vulnerability assessment
-
Cybersecurity

Investigating the Top 10 Application Vulnerabilities
Investigating the top 10 application vulnerabilities is crucial in today’s digital landscape. These weaknesses represent potential entry points for malicious…
Read More » -
Network Security
Hunting for Network Share Recon A Deep Dive
Hunting for network share recon sets the stage for a comprehensive exploration of identifying and analyzing network shares. This in-depth…
Read More » -
Cybersecurity
Hire an Ethical Hacker Now Protect Your Digital Fortress
Hire an ethical hacker now to proactively safeguard your digital assets. Cyber threats are constantly evolving, and neglecting security can…
Read More » -
Cybersecurity

Australia Runs Cybersecurity Health Check on Gov Websites
Australia runs cybersecurity health check on all gov websites and infrastructure – a massive undertaking designed to shore up the…
Read More » -
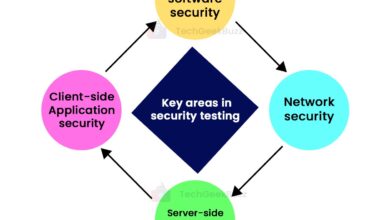
Construction & Safety
A Spell Check Equivalent for Building Security In
A spell check equivalent for building security in? It sounds strange, right? But think about it: spell check catches typos,…
Read More » -
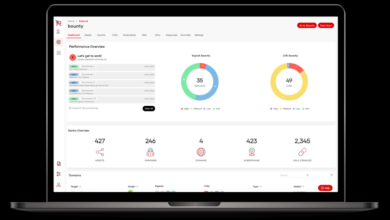
Cybersecurity
End-to-End Security Testing Keep it Simple
End to end security testing keep it simple – End-to-End Security Testing: Keep it Simple – that’s the goal, right?…
Read More »