be used to create highly personalized and convincing phishing emails, increasing the likelihood of successful attacks. Examples include using machine learning to analyze user data and tailor emails to individual preferences, increasing the chances of users clicking on malicious links or downloading harmful attachments.
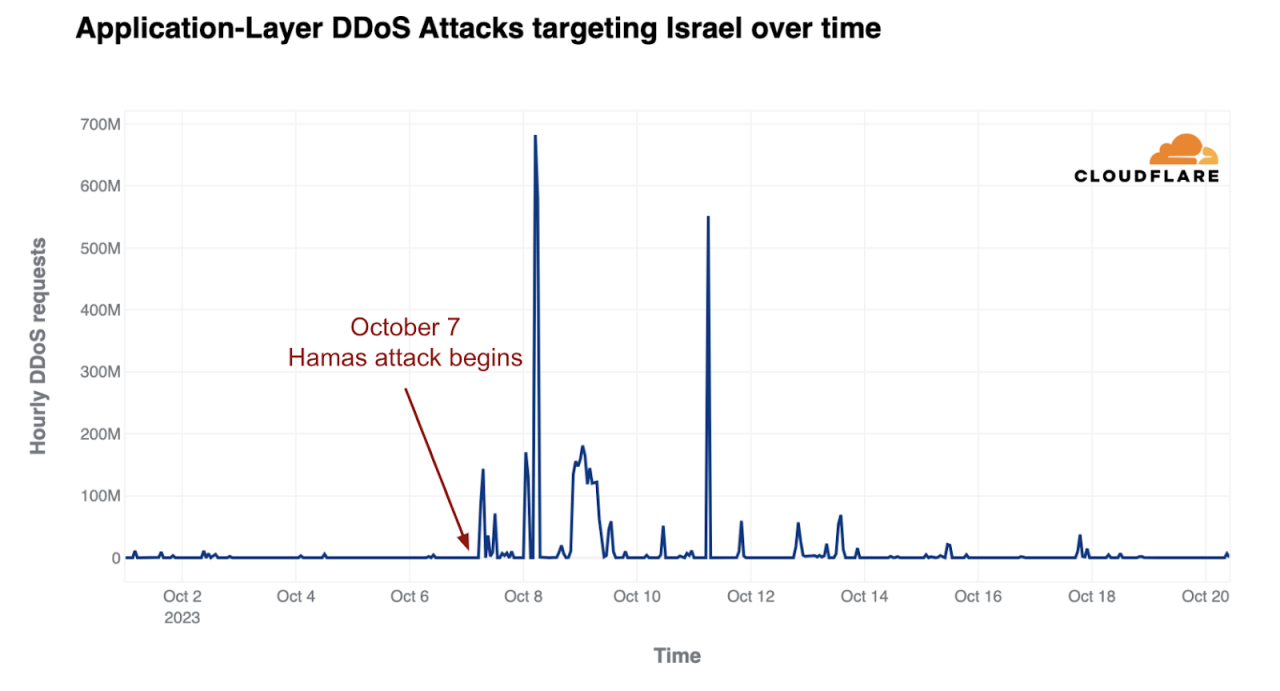
- Automated Denial-of-Service Attacks: AI can be used to generate and execute denial-of-service attacks at an unprecedented scale and speed, disrupting online services and infrastructure. These attacks can be difficult to defend against due to their automated and dynamic nature.
- Advanced Malware Development: AI can automate the creation of new and sophisticated malware, making it harder for traditional security solutions to detect and block. Machine learning algorithms can be used to create malware that adapts to security measures, making it harder to detect and remove.
- AI-powered Targeted Attacks: AI can be used to identify and target specific individuals or organizations, allowing for more effective and efficient attacks. This targeting can involve analyzing social media profiles, public information, and other data to identify potential vulnerabilities and tailor attacks to specific individuals or groups.
Specific Types of AI Cyberattacks Warned About
Israel’s warnings regarding AI-powered cyberattacks highlight a rapidly evolving threat landscape. These attacks are not merely incremental improvements on existing methods; they represent a fundamental shift in the nature of digital warfare, demanding a proactive and adaptive defense strategy. The potential for widespread disruption and damage is significant, underscoring the urgent need for understanding these emerging threats.
Specific AI-Enabled Cyberattack Types
Israel’s warnings encompass a diverse range of AI-enabled cyberattacks, reflecting the multifaceted applications of artificial intelligence in the digital realm. These attacks go beyond traditional methods, leveraging AI’s capacity for automation, learning, and adaptation.
- Automated Network Attacks: AI can automate network scanning and penetration testing, allowing attackers to rapidly identify vulnerabilities and launch targeted attacks at an unprecedented scale. This automation significantly reduces the time and resources needed for attacks, making them more frequent and potentially devastating. For example, a network attack might use AI to rapidly generate and test thousands of exploits against a target system, effectively automating the process of identifying and exploiting vulnerabilities.
- AI-Powered Malware: Sophisticated malware can be developed using AI, enabling it to adapt and evade detection more effectively. This “adaptive malware” can modify its behavior in real-time, learning from the responses of security systems and changing its attack strategies. One such example is malware that learns the patterns of network traffic to avoid detection by intrusion detection systems, thus becoming harder to identify and eliminate.
- Deepfakes for Phishing: AI-generated deepfakes can be used to create highly realistic but fraudulent videos or audio recordings to trick individuals into divulging sensitive information. This technique, coupled with phishing attacks, can exploit human trust and bypass traditional security measures. The convincing nature of these deepfakes makes them extremely effective in social engineering attacks, where manipulating human behavior is the core strategy.
- Predictive Attack Strategies: AI algorithms can analyze vast amounts of data to predict potential vulnerabilities and target critical infrastructure. This allows attackers to proactively exploit weaknesses before they are patched, significantly increasing the chances of successful attacks. For example, AI could analyze data from social media and news reports to anticipate maintenance schedules at critical infrastructure facilities, thus planning attacks during periods of low security.
Potential Impact of AI Cyberattacks
AI-driven cyberattacks can disrupt a wide range of critical infrastructure, causing significant damage to economies and societies. The impact extends beyond simple data breaches, encompassing the potential to cripple essential services.
- Disruption of Critical Infrastructure: AI-powered attacks can target critical infrastructure such as power grids, water systems, and transportation networks, causing widespread disruption and potentially catastrophic consequences. A successful attack on a power grid, for example, could leave millions without electricity for extended periods, severely impacting essential services and daily life.
- Financial Losses: Financial institutions are particularly vulnerable to AI-powered attacks, potentially leading to massive financial losses due to fraudulent transactions, theft of sensitive data, and manipulation of financial markets. Such attacks could trigger cascading effects throughout the global financial system, leading to significant economic instability.
- National Security Concerns: AI-powered cyberattacks can be used to compromise national security systems, potentially leading to espionage, sabotage, or disruption of critical defense capabilities. The strategic implications of such attacks could be profound, potentially impacting national security and geopolitical stability.
Vulnerabilities Exploited by AI Cyberattacks
The sophistication of AI cyberattacks is directly linked to the vulnerabilities they exploit. These vulnerabilities range from software flaws to human error and lack of awareness.
- Software Vulnerabilities: AI-powered attacks can leverage vulnerabilities in software and hardware, exploiting known or unknown flaws to gain unauthorized access to systems. This underscores the need for constant software updates and security patches.
- Human Error and Weak Passwords: AI can be used to automate attacks on users, exploiting their vulnerabilities like weak passwords or phishing attempts. This emphasizes the importance of strong passwords and user awareness training.
- Lack of Security Awareness: AI-powered attacks can be designed to exploit human weaknesses, such as a lack of security awareness, leading to successful social engineering attacks. This emphasizes the importance of educating users about security threats and best practices.
Potential Targets of AI Cyberattacks
The potential targets of AI-powered cyberattacks are diverse and extend across various sectors. The potential impact of these attacks on different sectors is a critical consideration.
| Sector | Potential Targets |
|---|---|
| Finance | Banking systems, stock exchanges, financial institutions |
| Energy | Power grids, oil pipelines, gas facilities |
| Transportation | Traffic control systems, railway networks, air traffic control |
| Healthcare | Patient records, medical equipment, hospital networks |
Sophistication of AI Cyberattacks Over Time
The sophistication of AI cyberattacks has evolved significantly over time, reflecting the rapid advancement of AI technology itself. Initial attacks might have relied on basic AI techniques, but current attacks leverage advanced algorithms and machine learning capabilities.
Potential Impacts and Implications of the Warnings

Israel’s warnings about AI-powered cyberattacks highlight a critical turning point in the digital age. These warnings aren’t just theoretical; they represent a tangible threat to global stability, demanding proactive measures to mitigate potential devastation. The implications extend far beyond technical vulnerabilities, touching upon economic, social, and geopolitical spheres. Understanding these ramifications is crucial for navigating the complex future of AI.The potential ramifications of AI-powered cyberattacks are far-reaching and necessitate a comprehensive understanding of their diverse impacts.
These attacks aren’t limited to disrupting systems; they threaten the foundations of modern life, and require a proactive approach to mitigation.
Economic Consequences of AI Cyberattacks
AI-driven cyberattacks can cripple critical infrastructure, disrupting supply chains, and causing substantial economic losses. Consider a scenario where AI is used to target financial institutions, potentially causing widespread panic and impacting global markets. The financial sector’s dependence on interconnected systems makes it particularly vulnerable. Furthermore, targeted attacks on manufacturing or energy grids could result in prolonged outages and substantial economic damage, impacting productivity and growth.
Social Impacts of AI Cyberattacks
AI cyberattacks can erode public trust in technology and institutions. The potential for manipulating public opinion, spreading misinformation, and even creating social unrest is a significant concern. Examples of social media manipulation using AI are becoming increasingly prevalent, highlighting the vulnerability of democratic processes and social cohesion.
Geopolitical Implications of AI Cyberattacks
The use of AI in cyber warfare can escalate geopolitical tensions, potentially leading to international conflicts. States might view AI-powered cyberattacks as an asymmetric warfare tool, blurring the lines between traditional and non-traditional threats. This could lead to a dangerous escalation in global tensions.
Effects on International Relations
The potential for AI cyberattacks to be used as instruments of national policy can severely strain international relations. A lack of clear international norms and regulations regarding the use of AI in warfare can lead to mistrust and an arms race, escalating global insecurity.
Effect on Global AI Development
The warnings about AI cyberattacks could stifle innovation and development. Fear of misuse and the need for stringent security measures could lead to a slowdown in the development and adoption of AI technologies. This is a delicate balance; innovation must be encouraged while simultaneously addressing security concerns.
Potential for AI Arms Races
The threat of AI cyberattacks could trigger a new arms race. Nations may invest heavily in developing AI-powered offensive and defensive cyber capabilities, increasing the risk of a catastrophic conflict.
Potential Solutions to Mitigate AI Cyberattack Risks
International cooperation and collaboration are crucial in addressing the challenge of AI cyberattacks. A shared understanding of the risks and a concerted effort to establish global norms and regulations are essential.
| Category | Potential Solutions |
|---|---|
| International Cooperation | Establish international agreements on AI security, promote shared threat intelligence, and coordinate responses to attacks. |
| Defensive Measures | Strengthen cybersecurity infrastructure, develop robust AI detection systems, and invest in proactive security measures. |
| Offensive Measures | Develop AI-powered tools for threat hunting and intelligence gathering. |
| Ethical Frameworks | Establish ethical guidelines and regulations for AI development and deployment, emphasizing responsible AI use. |
| Education and Awareness | Raise public awareness about the risks of AI cyberattacks, and train professionals in AI security. |
Possible Responses and Countermeasures
Israel’s warnings underscore the urgent need for proactive and comprehensive strategies to combat AI-powered cyberattacks. These threats are not confined to national borders; they demand a global response involving governments, the private sector, and international organizations. Effective countermeasures require a multi-faceted approach, encompassing technological advancements, robust regulations, and a commitment to international cooperation.The sophistication of AI-driven cyberattacks necessitates a shift from reactive measures to proactive defenses.
Israel’s recent warning about AI-powered cyberattacks highlights a growing concern. Protecting digital infrastructure is crucial, and the Department of Justice Offers Safe Harbor for MA Transactions, a new policy designed to streamline certain legal processes, could potentially mitigate some of the risks. This new approach, however, doesn’t fully address the complex challenges posed by sophisticated AI-driven cyberattacks.
A focus on strengthening cybersecurity infrastructure and fostering a culture of cybersecurity awareness within organizations and individuals is crucial. This proactive approach is essential for mitigating the potential damage and disruption caused by these attacks.
Potential Countermeasures to AI Cyberattacks
Developing robust defenses against AI-powered cyberattacks requires a multi-layered approach. This includes implementing advanced threat detection systems, enhancing incident response capabilities, and bolstering the resilience of critical infrastructure. Crucially, these measures must be adaptable to the evolving nature of AI-driven threats. Constant monitoring and adaptation are paramount.
- Advanced Threat Detection Systems: Implementing advanced machine learning algorithms to identify and analyze patterns indicative of malicious AI activity is essential. These systems should be capable of distinguishing between legitimate and malicious AI use cases. Regular updates and continuous improvement are vital to maintain effectiveness.
- Enhanced Incident Response Capabilities: Establishing and refining incident response plans that are tailored to AI-specific attacks is critical. This includes protocols for identifying, containing, and recovering from attacks involving AI tools. Rapid and effective response minimizes damage.
- Strengthening Cybersecurity Infrastructure: Securing critical infrastructure from AI-driven attacks requires a multifaceted approach. This includes employing robust encryption protocols, multi-factor authentication, and regular security audits. Regular vulnerability assessments are necessary to address emerging weaknesses.
Importance of International Cooperation
Addressing the transnational nature of AI cyber threats necessitates strong international cooperation. This includes sharing best practices, developing common standards, and establishing mechanisms for international collaboration in responding to attacks. Harmonizing cybersecurity policies across nations is critical.
Israel’s recent warning about AI-powered cyberattacks highlights a growing concern. These attacks aren’t just theoretical; vulnerabilities in systems like Microsoft Azure Cosmos DB, as detailed in Azure Cosmos DB Vulnerability Details , demonstrate the real-world risks. While this particular vulnerability might not be directly related to the AI-driven threats, it emphasizes the critical need for robust security measures across the board to combat the evolving landscape of cyber warfare.
Israel’s warning serves as a potent reminder of the ongoing challenges.
- Information Sharing: Establishing secure channels for sharing information about emerging threats and vulnerabilities across borders. This will allow for early warnings and coordinated responses.
- Joint Research and Development: Collaborating on research and development of new technologies and strategies for combating AI-driven cyberattacks. This can lead to breakthroughs in defense mechanisms.
- International Legal Frameworks: Creating international legal frameworks that address the use of AI in cyberattacks. Establishing clear guidelines and norms of behavior in cyberspace is crucial.
Role of Government Agencies in Responding to AI Cyberattacks
Government agencies play a critical role in developing and implementing national strategies for AI cybersecurity. This involves establishing regulatory frameworks, funding research and development, and coordinating responses to attacks.
- Regulatory Frameworks: Developing and enforcing regulations that address the ethical and security implications of AI development and deployment. This will ensure that AI systems are developed and used responsibly.
- Funding for Research and Development: Providing financial support for research and development of new cybersecurity technologies and strategies that can counter AI-driven attacks. This fosters innovation in defense mechanisms.
- Coordination of Responses: Coordinating responses to AI-driven attacks across different government agencies. This ensures a unified and effective response.
Proactive Measures Countries Could Take
Proactive measures are crucial in anticipating and mitigating AI-driven cyberattacks. These include investing in cybersecurity education, promoting industry best practices, and developing robust national cybersecurity strategies.
- Investing in Cybersecurity Education: Integrating cybersecurity education into curricula at all levels, from primary school to higher education. Promoting awareness and skills in cybersecurity among the public is paramount.
- Promoting Industry Best Practices: Encouraging the adoption of best practices in cybersecurity within industries. This includes promoting the use of strong passwords, regular security audits, and secure data storage practices.
- Developing Robust National Cybersecurity Strategies: Developing and implementing comprehensive national strategies that address the unique vulnerabilities of each country in the context of AI-driven cyberattacks.
Strategies to Combat AI Cyberattacks
| Strategy | Description | Example |
|---|---|---|
| Proactive Security Measures | Implementing security measures before an attack occurs. | Regular security audits, vulnerability assessments, and penetration testing. |
| Advanced Threat Detection | Using sophisticated tools to identify malicious AI activity. | Employing machine learning algorithms to detect anomalies in network traffic. |
| Incident Response Planning | Developing and testing plans for responding to AI-driven cyberattacks. | Establishing clear communication channels and roles for incident response teams. |
| International Collaboration | Sharing information and coordinating efforts with other countries. | Participating in international forums and exchanging best practices. |
Role of Private Sector Initiatives
Private sector initiatives play a vital role in bolstering AI cybersecurity. This includes investing in research and development, implementing robust security measures, and promoting cybersecurity awareness within organizations.
- Private Sector Research and Development: Investing in research and development of new cybersecurity technologies to counter AI-driven attacks. This can lead to innovative solutions.
- Robust Security Measures: Implementing strong security measures within organizations to protect against AI-driven cyberattacks. This includes multi-factor authentication and encryption protocols.
- Cybersecurity Awareness Programs: Implementing cybersecurity awareness programs to educate employees about the risks of AI-driven cyberattacks and best practices for protecting themselves and the organization.
Need for Robust Cybersecurity Education and Training Programs
Robust cybersecurity education and training programs are essential for building a workforce equipped to address AI-driven cyber threats. This includes training individuals in the latest techniques and tools for detecting and responding to AI-related cyberattacks.
- Training Programs for Professionals: Developing specialized training programs for cybersecurity professionals to equip them with the skills necessary to combat AI-driven attacks.
- Education for the Public: Raising public awareness about the risks of AI-driven cyberattacks and promoting best practices for online safety.
Illustrative Examples of AI Cyberattacks

The rapidly evolving landscape of artificial intelligence (AI) presents novel challenges in cybersecurity. AI-powered attacks, though not yet commonplace, are gaining sophistication, making them increasingly potent and difficult to defend against. These attacks leverage AI’s capacity for learning and adaptation to bypass traditional security measures.
Hypothetical AI-Driven Phishing Campaigns
Sophisticated AI algorithms can analyze vast datasets of user behavior, email patterns, and online interactions to identify individuals most susceptible to phishing attacks. This allows for highly targeted and personalized phishing campaigns, significantly increasing their success rate. For example, an attacker might craft an email seemingly from a trusted contact, leveraging insights into the recipient’s professional network and personal interests to make the message appear authentic.
Automated Malware Generation and Deployment
AI can automate the creation of sophisticated malware variants, adapting to evolving security defenses in real time. This dynamic nature makes it extremely difficult to identify and counter these threats. Imagine malware that can modify its code structure to avoid detection by signature-based antivirus software, or malware that adapts its attack vector based on the victim’s network configuration.
Israel’s recent warning about AI-powered cyberattacks highlights a critical need. We’re facing a new frontier in digital threats, and developers need to prioritize robust security measures. This means deploying AI code safety goggles, like those discussed in Deploying AI Code Safety Goggles Needed , to proactively identify and fix vulnerabilities before they become exploitable. Ultimately, a proactive approach is crucial to mitigating the risks of these emerging threats.
AI-Powered Denial-of-Service (DoS) Attacks
AI can optimize and scale DoS attacks, generating traffic patterns that overwhelm targeted systems. This approach can be more difficult to mitigate than traditional DoS attacks, as the AI-driven attacks can adapt to any countermeasures employed. A hypothetical example might involve an AI program that learns the weaknesses of a specific network infrastructure, generating increasingly sophisticated attack patterns to disrupt services.
Table: Progression of an AI Cyberattack
| Stage | Description |
|---|---|
| Phase 1: Reconnaissance | The attacker utilizes AI to gather information about the target’s network, systems, and personnel. |
| Phase 2: Vulnerability Analysis | AI analyzes the collected data to identify vulnerabilities in the target’s security posture. |
| Phase 3: Attack Planning | Based on the analysis, the AI formulates a customized attack strategy. |
| Phase 4: Attack Execution | The AI deploys the attack, adapting to any countermeasures. |
| Phase 5: Data Exfiltration | AI manages and facilitates the extraction of sensitive data from the victim’s systems. |
Characteristics of Sophisticated AI-Driven Attacks
These attacks exhibit several key characteristics:
- Adaptability: The attacks adjust to security measures in real-time, making them challenging to stop.
- Stealth: They often bypass traditional detection methods, making them difficult to identify.
- Scalability: The AI can quickly and efficiently scale attacks to impact numerous targets simultaneously.
- Personalization: AI enables highly tailored attacks, increasing the likelihood of success.
Methods Used to Create AI-Driven Attacks
Attackers employ various techniques to develop these sophisticated attacks:
- Machine Learning: Algorithms are trained on vast datasets of attack patterns and security measures to identify vulnerabilities and craft effective exploits.
- Deep Learning: Neural networks can analyze complex data patterns to identify anomalies and create new attack methods.
- Evolutionary Algorithms: These algorithms mimic natural selection to optimize attack strategies, adapting them to real-time conditions.
Motivations Behind AI-Based Attacks
The motivations behind these types of attacks can vary widely:
- Financial Gain: Stealing sensitive data or disrupting services to cause financial losses.
- Espionage: Acquiring intellectual property or sensitive information for competitive advantage.
- Political Motivations: Disrupting infrastructure or causing damage to a nation-state or organization.
- Cyber Warfare: Part of a larger conflict between nation-states or organizations.
Stages of an AI-Based Attack
“An AI-driven attack typically progresses through distinct stages, each leveraging the capabilities of AI to enhance its efficiency and effectiveness.”
- Reconnaissance: The attacker collects information about the target’s systems and vulnerabilities. This stage is often automated and highly efficient.
- Vulnerability Exploitation: The attacker uses AI to identify and exploit vulnerabilities in the target’s security infrastructure. The AI adjusts its approach based on real-time feedback.
- Attack Execution: The attacker launches the attack using optimized methods determined by the AI.
- Data Exfiltration: The attacker uses AI to identify and exfiltrate sensitive data from the target’s systems.
- Cleanup: The attacker removes traces of the attack, making it difficult to detect.
Last Recap
Israel’s warning underscores the urgent need for global collaboration in developing and implementing robust defenses against AI-driven cyberattacks. The potential for devastating consequences demands proactive measures, encompassing international cooperation, government-led initiatives, and private sector engagement. Ultimately, the world must address this emerging threat before it becomes a reality, ensuring the safety and stability of the digital world.
Expert Answers: Israel Issues Warning On Ai Cyber Attacks
What specific types of AI attacks does Israel warn about?
Israel’s warning encompasses a range of sophisticated AI-powered attacks, including automated phishing campaigns, targeted malware deployments, and potentially even the use of autonomous weapons systems. The attacks could exploit vulnerabilities in critical infrastructure and target specific sectors like finance and energy.
What are the potential economic impacts of these attacks?
AI cyberattacks could cause significant economic damage, disrupting supply chains, crippling financial institutions, and damaging critical infrastructure. The potential for widespread economic disruption necessitates proactive measures to prevent such attacks.
How does Israel’s approach to AI cyber threats compare to other countries?
A table comparing and contrasting Israel’s approach with other countries’ strategies would be a valuable addition to this analysis, highlighting potential areas for collaboration and knowledge sharing.
What proactive measures can countries take to counter AI cyber threats?
Proactive measures include strengthening cybersecurity infrastructure, investing in AI-driven threat detection systems, and fostering international cooperation to share information and best practices.