Vulnerability Management
-
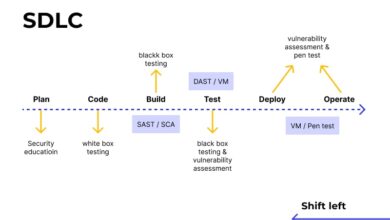
Software Development

Security Should Never Be An Afterthought App Security Testing
Security should never be an afterthought application security testing has been around for a long time but few development teams…
Read More » -
Application Security
AppScans API Scanning DAST, IAST Lunch & Learn
Api scanning with dast and iast in appscans next lunch n learn – API scanning with DAST and IAST in…
Read More » -
Software Development

Secure Your Software with Our App Security Testing Platform
Secure your software with our application security testing platform – it’s a phrase that should resonate with every developer and…
Read More » -
Cybersecurity
It is no secret that secrets scanning is important
It is no secret that secrets scanning is important; in today’s digital landscape, where data breaches are headline news, protecting…
Read More » -
Cybersecurity

Building Resilience with Software Supply Chain Security
Building resilience with software supply chain security is more critical than ever. In today’s interconnected world, software underpins almost every…
Read More » -
Software Development

Demystifying PBOM and SBOM Understanding Key Differences
Demystifying pbom and sbom understanding the key differences – Demystifying PBOM and SBOM: Understanding the key differences is crucial in…
Read More » -
Cybersecurity
Protecting Software Supply Chains with SBOM PBOM
Protecting software supply chains with sbom pbom – Protecting software supply chains with SBOMs (Software Bills of Materials) and PBOMs…
Read More » -
IT Security
ESG Insights for Vulnerability Remediation
ESG insights for vulnerability remediation are no longer a niche topic; they’re a crucial element of responsible business practices. This…
Read More » -
Software Development

Software Composition Analysis SCA Securing Your Code
Software composition analysis sca – Software Composition Analysis (SCA) – it’s the unsung hero of modern software development, quietly safeguarding…
Read More » -
Cybersecurity

Software Supply Chain Exposures Whitepaper A Deep Dive
Software Supply Chain Exposures Whitepaper: Have you ever stopped to think about the hidden vulnerabilities lurking within the software you…
Read More »
