A Comprehensive Guide to Zero-Shot Text Classification and Its Impact on Natural Language Processing
Zero-shot text classification represents a significant leap in the field of artificial intelligence, offering a method to categorize textual data into predefined labels without the requirement of task-specific training data. Traditionally, machine learning models required thousands of labeled examples to understand the nuances of a specific category, such as distinguishing between "technical support" and "billing inquiries" in a customer service setting. However, the advent of large-scale pretrained transformer models has shifted this paradigm, allowing models to leverage their foundational understanding of human language to perform classification tasks on the fly. By treating classification as a reasoning problem rather than a pattern-matching exercise, zero-shot learning enables developers and researchers to deploy functional AI systems in minutes rather than weeks.
The Evolution of Text Categorization: From Rules to Zero-Shot Learning
The journey toward zero-shot classification is rooted in the broader history of Natural Language Processing (NLP). In the early days of computing, text classification relied on rigid, rule-based systems where programmers manually defined keywords and regular expressions. While effective for simple tasks, these systems lacked the flexibility to handle the inherent ambiguity of human language. The 2010s saw the rise of supervised learning, where models like Support Vector Machines (SVM) and later, Recurrent Neural Networks (RNNs), were trained on massive, human-annotated datasets. While highly accurate, the "data bottleneck" became a primary obstacle; the cost and time required to label data for every new niche application were often prohibitive.
The landscape changed dramatically in 2017 with the introduction of the Transformer architecture by Google researchers. This paved the way for models like BERT, GPT, and BART, which were pretrained on vast swaths of the internet. By 2019 and 2020, researchers realized that these models had developed a "semantic map" of language so sophisticated that they could recognize the relationship between a piece of text and a label they had never specifically been trained to identify. This led to the birth of Zero-Shot Learning (ZSL) as a mainstream tool, democratizing access to high-end AI for small-to-medium enterprises (SMEs) that lack the resources for large-scale data annotation.
The Mechanics of Natural Language Inference
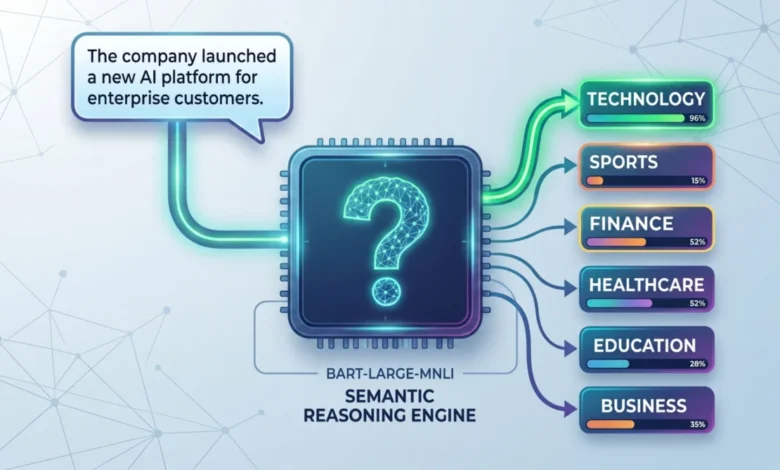
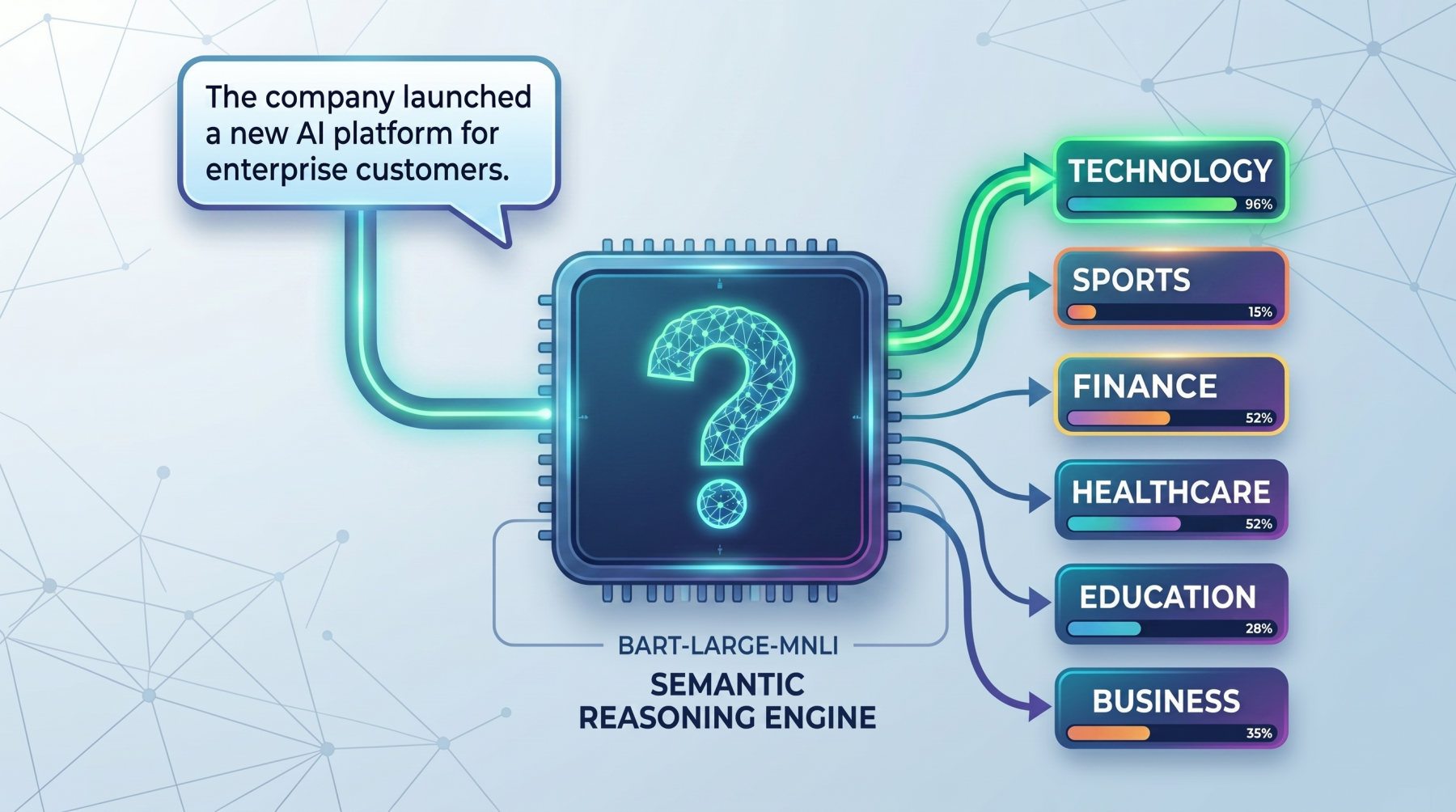
To understand how zero-shot classification functions, one must look at the underlying mechanism of Natural Language Inference (NLI). Unlike traditional classifiers that output a probability distribution over a fixed set of integers (representing classes), zero-shot models like facebook/bart-large-mnli treat the task as a "premise" and "hypothesis" relationship.
In this framework, the input text serves as the "premise." The model then takes each candidate label provided by the user and fits it into a "hypothesis template," such as "This text is about ." For instance, if the input text is a news snippet about a solar flare and the candidate label is "science," the model evaluates the likelihood that the premise ("A solar flare occurred today") entails the hypothesis ("This text is about science").
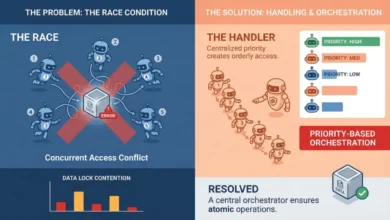
The model evaluates three possible states for each label:
- Entailment: The text supports the hypothesis.
- Neutral: The text neither supports nor contradicts the hypothesis.
- Contradiction: The text directly opposes the hypothesis.
By calculating the softmax of the entailment scores across all candidate labels, the model can rank which label is the most semantically appropriate. This "reasoning" approach allows for immense flexibility; a user can change the labels from "politics" and "sports" to "urgent" and "non-urgent" without ever retraining the underlying model.
Implementing Zero-Shot Classification: A Technical Overview
Modern NLP libraries, most notably the Hugging Face transformers library, have simplified the implementation of zero-shot classification to a few lines of Python code. The process begins with environment setup, typically requiring the installation of torch and transformers.
The standard model for this task is facebook/bart-large-mnli. BART (Bidirectional and Auto-Regressive Transformers) is particularly effective because its architecture allows it to excel at both understanding and generating text. When paired with the Multi-Genre Natural Language Inference (MNLI) dataset, it becomes a powerful engine for zero-shot tasks.
Basic Implementation
A basic implementation involves loading the classification pipeline and passing the text alongside a list of candidate labels. For example, a sentence regarding a company’s AI platform might be tested against "technology," "sports," and "finance." The model returns a dictionary containing the labels and their corresponding confidence scores, usually identifying "technology" with a high degree of certainty (often exceeding 95%).
Multi-Label Classification
In real-world scenarios, a single piece of text often belongs to multiple categories. A news article about a new medical device could reasonably be classified under "healthcare," "technology," and "business." By setting the multi_label parameter to True, the model treats each label as an independent hypothesis. Instead of the scores summing to one, each label is given a score between 0 and 1 based on its individual merit. This is critical for complex routing systems in enterprise environments.
Optimizing with Hypothesis Templates
One of the more nuanced aspects of zero-shot classification is the "hypothesis template." While the default is often "This example is " or "This text is about ," performance can be significantly improved by tailoring the template to the domain. In a sentiment analysis task, a template like "The sentiment of this review is " may yield more accurate results than a generic one. This process, often referred to as "prompt engineering," allows the model to better align its internal semantic weights with the user’s specific intent.
The Economics of Zero-Shot Learning: Supporting Data and Market Impact
The shift toward zero-shot learning is driven as much by economics as it is by technology. According to industry reports, data labeling accounts for up to 80% of the time spent on AI projects. Professional data annotation services can cost anywhere from $1 to $5 per complex label, meaning that a robust dataset of 10,000 samples could cost a company $50,000 before a single line of model code is written.
Zero-shot classification effectively removes this upfront cost. While the computational cost of running a large transformer model like BART is higher per inference than a simple linear model, the "Total Cost of Ownership" (TCO) for many projects is lower because it eliminates the need for expensive data collection and maintenance.
Furthermore, the global NLP market is projected to reach approximately $1.8 trillion by 2030, according to various market analyses. The growth is fueled by the demand for automated customer service and content moderation. Zero-shot models are at the forefront of this growth, as they allow for "cold-start" capabilities—where a system can be operational the same day a new business requirement is identified.
Industry Reactions and Strategic Implications
The technology community has reacted with cautious optimism to the proliferation of zero-shot models. AI researchers have noted that while zero-shot classification is a "game-changer" for prototyping, it is not a silver bullet. Industry experts suggest that zero-shot models should be used to "bootstrap" projects. By using a zero-shot model to label an initial batch of data, companies can then use those labels to train smaller, faster, and cheaper supervised models for long-term production use.
From a strategic perspective, zero-shot classification offers several key advantages:
- Agility: Businesses can respond to market changes by updating classification labels instantly without retraining.
- Scalability: Systems can handle an infinite variety of categories, making them ideal for dynamic environments like social media monitoring.
- Accessibility: Non-experts can utilize powerful AI by simply defining categories in plain English.
However, there are inherent risks. Zero-shot models can inherit biases present in their pretraining data, leading to skewed results in sensitive areas like hiring or legal analysis. Furthermore, "hallucinations"—where a model provides a high confidence score for a label that is objectively incorrect—remain a challenge that requires human-in-the-loop oversight.
Future Outlook and Broader Impact
As transformer models continue to grow in size and efficiency, the gap between zero-shot and supervised performance is narrowing. Future developments are expected to focus on "distillation," where the reasoning capabilities of massive models like BART or GPT-4 are compressed into smaller, mobile-friendly versions.
We are also seeing the rise of "few-shot" learning, a middle ground where providing just three to five examples can dramatically boost a model’s accuracy. This hybrid approach combines the ease of zero-shot learning with the precision of supervised training.
In conclusion, zero-shot text classification is more than just a technical convenience; it is a fundamental shift in how humans interact with machine intelligence. By moving away from rigid datasets and toward semantic reasoning, we are creating AI systems that understand not just the labels we give them, but the language and logic behind those labels. For developers and businesses, the message is clear: the barrier to entry for sophisticated text analysis has never been lower, and the potential for innovation has never been higher.