security
-
Data Security

LA County Data Breach Impacts 200,000
Los angeles county suffers data breach impacting 200000 individuals – Los Angeles County suffers data breach impacting 200,000 individuals. This…
Read More » -
Cybersecurity
Bitglass Security Spotlight GCP, Synack, Drupal Defense
Bitglass security spotlight google synack drupal integration offers a powerful approach to bolstering security for Drupal websites hosted on Google…
Read More » -
Security

Belkin Wemo Devices Smartphone Attacks Exposed
Belkin Wemo devices expose smartphones to attacks, opening a potential avenue for hackers to compromise user data and privacy. These…
Read More » -
Technology

Linux Foundations Secure Cloud Consortium
Linux Foundation forms new secure cloud computing consortium, marking a significant step forward in bolstering cloud security. This initiative aims…
Read More » -
Technology

Leaked iOS Source Code Trouble for Apple?
Leaked iOS source code could spell trouble for Apple Inc., potentially exposing vulnerabilities in iPhones, iPads, Macs, and more. This…
Read More » -
Technology

Jewelry to Unlock iPhone, Authenticate Payments
Jewelry to unlock an iPhone or authenticate a digital payment is an intriguing concept, promising a future where our everyday…
Read More » -
International Relations
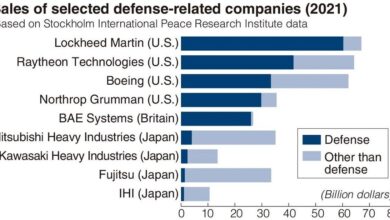
Japan Restricts Foreign Equipment Security Concerns
Japan to restrict the use of foreign equipment in its private sector due to security concerns. This significant move signals…
Read More » -
Technology

Cyber Attack Halts Seattle-Tacoma Airport
Cyber attack disrupts operations at seattle tacoma international airport – Cyber attack disrupts operations at Seattle-Tacoma International Airport, grounding flights…
Read More » -
Security Threats

ISIS Shifts to Cyberattacks After Loss
Isil will shift its focus to cyber attacks after battlefield loss – ISIS will shift its focus to cyber attacks…
Read More » -
Cybersecurity Analysis

Cybersecurity Half Full or Half Empty?
Is the cybersecurity industrys glass half full or half empty – Is the cybersecurity industry’s glass half full or half…
Read More »
