security
-
Cybersecurity

Is Backup the Only Ransomware Blocker?
Is backup the only solution to block ransomware threats? This exploration delves into the critical question of ransomware protection, examining…
Read More » -
Security

iPhone Vulnerability Contactless Payment Fraud
iPhone vulnerability allows hackers to fraudulently make contactless payments, exposing a serious security flaw that could lead to significant financial…
Read More » -
Technology

Intel Processors Recognizing Ransomware at Hardware Level
Intel processors to recognize ransomware attacks at hardware level sets the stage for a fascinating new approach to cybersecurity. This…
Read More » -
Technology

Intel Announces Cloud Security Fears Vanished
Intel announces that cloud security fears have vanished, sparking a wave of excitement and speculation about the future of cloud…
Read More » -
Cybersecurity
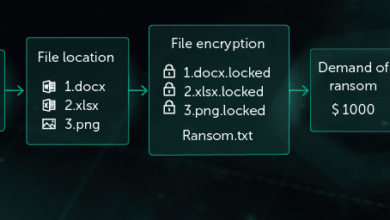
Intel & Check Point Ransomware Defense Partnership
Intel and Check Point software extend partnership for ransomware protection, forging a powerful alliance to combat the escalating threat of…
Read More » -
Cybersecurity

Insider Threats Rise with BYOD
Insider threats are increasing due to byod trend – Insider threats are increasing due to the BYOD trend, creating a…
Read More » -
Cybersecurity

Insider Risk Unconventional Thoughts & Lessons Learned
Insider risk unconventional thoughts and lessons learned – Insider risk: unconventional thoughts and lessons learned. This exploration delves into the…
Read More » -
Software Development
If Youre Only as Strong as Your Allies, Should You Trust Third-Party Code?
If youre only as strong as your allies should you trust third party code – If you’re only as strong…
Read More » -
Computer Security
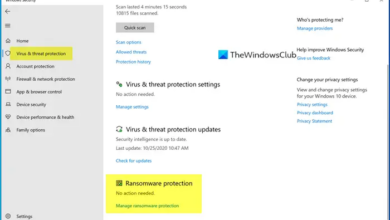
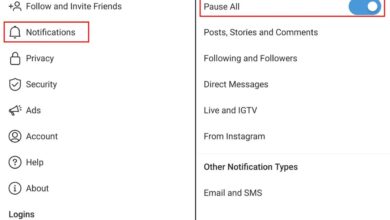
How to Turn on Ransomware Protection on Windows 10
How to turn on ransomware protection on Microsoft Windows 10? This guide dives deep into securing your system from the…
Read More »